by Cody Dumont
In the early days of the Internet, vulnerabilities were not publicly known or identifiable. In 1999, the information security industry endorsed the importance using a common format in identifying vulnerabilities, thus the Common Vulnerabilities and Exposures (CVE®) was created. Since 1999, the adoption of CVE has grown from 29 organizations to over 150 organizations. Tenable’s Renaud Deraison and Marcus Ranum have been past members of the CVE Editorial board. Tenable products were first CVE Compatible in 2004, and currently Tenable.sc, Nessus and the Nessus Network Monitor are compatible. Tenable continues to lead the security industry in vulnerability management and continuous network monitoring by embracing accepted standards such as CVE.
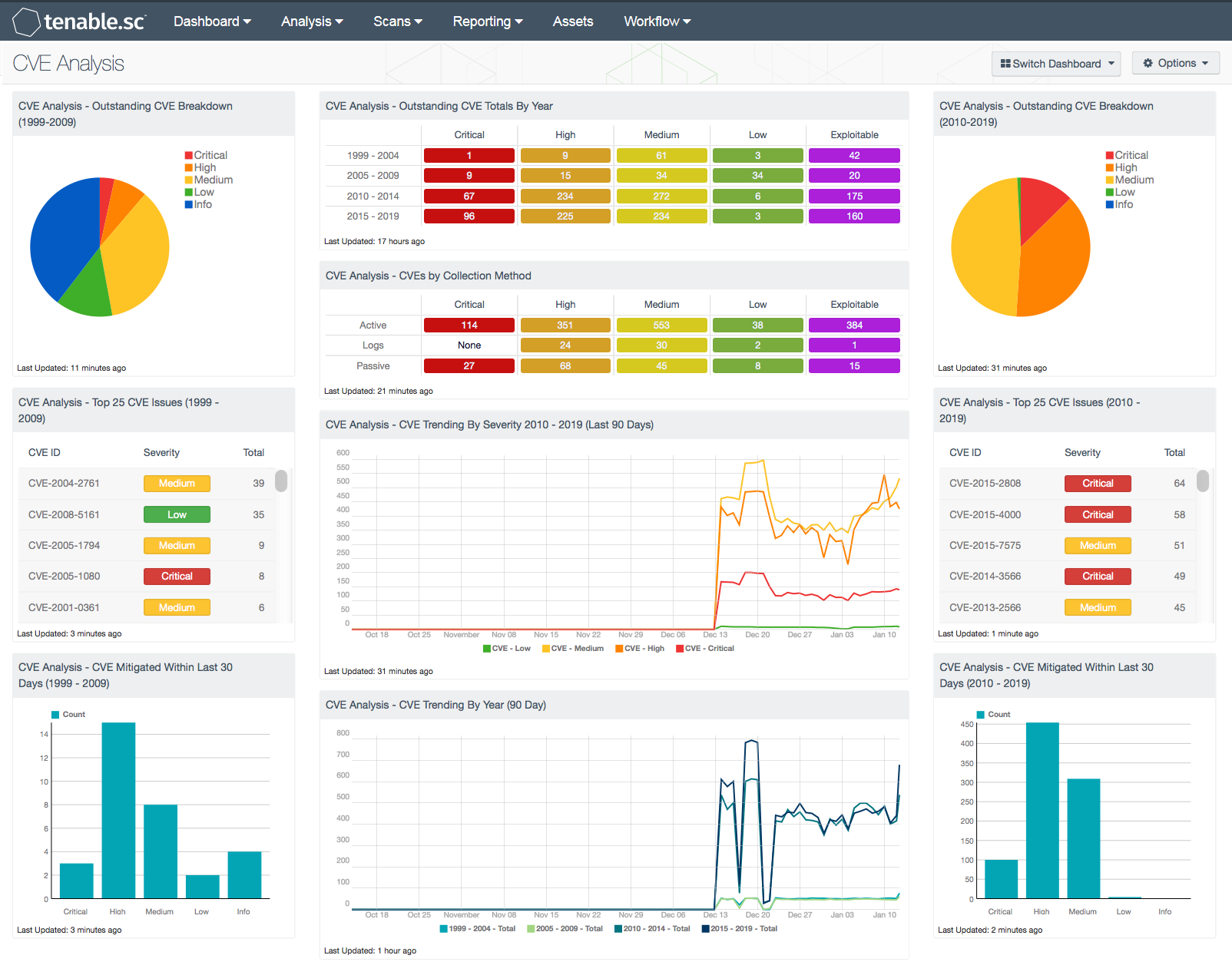
Tenable.sc Continuous View (CV) utilizes the CVE program to reference each of the vulnerabilities detected by Nessus and the Nessus Network Monitor (NNM). Logs collected from the Log Correlation Engine (LCE) are analyzed for vulnerabilities and where applicable the associated CVE identifier is applied. The CVE identifiers can be used through Tenable.sc for reporting, asset identification, risk management, and threat mitigation. The CVE Analysis dashboard helps to identify vulnerabilities by their CVE identifiers from 1999 to 2019.
