New Nessus Plugins Audit Your Patch Management System Effectiveness
Integrating with Patch Management
In December 2011, Tenable announced that Nessus could integrate with many popular patch management solutions. Initial support was offered for Red Hat Network Satellite server, Microsoft WSUS / SCCM, and VMware Go. More recently, support was added for IBM Tivoli Endpoint Manager (TEM) for Patch Management. Integration with patch management solutions means Nessus and SecurityCenter can collect information about patches from systems without requiring credentials to the targeted hosts themselves.
Today, two new plugins extend our previous integration to automatically cross-reference vulnerabilities from credentialed patch audits with patch information from your patch management solution, reporting discrepancies in a single report.
[video:http://youtu.be/nOMO6rhPGuQ]
This video explains how Nessus integrates with your patch management solutions, including some of the problems it will uncover, benefits of integration, and a quick demonstration.
Nessus vs. Patch Management Solutions
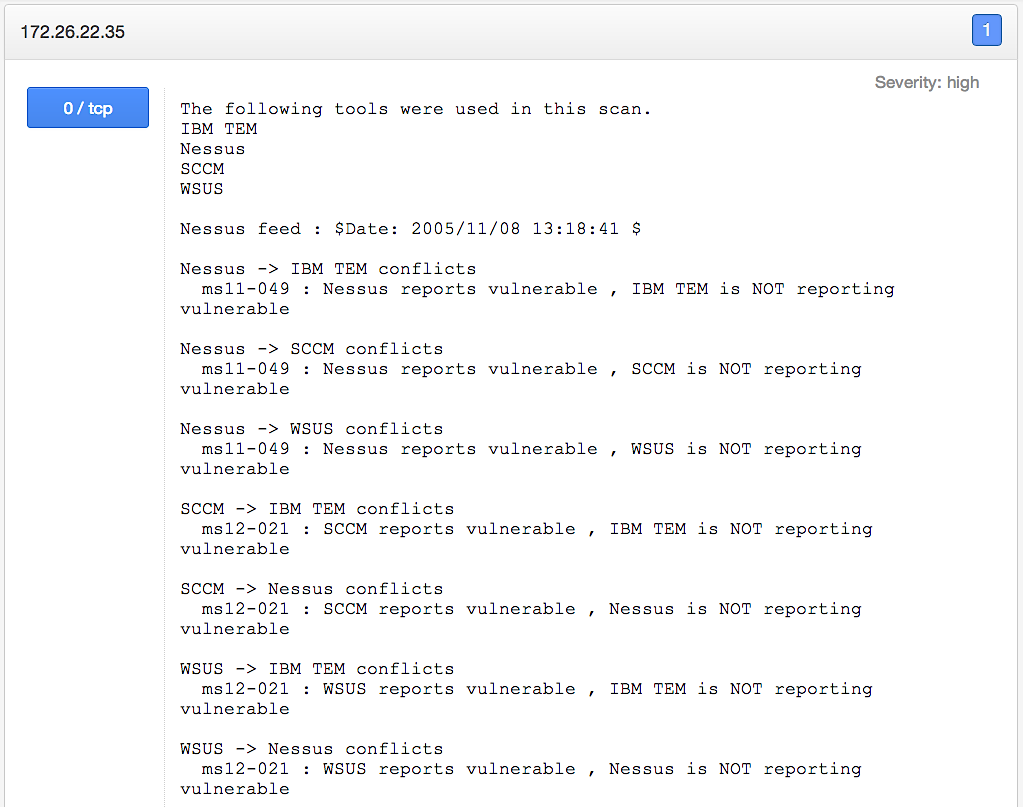
Two new Nessus plugins, titled Patch Management Windows Auditing Conflicts and Patch Management Auditing Satisfied, are now available to compare Windows patch auditing results. Nessus compares the patch data it finds on the target with results from patch management solutions. In addition, Nessus can also compare results from an organization's different patch management solutions. For example, if you provided credentials for the target hosts themselves and Microsoft SCCM, Microsoft WSUS, and IBM TEM, Nessus will produce the following report:
The above results come from the Patch Management Windows Auditing Conflicts plugin and detail the discrepancies between Nessus and patch management solutions results.
