by Josef Weiss
November 12, 2015
A common implementation of firewalls is to protect network devices by analyzing data moving in and out of the organization, restricting unauthorized access and malicious traffic. The firewall barrier is a critical control in effectively monitoring traffic both in and out of an organization.
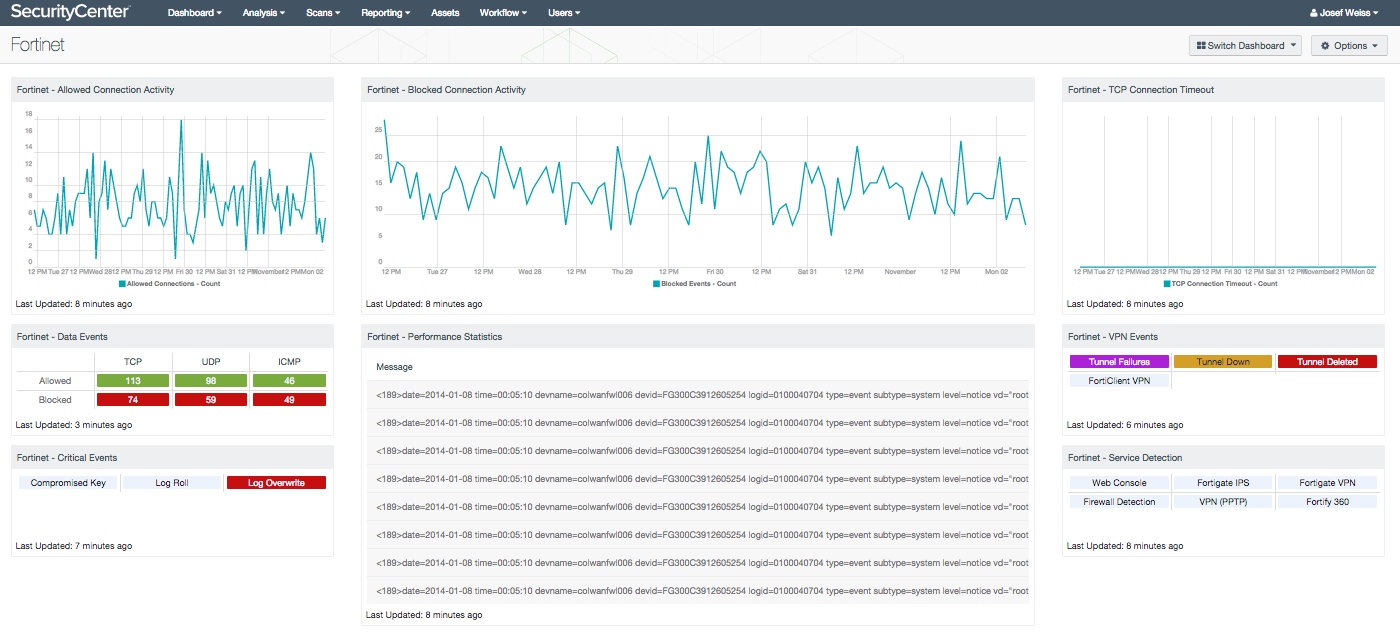
A task common to many security programs is to monitor and analyze logs and events from security devices such as firewalls. Reviewing the organization’s firewall solution ensures the implementation is running smoothly. Monitoring firewall logs is a critical task in security operations, and facilities the identification of security concerns and related issues. The Fortinet dashboard allows security administrators to view a summary status of firewall information, and includes indicators for events, connection activity, and performance alerts in a single location within SecurityCenter. The continuous monitoring of firewalls allows the analyst to quickly identify important event data, without having to log into multiple devices. Problems can be rapidly identified, and a workflow can be easily created to escalate potential concerns.
Using the correlation features of LCE, the Fortinet dashboard highlights the native ability of SecurityCenter to monitor the status of other security products. By collecting this information, a security analyst can review the configuration and traffic status of the firewall without requiring firewall management privileges.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.2
- LCE 4.4.1
- Nessus 6.4.2
- PVS 4.4.0
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. SecurityCenter CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new types of regulatory compliance configuration audits. LCE correlates real-time events, such as DNS queries, and then performs analysis to discover vulnerabilities and Indicators of Compromise (IOC). LCE also has the capability to discover users, operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and other critical infrastructure. SecurityCenter CV allows for the most comprehensive and integrated view of network health.
The collection contains to following components:
- Fortinet - Allowed Connection Activity - This component trends the number of allowed connections over the last seven days as reported by a FortiGate device.
- Fortinet - Blocked Connection Activity - This component trends the number of blocked connections over the last seven days as reported by a FortiGate device.
- Fortinet - TCP Connection Timeout - This component trends the number of TCP session timeouts over the last seven days as reported by a FortiGate device.
- Fortinet - Data Events - This component displays total counts of accepted and blocked TCP, UDP and ICMP connections over the last 24 hours as reported by a FortiGate device.
- Fortinet - Critical Events - This component indicates on several critical events. These events are SSL certificates that have been signed with a compromised key, log rolls, and overwrites.
- Fortinet - VPN Events - This matrix component indicates on Fortinet VPN events, providing alerts to when tunnels fail, go down, or become disabled. There are also active indicators that provide notification if Fortinet VPN Clients are found to be installed on endpoint devices.
- Fortinet - Performance Statistics - This component displays 'Performance Statistic' log data that is forwarded from a FortiGate device. The log data contains information in regard to memory, CPU utilization, and total sessions. Performance stat forwarding must be enabled on the FortiGate device for it to forward these types of events to a logging source.