Vulnerabilities can be found in every part of an organization’s infrastructure including routers, servers, firewalls, firmware, and software. Many of these vulnerabilities can include exploits that can allow for attackers to gain control over critical systems and data, and pivot to other systems across the enterprise. This report provides a summary of the exploitable vulnerabilities passively detected by Nessus Network Monitor (NNM), which can be used to compare the effectiveness of patch management efforts, and whether existing security controls need to be modified.
Once an exploitable vulnerability is discovered on a system, attackers now have a window of opportunity to exploit that vulnerability and gain access to critical systems. In order to effectively patch systems, organizations must implement a continuous scanning and remediation strategy. Most vulnerability scanning tools used by organizations only detect vulnerabilities found during each scan, but fail to detect vulnerabilities from transient devices missed between scans.
NNM provides organizations with the ability to capture vulnerability data from hosts that were offline during active scans. Using passive listening, organizations will be able achieve a more consistent and effective way to monitor for vulnerabilities on transient devices such as mobile devices, laptops, and virtualized systems. The sooner analysts know when a system has an exploitable vulnerability, the sooner security teams patch the vulnerability or deploy additional security controls until a patch has been released.
Information presented within this report includes a high-level overview of vulnerabilities passively detected by NNM. Elements presented within this report include the top exploitable vulnerabilities, and is sorted to highlight the most vulnerable hosts first. Analysts will be able to monitor subnets for exploitable vulnerabilities, which can highlight whether systems are being patched in a timely manner. This data can also be used by security teams to identify vulnerabilities on outdated or unsupported software where a patch may not be available. Using this information, additional security controls can be applied to compensate and reduce overall risk to the organization.
This report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Monitoring. The report requirements are:
- Tenable.sc 5.4.2
- NNM 5.2.0
Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist an organization in knowing, managing, and securing the network. Passive listening collects data to continuously monitor traffic and collect information about services and network devices. With more supported technologies than other vendors, Tenable.sc CV is able to analyze vulnerabilities and collected logs from a wide range of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure devices. Tenable.sc CV provides an organization with the most comprehensive view of the network, and the intelligence needed to safeguard critical assets and sensitive data.
The following chapters are included within this report:
- Executive Summary: The Executive Summary chapter presents an overview of exploitable vulnerabilities that have been passively detected by NNM. Many organizations use automated patch management solutions to patch systems within their network. Unfortunately, some use a “set it and forget it” strategy, and assume all of their patches will be applied properly. Organizations still need to continuously scan, test, patch, and rescan their systems to ensure that patches are applied. Information presented in this chapter will alert organizations to most vulnerable subnets on the network.
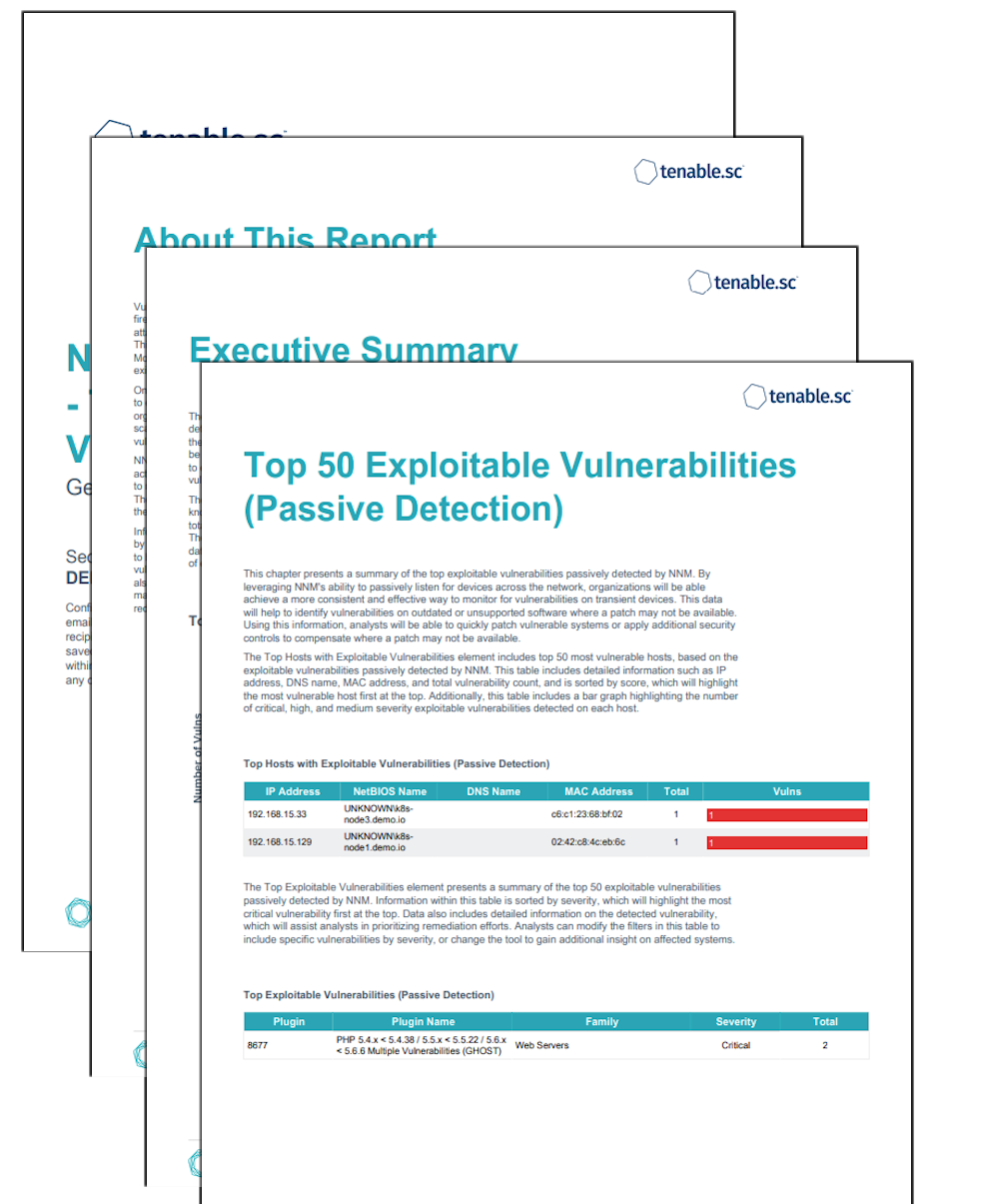
- Top 50 Exploitable Vulnerabilities: This chapter presents a summary of the top exploitable vulnerabilities passively detected by NNM. By leveraging NNM's ability to passively listen for devices across the network, organizations will be able achieve a more consistent and effective way to monitor for vulnerabilities on transient devices. This data will help to identify vulnerabilities on outdated or unsupported software where a patch may not be available. Using this information, analysts will be able to quickly patch vulnerable systems or apply additional security controls to compensate where a patch may not be available.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success