by Cody Dumont
September 16, 2015
With vulnerabilities gaining more visibility in the news, executives and management need to be briefed at least monthly on status updates and mitigations. Tenable.sc Continuous View has the ability to track vulnerabilities as they are discovered on the network and when they are mitigated. This report provides the security operations team with an easy-to-understand report for managers to monitor progress.
Tenable.sc provides organizations with an easy-to-understand platform to collect vulnerability information using three methods: active, passive, and log collection. After the data is collected, the date that a vulnerability is initially discovered and when the vulnerability is remediated can be tracked and reported on. This report provides a high-level executive review of vulnerability detection over the past 30 days.
This report provides executive-level directors and managers with a detailed understanding of the vulnerability risk management program via a series of trend graphs, charts, tables, and other reporting components. A CISO can use this report in monthly meetings to communicate the status of current risk levels to other members of the organization.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the Tenable.sc Feed under the category Executive. The report requirements are:
- Tenable.sc 4.8.2
- Nessus 8.5.1
Tenable.sc CV enables the organization to react to advanced threats, zero-day vulnerabilities and new forms of regulatory compliance. By providing a unique combination of detection, reporting, and pattern recognition utilizing industry-recognized algorithms and models, Tenable.sc CV can become the cornerstone to any successful security program. Taking a proactive approach to continuous network monitoring, Tenable.sc CV identifies the biggest risks across the entire enterprise. Tenable.sc CV scales to meet future demands of monitoring virtualized systems, cloud services, and the proliferation of devices.
Chapters
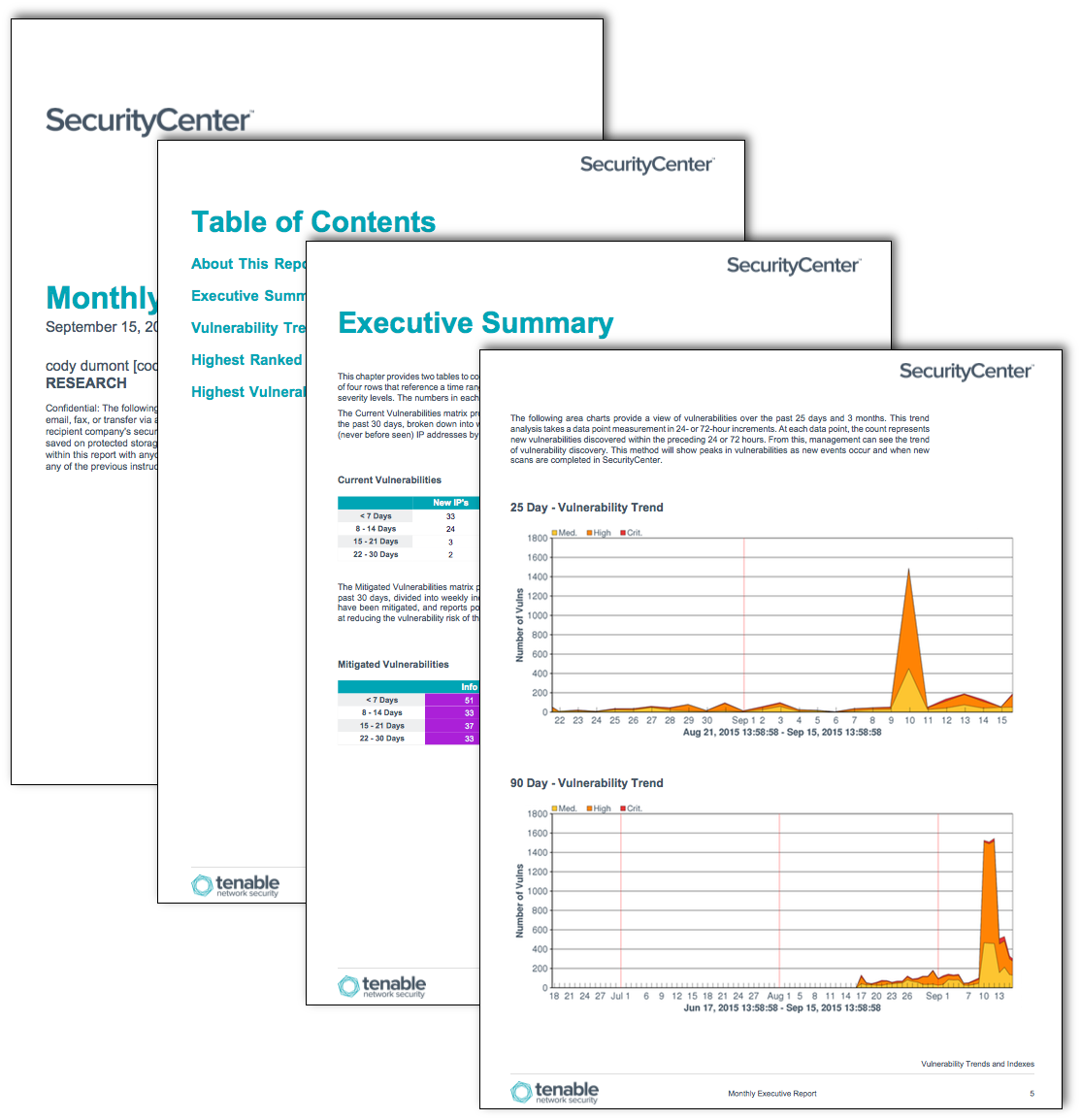
Executive Summary: This chapter provides two matrices to communicate new vulnerabilities and mitigated risk. Each matrix is comprised of four rows that reference a time range in which vulnerabilities are discovered, and columns that indicate their severity levels. The numbers in each cell indicate the number of hosts that match the respective query.
Vulnerability Trends and Indexes: This chapter provides a series of pie charts, area charts, and line graphs that depict the vulnerability status over the past 30 days. This information provides management with a visual representation of new vulnerabilities over the past 30 days.
Highest Ranked Assets: This chapter provides a summary of the top 10 assets on the network based on total vulnerabilities found. The data will help management see vulnerabilities based on similar devices or operating systems. Assets can be used to group similar devices together, or devices with some attribute in common.
Highest Vulnerable Systems in the Network: This chapter provides a summary of the top 10 most vulnerable systems on the network or in an asset group based on total critical severity vulnerabilities found. The data will help management see the systems that require the most immediate attention.