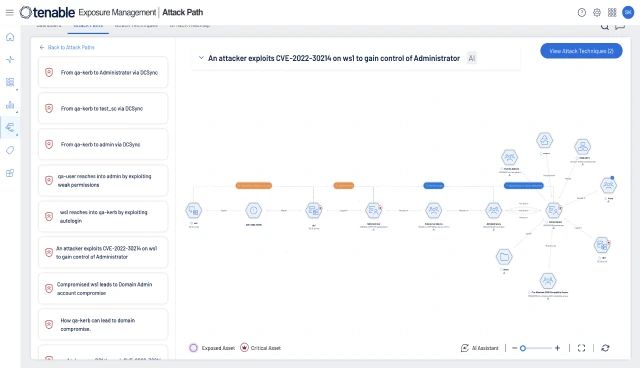
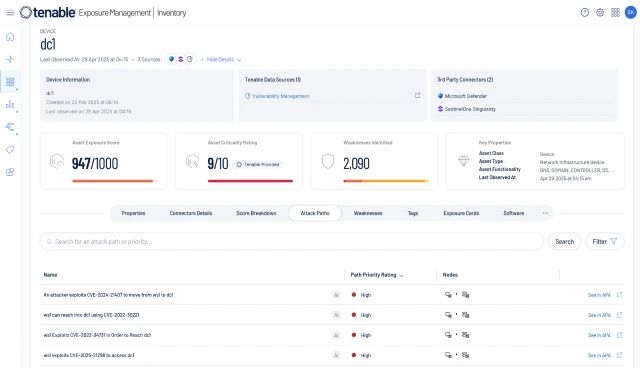
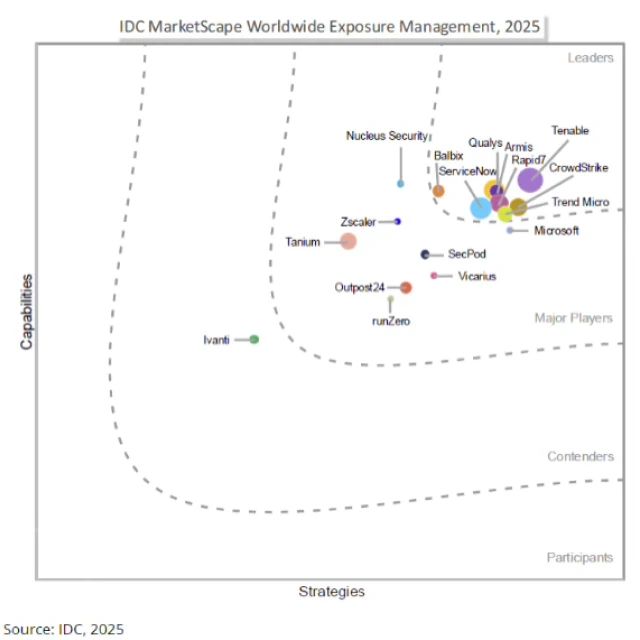
Go beyond Unified Vulnerability Management
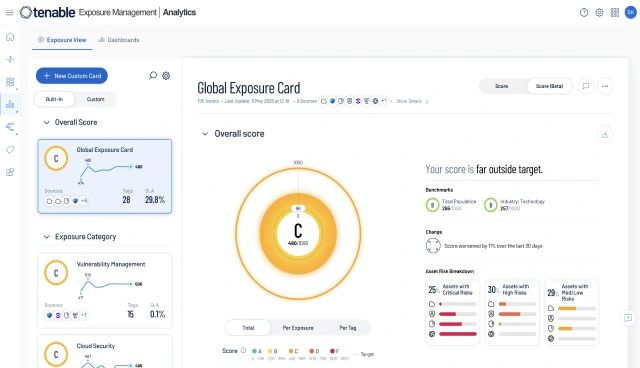
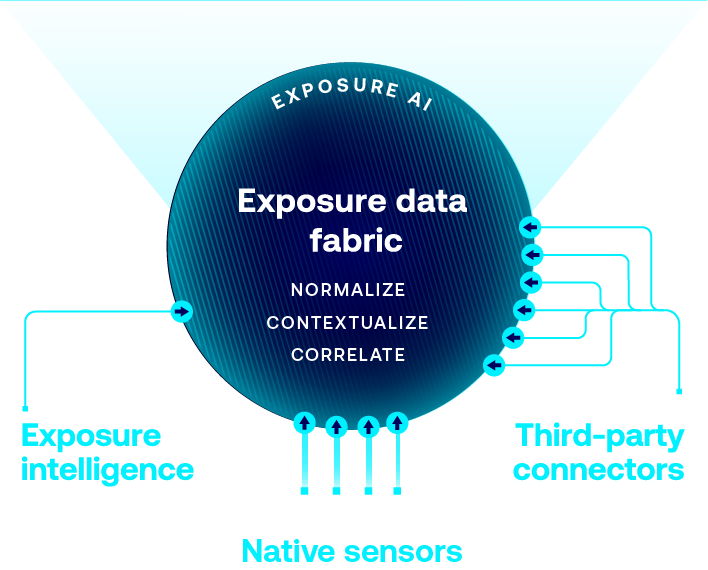
Take control of your cyber risk with Unified Vulnerability Management, bringing all your data together into a single, unified view. Then go further—gain the relationship context you need to understand which risks represent real business exposure—and prioritize what truly matters.