by Ron Gula
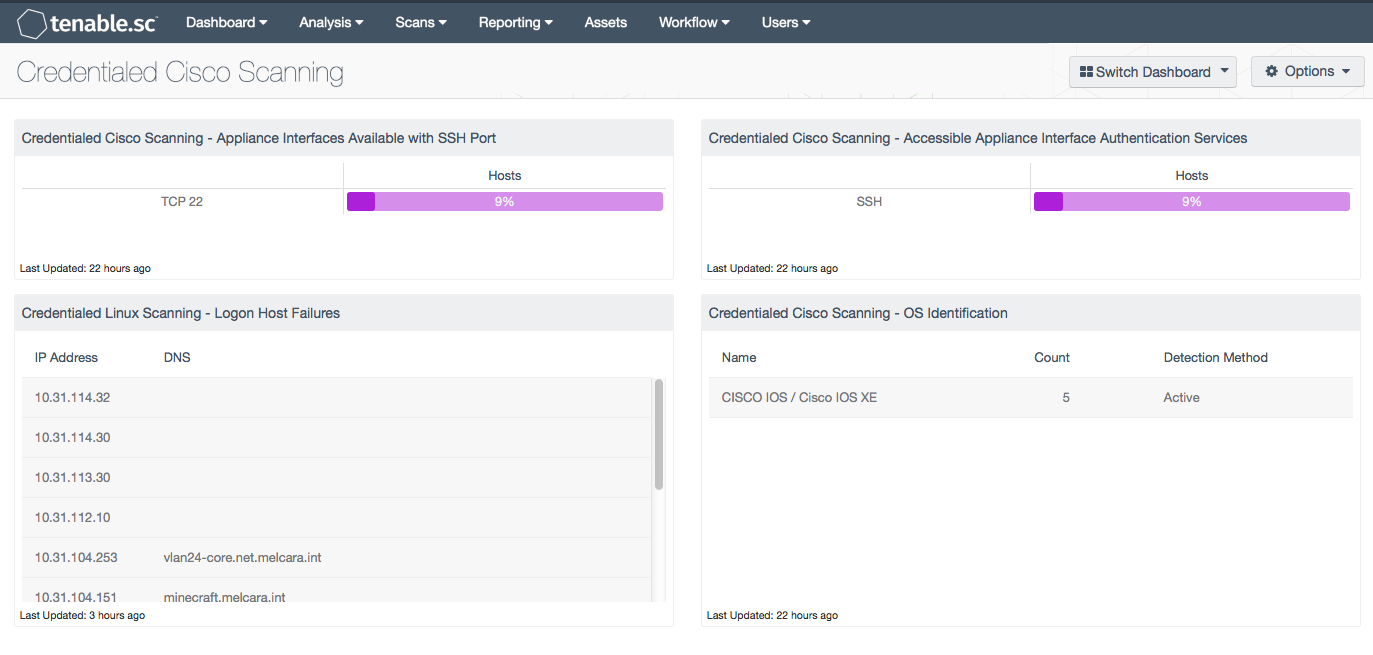
Monitoring the status of Cisco credentialed scanning is important for supporting both patch and compliance auditing of Cisco systems. Tenable.sc Continuous View (CV) has the ability to perform credentialed scans on Cisco appliances, thus increasing the accuracy of the collected data. This dashboard monitors the results of credentialed scans of Cisco appliances.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Monitoring.
The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.4.0
- NNM 5.9.0
When rolling out Cisco credentialed scanning for the first time across an enterprise, one important task is to monitor systems that failed authentication. An organization’s security team should continue to monitor the success of credentialed scanning on an ongoing basis. Monitoring the environment in this manner helps to detect changes in the network that might disrupt credentialed scanning.
The filters used in this dashboard attempt to filter out Cisco related devices using the vulnerability text search. The dashboard consists of four components that leverage the following plugins, which must be enabled during a credentialed scan:
- 1 NNM OS Detection
- 10267 SSH Server Type and Version Information
- 11936 Nessus OS Identification
- 21745 Authentication Failure - Local Checks Not Run
The “Credentialed Linux Scanning - Logon Host Failures” component is reused from the “Credentialed Linux Scanning” dashboard. This component should be edited by adding the “Cisco Devices” dynamic asset to the filter. This will ensure that only Cisco devices are present in the table. Further information can be found at Using Assets with Dashboards How-To Guide.
Tenable.sc Continuous View (CV) identifies the biggest risks across the entire enterprise, and Tenable’s products allow for the most comprehensive and integrated view of network health. Nessus and Tenable.sc are continuously updated with information about advanced threats and zero-day vulnerabilities, as well as new types of regulatory compliance configuration audits, allowing organizations to respond to new threats as they emerge.
Components
Credentialed Cisco Scanning - Appliance Interfaces Available with SSH Port: This matrix component indicates the percentage of Cisco hosts with vulnerabilities discovered on TCP port 22 (SSH). Nessus uses Secure Shell (SSH) for credentialed scans on Cisco devices. Nessus supports three types of authentication methods for use with SSH: username and password, public/private keys, and Kerberos. If SSH servers are running on another port, the scan policies will need to be modified, and the filter in this matrix will need to be modified to reflect the correct SSH service port.
Credentialed Linux Scanning - Logon Host Failures: This table displays systems that failed SSH login for credentialed scans. If the resources are available, then the Nessus scanner can enumerate software and installed packages. If the login fails or the login session does not provide the necessary resources, then authentication will fail. The authentication failure status is provided by plugin 21745 reporting a problem. This filter in this component uses a regular express to exclude SMB login failures, which helps eliminate false positives of Windows login failures.
Credentialed Cisco Scanning - Accessible Appliance Interface Authentication Services: This matrix component highlights the percentage of Cisco hosts that are accessible via the SSH service detected by plugin 10267. While performing patch and configuration auditing, Tenable recommends leveraging the Netstat scanner, used via SSH, to considerably speed up and in some cases improve port scan accuracy. The “SSH Server Type and Version Information” (plugin 10267), detects the SSH server type and version information by sending an empty authentication request. This plugin enumerates the version by collecting banner information from the SSH session or other methods. The component uses the keyword “cisco” within the vulnerability text to identify Cisco devices.
Credentialed Cisco Scanning - OS Identification: This table component displays the various Cisco appliances being audited with credentialed scans. This table is sorted by OS count and displays the OS version, count, and detection method. This information is useful to an analyst who needs to know the number of Cisco platforms that are being scanned in the network environment. This component filters using passive and active plugins to locate all Cisco systems. The OS Identification plugins use several techniques to identify the OS, with differing levels of confidence. This component uses the vulnerability text string “cisco” in conjunction with plugin IDs.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success