CVE is a widely used industry standard for identifying vulnerabilities across software vendors and vulnerability management systems. Using CVE identifiers to identify vulnerabilities allows organizations to easily target affected systems and software for remediation. As vendors provide patches for widespread vulnerabilities such as HeartBleed and ShellShock, many new plugins are released. The task of tracking vulnerabilities is simplified by using CVE identifiers, as the CVE identifiers for vulnerabilities remain the same even as new patches and plugins are released. Using CVE is a very flexible and useful method of detecting vulnerabilities to assist in the risk management process.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- Tenable.sc 4.8.2
- Nessus 8.6.0
- LCE 6.0.0
- NNM 5.9.0
Tenable provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. Tenable.sc offers organizations a unique peace of mind by identifying their biggest threats and enable them to respond quickly. Tenable.sc Continuous View (CV) provides a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. Tenable.sc CV combines active scanning, log analysis, and deep packet inspection to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities.
Components
CVE Analysis - Outstanding CVE Breakdown (1999-2009): This component displays a severity summary of the current vulnerabilities identified by CVE from 1999 to 2009. Using the CVE filter and the Severity Summary tool, this pie chart provides an overview of vulnerabilities linked to CVE identifiers from 1999 to 2009. The color of each severity is displayed in the legend to the right of the chart.
CVE Analysis - Top 25 CVE Issues (1999 - 2009): This table lists the top 25 CVE identifiers discovered on the network and the total systems affected. The table uses the CVE summary tool and the CVE filter to identify the top 25 CVEs identified between 1999 and 2009. The table is sorted using the total vulnerability count column.
CVE Analysis - CVE Mitigated Within Last 30 Days (1999 - 2009): The bar chart uses the severity summary tool and CVE filters against the Mitigated database to identify remediated vulnerabilities. The filter targets CVEs identified from 1999 to 2009. The chart is sorted by severity.
CVE Analysis - Outstanding CVE Totals By Year: This matrix provides a breakdown by CVE year and severity. The filters used in each cell contain the CVE identifier strings for the year that the CVE was identified and cross-mapped to a severity level. The last column checks for vulnerabilities that are known to be exploitable. The exploitable column is purple, and other columns map the colors to severity: red is critical, orange is high, yellow is medium, and green is low. The last row filters for CVEs through 2019.
CVE Analysis - CVEs by Collection Method: This matrix provides a breakdown by collection method and severity. The filters used in each cell contain the CVE identifier to first identify vulnerabilities with CVEs and then cross-mapped to plugin type and severity. The plugin type defines the method used by Tenable.sc to collect the data. The “Active” plugin type refers to Nessus scan data, “Passive” is for data collected with NNM, and “Logs” are Event vulnerabilities detected through log analysis using LCE. The exploitable column is purple, and other columns map the colors to severity: red is critical, orange is high, yellow is medium, and green is low.
CVE Trending By Severity 2010 - 2019 (Last 90 Days): This line chart provides a severity summary of vulnerabilities detected over the past 90 days with CVE identifiers after 2010. The filter uses the CVE ID and the severity for low, medium, high, and critical. The values calculated at each data point provide a count of vulnerabilities over the previous 3 days, which gives a more accurate view of the change in data.
CVE Analysis - CVE Trending By Year (90 Day): This line chart provides a severity summary of vulnerabilities detected of the past 90 days grouped by CVE identifier. The filter uses the CVE ID and the severity for low, medium, high, and critical. The values calculated at each data point provide a count of vulnerabilities over the previous 3 days, which gives a more accurate view of the change in data.
CVE Trending by Year - Outstanding CVE Breakdown (2010-2019): Using the CVE filter and the Severity Summary tool, this pie chart provides an overview of vulnerabilities linked to CVE identifiers from 2010 to 2019. The color of each severity is displayed in the legend to the right of the chart.
CVE Analysis - Top 25 CVE Issues (2010 – 2019): This table lists the top 25 CVE identifiers discovered on the network and the total systems affected. The table uses the CVE summary tool and the CVE filter to identify the top 25 CVEs identified between 2010 and 2019. The table is sorted using the total vulnerability count column.
CVE Analysis - CVE Mitigated Within Last 30 Days (2010 - 2019): The bar chart uses the severity summary tool and CVE filters against the Mitigated database to identify remediated vulnerabilities. The filter targets CVEs identified from 2010 to 2019. The chart is sorted by severity.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success