Detecting the Amazon Web Services Cloud Attack with Nessus
On June 17th, a planned attack against hosting provider, Code Spaces, brought the company to its knees and resulted in the company shutting down its business.
In this case, the attacker gained access to the company’s Amazon EC2 control panel and left messages asking for reply back via email. The response to the email eventually triggered a Distributed Denial of Service (DDoS) attack with the attacker demanding a large fee for resolution.
Once the hosting provider realized that that attacker had access to the AWS control panel, Code Spaces changed passwords to take back control of their panel, but the perpetrator had planned ahead and already created backup logins to the panel. At that point, the attacker began to delete the company’s AWS services including EBS snapshots, S3 buckets, all AMI’s, and EBS instances and several machine instances.
If you are concerned about the exposure to this type of attack in your organization, Nessus includes checks that can help you monitor and detect such events and also report results back to management.
Amazon AWS Best Practices Audit: Nessus recently added AWS audits (Reference TNS Nessus Amazon AWS Auditing Now Available blog) via the Amazon AWS Best Practices Audit Plugin that checks Amazon AWS Infrastructure accounts against the AWS Security Best Practices Guide and IAM Best Practices Guide. It includes 90+ checks for various settings - ranging from proper password policies to suggestions for using multi-factor authentication, roles, and policies. Specifically, the three checks below can be useful in detecting this type of attack:
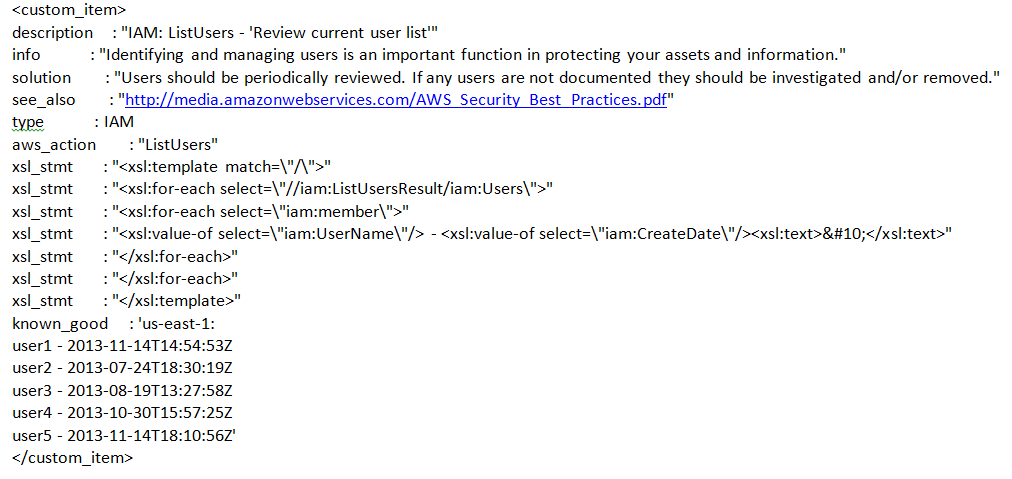
- List of Authorized Users: Identifying and managing authorized users is very important in this case. If users are not authorized, you should investigate and remove appropriately. Furthermore, the “known_good” feature in Nessus helps keep track of authorized users.
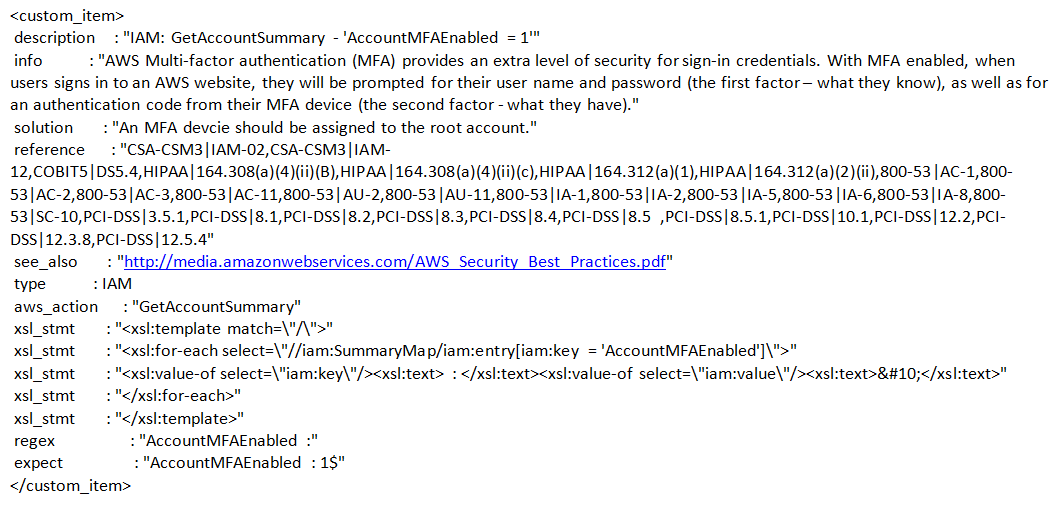
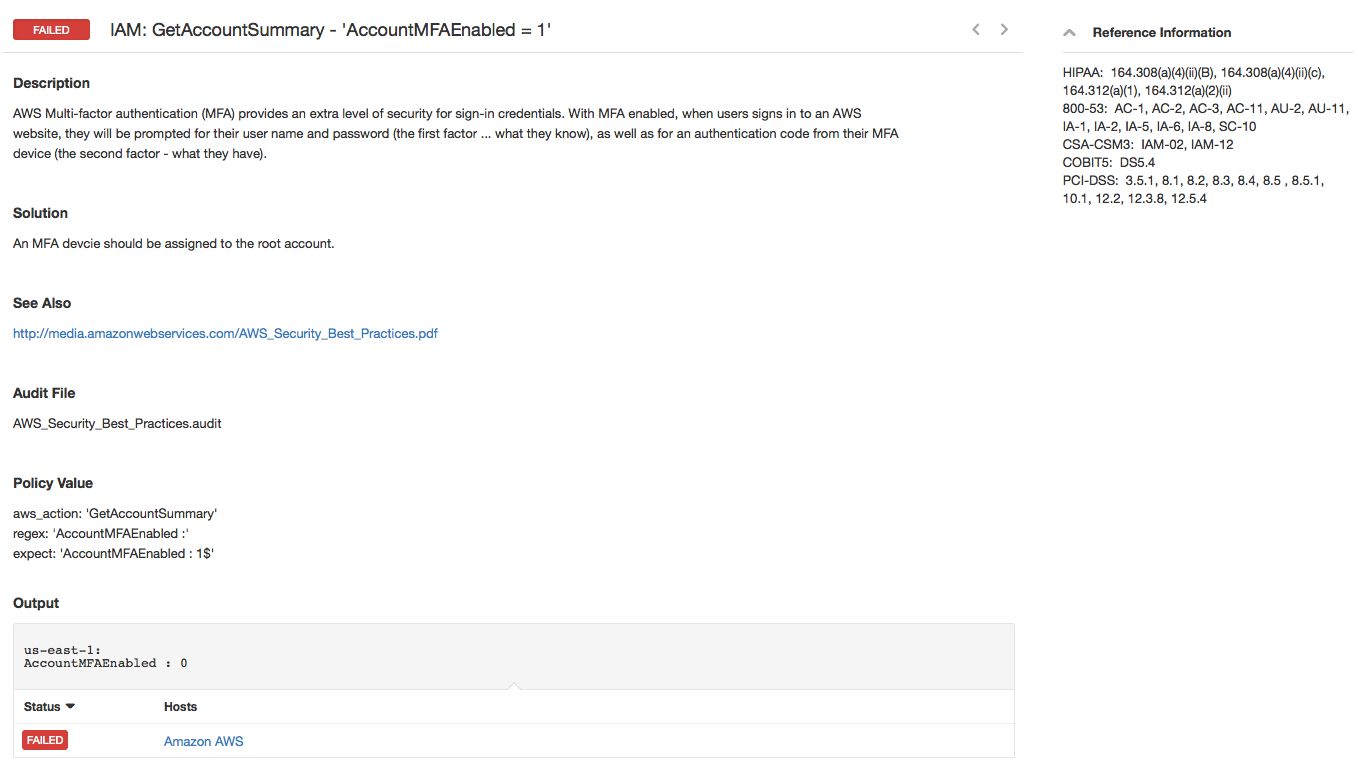
