See Everything
Predict What Matters
Understand your risk and know which vulnerabilities to fix first with Tenable Vulnerability Management.
Buy Tenable Vulnerability Management Now Try Tenable Vulnerability Management FREE


Get a Risk-based View of Your Entire Attack Surface - from IT to Cloud to Containers.
Get a risk-based view of your entire attack surface - so you can quickly identify, investigate and prioritize vulnerabilities.
Managed in the cloud and powered by Nessus technology, Tenable.io provides the industry's most comprehensive vulnerability coverage with the ability to predict which security issues to remediate first. It’s your complete end-to-end vulnerability management solution.

Discover
Active scanning, agents, passive monitoring, cloud connectors and CMDB integrations provide unified visibility and a continuous view of all of your assets - both known and previously unknown.

Assess
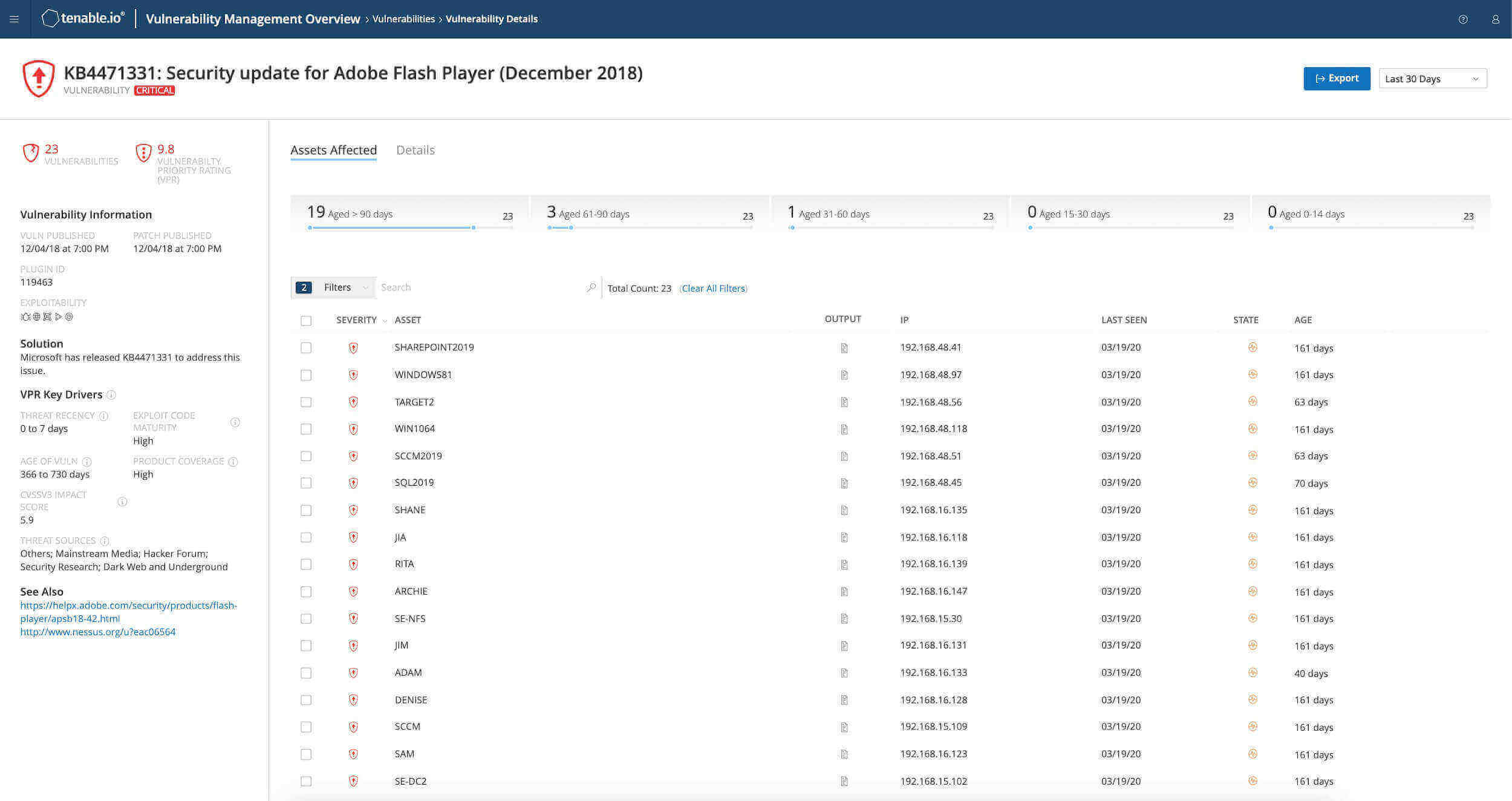
With coverage for more than 55,000 vulnerabilities, Tenable has the industry’s most extensive CVE and security configuration support to help you understand all of your exposures.

