Tenable Responds to CVE-2015-0204: FREAK Vulnerability
It seems that in recent history, the SSL library continues to give security teams plenty of opportunities to interface with systems/application administrators and vendors to upgrade SSL in their environments. The latest vulnerability to impact SSL is CVE-2015-0204, known in the media as "FREAK," short for Factoring RSA EXPORT Keys. FREAK can facilitate a man-in-the-middle attack and force a browser to export a weak 512-bit key, which can be factored in just a few hours. On January 8, 2015, Openssl.org posted the vulnerability with a severity of Low in its security advisory. However, this vulnerability has gained attention most recently when a Washington Post article cited a former U.S. government policy that forbade the export of strong encryption. While this issue impacts all versions of OpenSSL, other software titles that do not properly handle the use of weak algorithms could also be affected. A fix for FREAK in OpenSSL is available as of OpenSSL v1.0.2. Other vendors are also making SSL updates available.
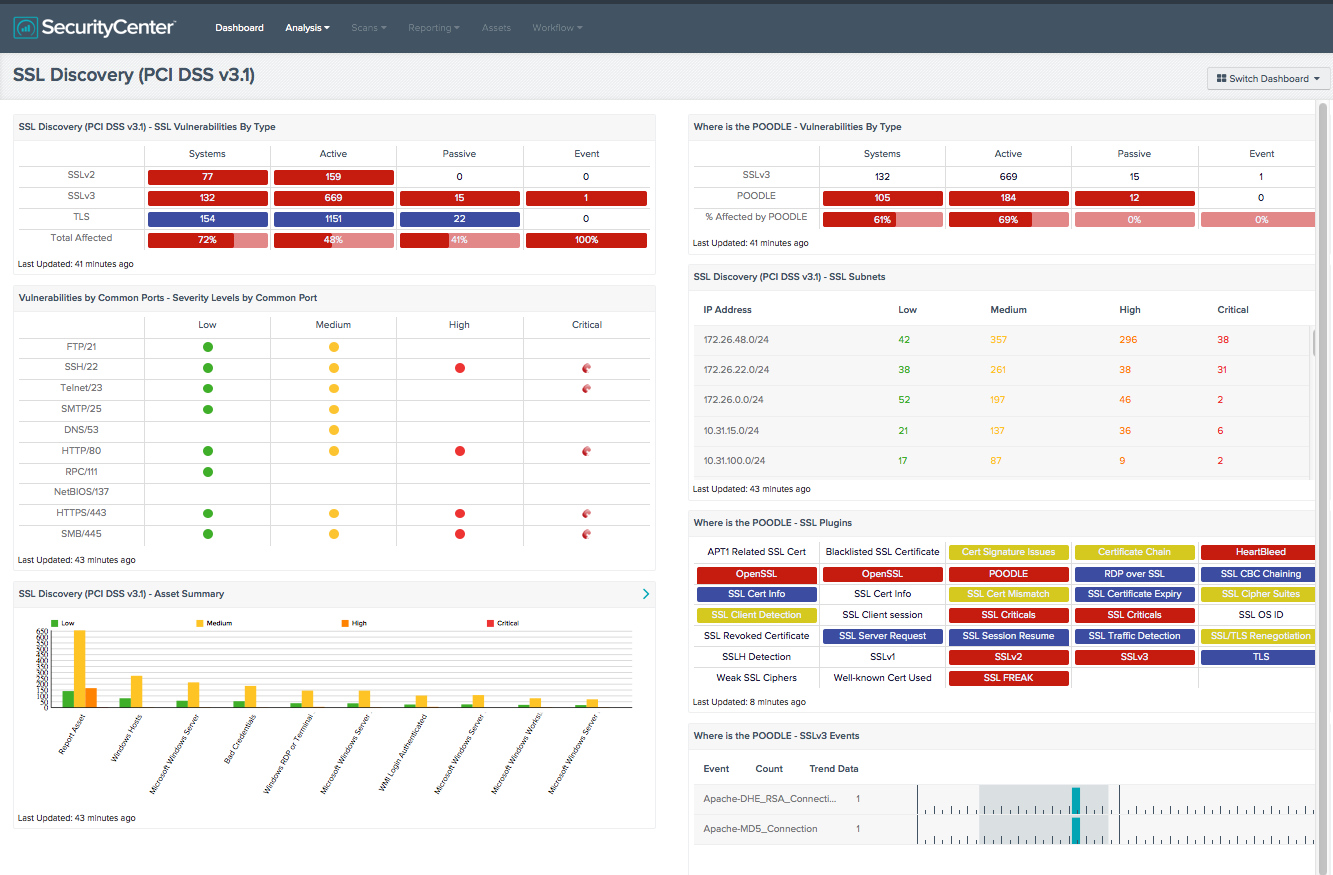
SecurityCenter dashboard
While OpenSSL is prevalent and the impact to operations teams can be significant, there is no reason to freak out; Tenable already has you covered! A SecurityCenter Continuous View™ SSL Discovery dashboard is available for tracking SSL usage in your environment. We have updated the components to specifically call out CVE-2015-0204 to make it even easier to track its impact and remediation.
Nessus plugins
When you scan your environment for FREAK utilizing Nessus®, be sure to look at these plugins:
- 26928: SSL Weak Cipher Suites Supported
- 81606: SSL/TLS RSA-EXPORT <= 512-bit Cipher Suites Supported (FREAK) (newly released)
As always, you can also search for CVE-2015-0204 on our Nessus Plugins page to find the latest Nessus plugins.
This blog will be updated as events warrant.
- Dashboards
- Nessus
- OpenSSL
- Plugins
- SecurityCenter