- Multi-Factor Authentication: This validates if Multi-Factor Authentication (MFA) is enabled. With MFA enabled, when user signs in to an AWS website, they will be prompted for their user name and password (the first factor – what they know), as well as for authentication code from their MFA device (the second factor - what they have).
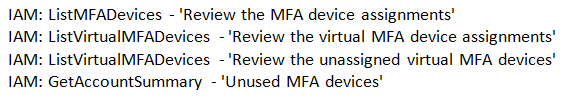
- List of Multi-Factor Devices: In addition, the MFA plugin also provides a list of used/unused multi-factor devices for manual review.
The details of the three checks are provided below. Tenable customers can download the audit file from the Tenable Support Portal.
A combination of these checks would have helped detect, if not thwart, such attacks. While this type of attack can severely impact business operations, it should not deter organizations that have or are planning on using cloud services. However, it reinforces the need for validating and continuously monitoring authorized access and tracking changes to it.
If you would like to learn more about the auditing capabilities of Nessus, click here. If you would like to evaluate Nessus for free, download here.
________________________________________________________________________________
Details of AWS Checks
1) Check for list of allowed users
2) Check for whether Multi-Factor Authentication is enabled
Sample Output for the Multi-Factor Authentication
3) List of used/unused Multi-Factor devices for manual review
Attacks such as these, remind us that just because our workflow has moved to the cloud, our security challenges don’t go away. In fact the stakes just get higher. There is a reason best practice guidelines exist. And its just common sense to take steps such as using multi-factor authentication, reviewing the list of users and adhering to other best practice recommendations regardless of the size of your infrastructure. One bad move could be the difference between being online or offline.
Related Articles
- Cloud
- Nessus
- Threat Intelligence
- Threat Management
- Vulnerability Management