As we've established (see the previous post "If a Security Control Falls in the Forest…"), patches can fall off a system for a variety of reasons. This underscores the importance of cross-referencing patches between what is on the system and what the patch management solution thinks is on the system. In the above Nessus output, you can see that Nessus had credentials to login to the target system itself (indicated by the "Nessus ->"). Nessus was also able to pull the patch levels from SCCM (as indicated by the "-> SCCM conflicts"). What follows is a report for each patch and the discrepancies. As the first entry indicates for the host, Nessus found MS11-049 missing, but IBM TEM is reporting that patch as being applied.
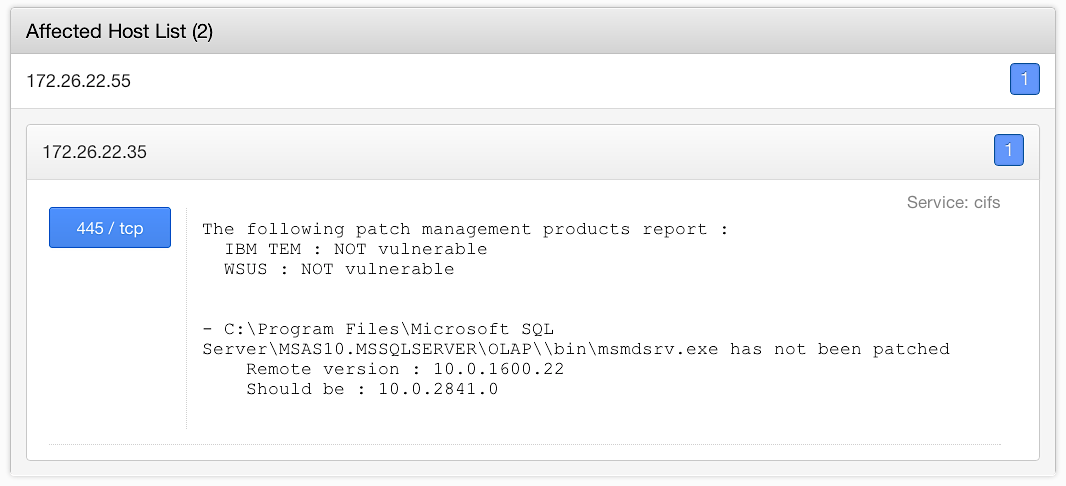
Administrators can view more details by reviewing the results for each missing patch. Nessus will display the file and/or registry key that was used to validate the installation of the patch. This can be used to quickly identify the gaps in your patching processes.
Often, security professionals run into the problem of conflicting patch audits. The systems administrators sometimes dispute the results of the vulnerability scan, causing potential exposures to linger in your environment. With this new functionality, you will have the information to work with your systems administrators to work out the gaps in your patch management processes, and more quickly and easily resolve problems.
Conclusion
One of the concepts that sticks out in my mind, mentioned by Gene Kim in our interview, was "trust but verify." This new plugin allows you to do just that. It’s critical to the success of your IT organization to implement a well thought-out patch management strategy. However, how do you know if it's functioning properly and there are no gaps? By using Nessus and SecurityCenter you can keep tabs on the overall health of your systems, processes, and procedures on a continual basis and make adjustments as you go. Nessus also has the ability to perform configuration auditing against IBM TEM servers and clients, including checks for software versions, service status, and file permissions. The PVS (Passive Vulnerability Scanner) can further monitor patch management systems and detect vulnerabilities in real time over the network. This level of continuous monitoring will allow you to constantly measure the integrity of the systems in your environment and take corrective actions when necessary.
- Nessus
- Patch Auditing
- SecurityCenter