by Josef Weiss
June 1, 2016
A botnet is a group of computers, often called nodes or zombies, which have been exploited and can be remotely controlled by an attacker, often called a bot-herder. The term “bot,” a derivative of robot, refers to software that can perform tasks with some degree of autonomy. Computers often become nodes within a botnet when malware is installed that allows compromised hosts to establish a command-and-control connection back to the bot-herder. This illicit and often malicious software is usually the result of social engineering attacks, which trick the user into installing the malware. Botnets are frequently used to distribute illegal content, send spam, or attack other computers.
Botnets are easily concealed as they are primarily designed to operate in the background with very little evidence of their existence. However, they can have a significant impact, as many times the attacker can have as much control of the computer as the victims themselves. The botnets’ low profile may allow them to be active and operational for long periods of time before they are detected. Some malware may also contain command-and-control capabilities, allowing them to evolve into botnets over time.
The ability of a botnet to remain stealthy can make defending against them difficult. This dashboard displays active and passive botnet detections, botnet and malicious process indicators, as well as threatlist events, to assist the analyst in determining whether any potential botnet activity is present on the network. Active vulnerability scans with Nessus identify hosts that are being controlled as part of a botnet, as well as web servers that are hosting malicious content associated with botnet propagation. Correlation of logs and sniffed traffic by LCE with known botnet IPs also helps identify systems that are participating in a botnet.
Using the active scanning, agent scanning, passive listening, and host data sensors, SecurityCenter CV can provide a more comprehensive view of devices accessing the network. By practicing continuous monitoring, organizations can more effectively assess risk and identify authorized and unauthorized activity in their network.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Discovery & Detection.
The dashboard requirements are:
- SecurityCenter 4.8.2
- Nessus 6.5.6
- LCE 4.8.0
- PVS 5.0.0
As hosts connect to network, the race begins to identify all the vulnerabilities and assess how each system will affect the network. Only Tenable can automatically analyze information from active scanning, intelligent connectors, agent scanning, passive listening, and host data. Active scanning periodically examines hosts to determine the level of risk posed to the organization. Intelligent connectors leverage other security investments in the environment to integrate security data in order to improve context and analysis. Agent scanning provides the ability to rapidly assess hosts without the need for credentials and to detect hosts that were offline during active scans. Passive listening provides real-time monitoring to collect information about hosts connected to the network and how the hosts are communicating. Host data uses logs, file system activity, and configuration changes to actively monitor host activities and events to identify malicious activity and anomalous behavior.
The dashboard contains the following components:
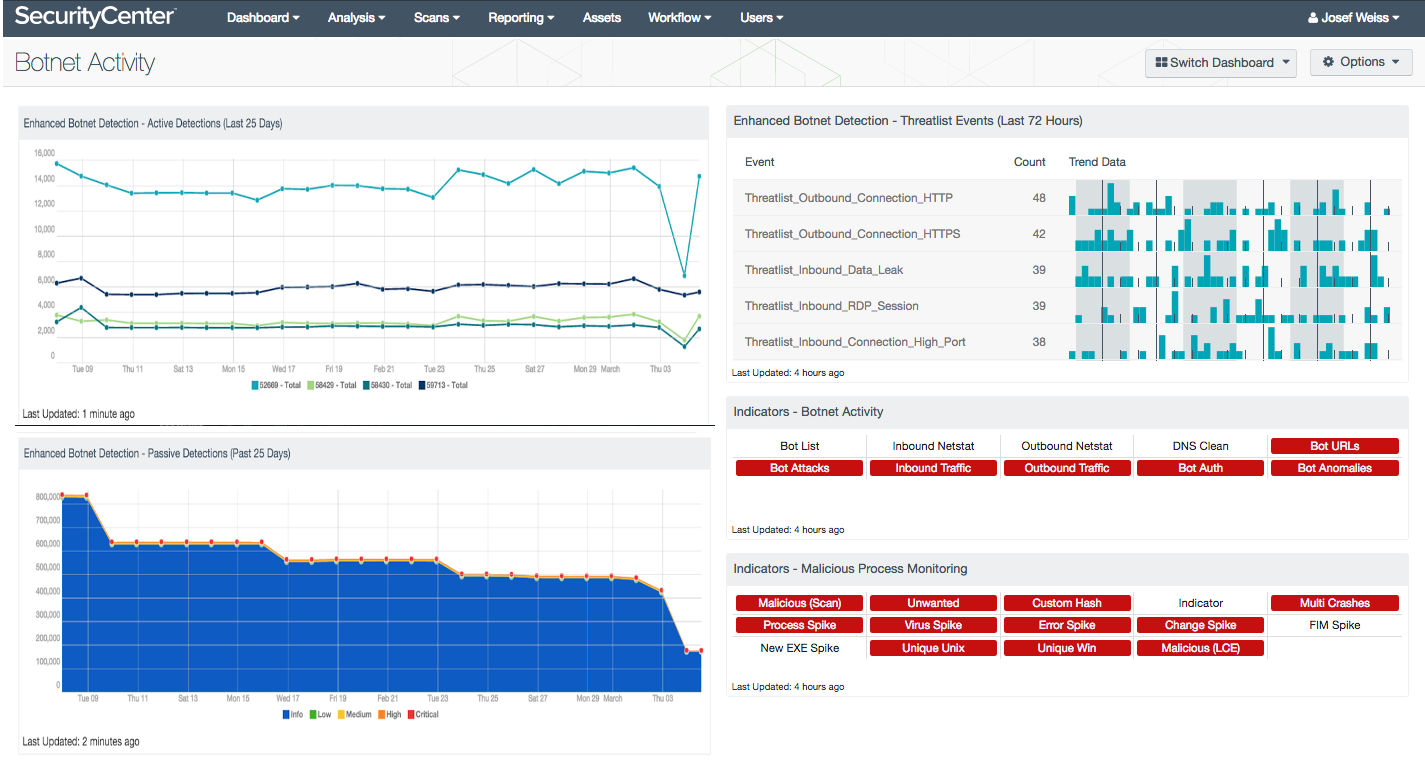
- Indicators - Botnet Activity - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot.
- Indicators - Malicious Process Monitoring - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot. This component is included in dashboards related to the 2015 Verizon Data Breach Investigation Report (DBIR).
- Enhanced Botnet Detection - Passive Detections (Last 25 Days): The Passive Detections (Last 25 Days) area chart depicts the trend of vulnerabilities related to botnet activity over the past 25 days by severity.
- Enhanced Botnet Detection - Active Detections (Last 25 Days): The Active Detections (Last 25 Days) line chart depicts the trend of vulnerabilities related to botnet activity over the past 25 days by plugin.
- Enhanced Botnet Detection - Threatlist Events (Last 72 Hours): The Threatlist Events (Last 72 Hours) table provides a normalized event summary of the threatlist events detected in the past 72 hours by count.