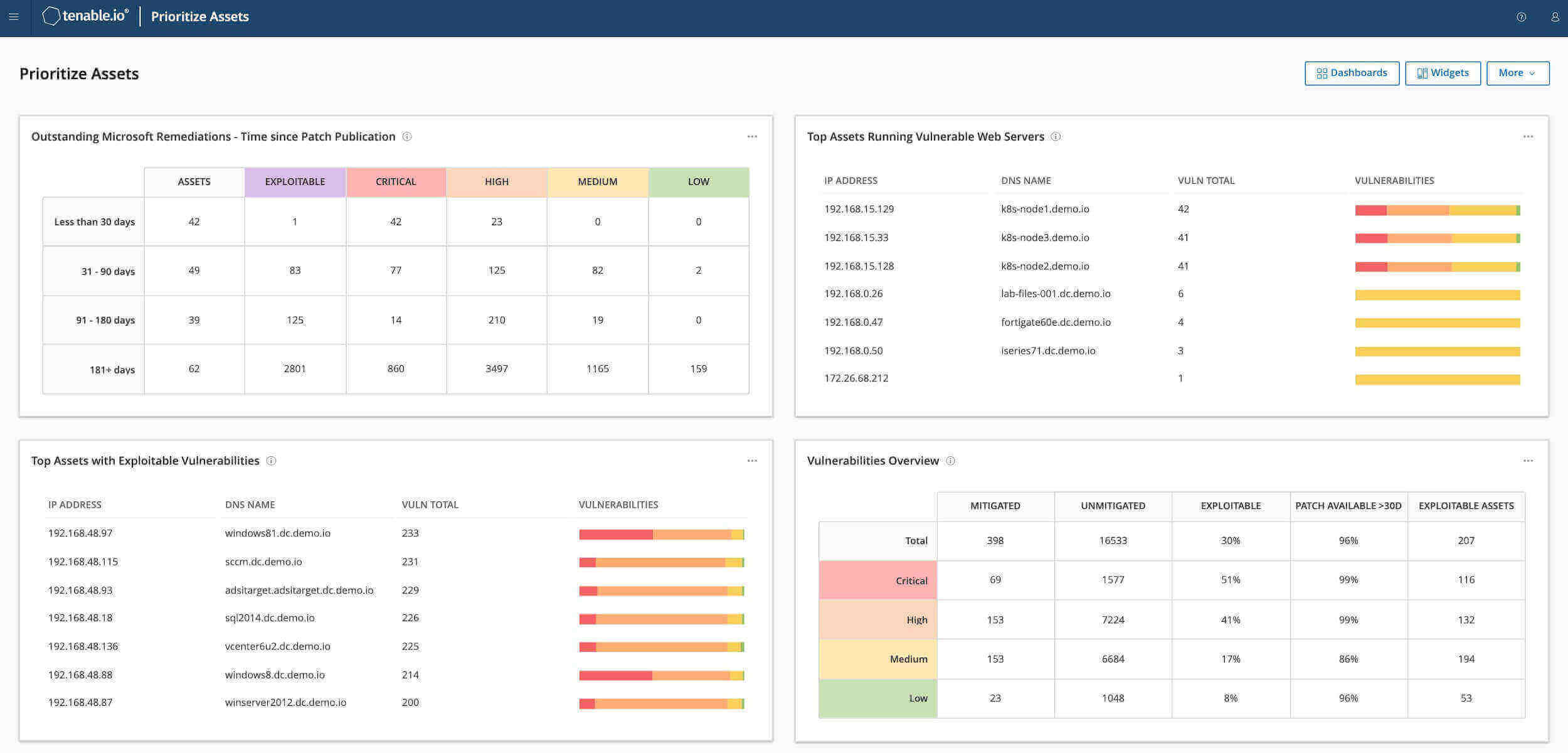
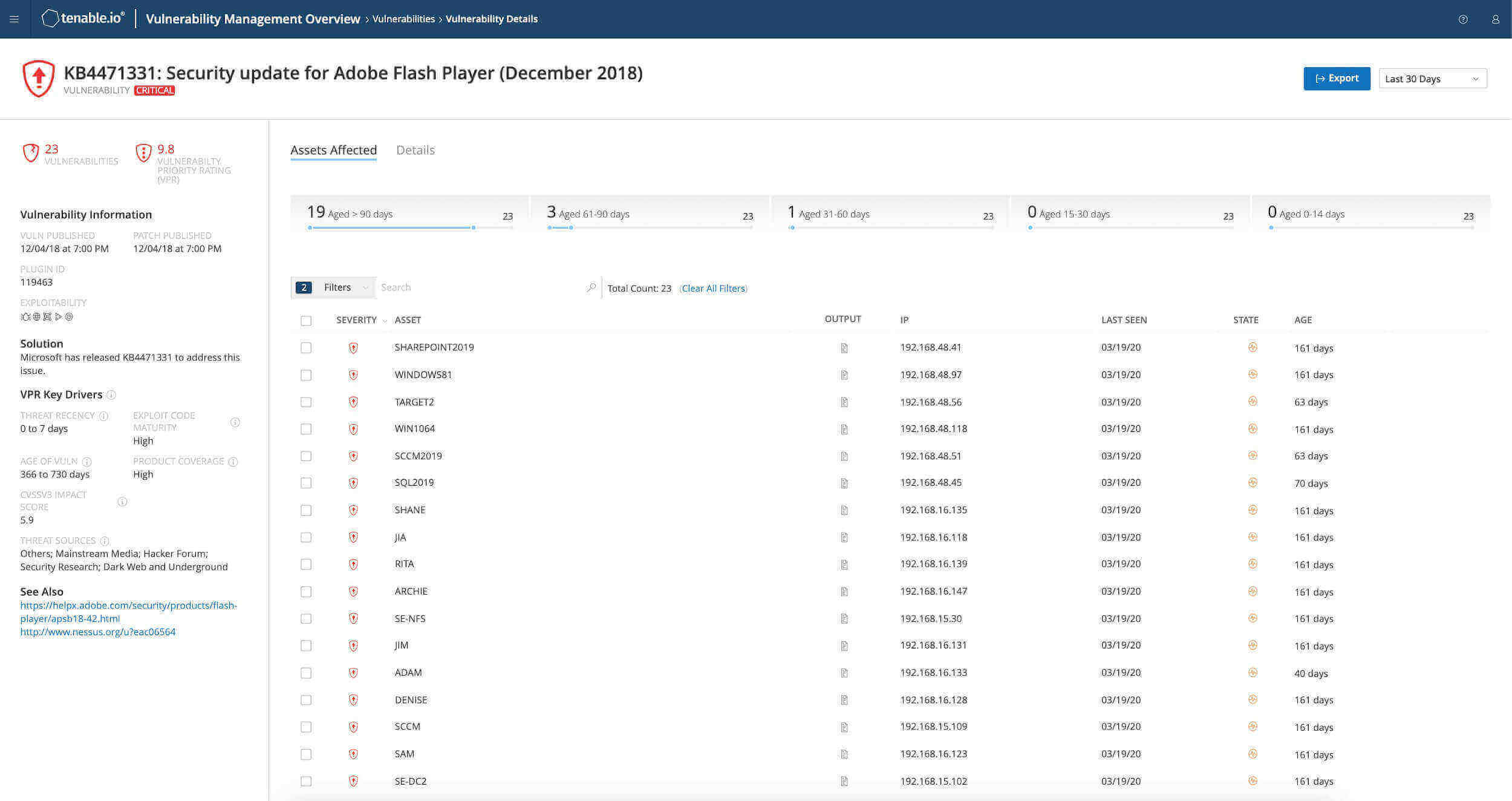
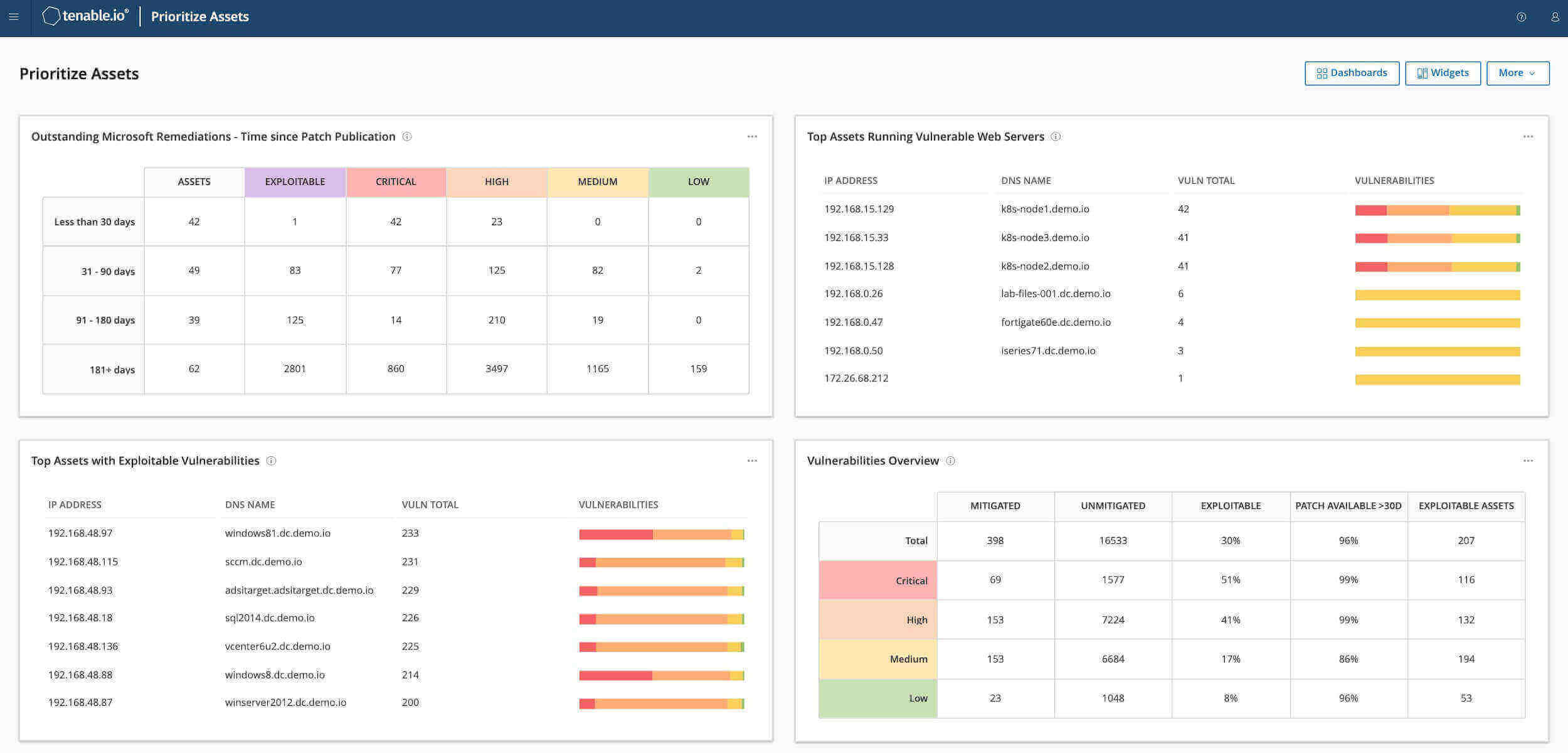
Prioritize
Combine vulnerability data, threat intelligence and data science for
easy-to-understand risk scores to quickly assess risk and know which vulnerabilities to fix first.
Actively Identify, Investigate and Prioritize Vulnerabilities
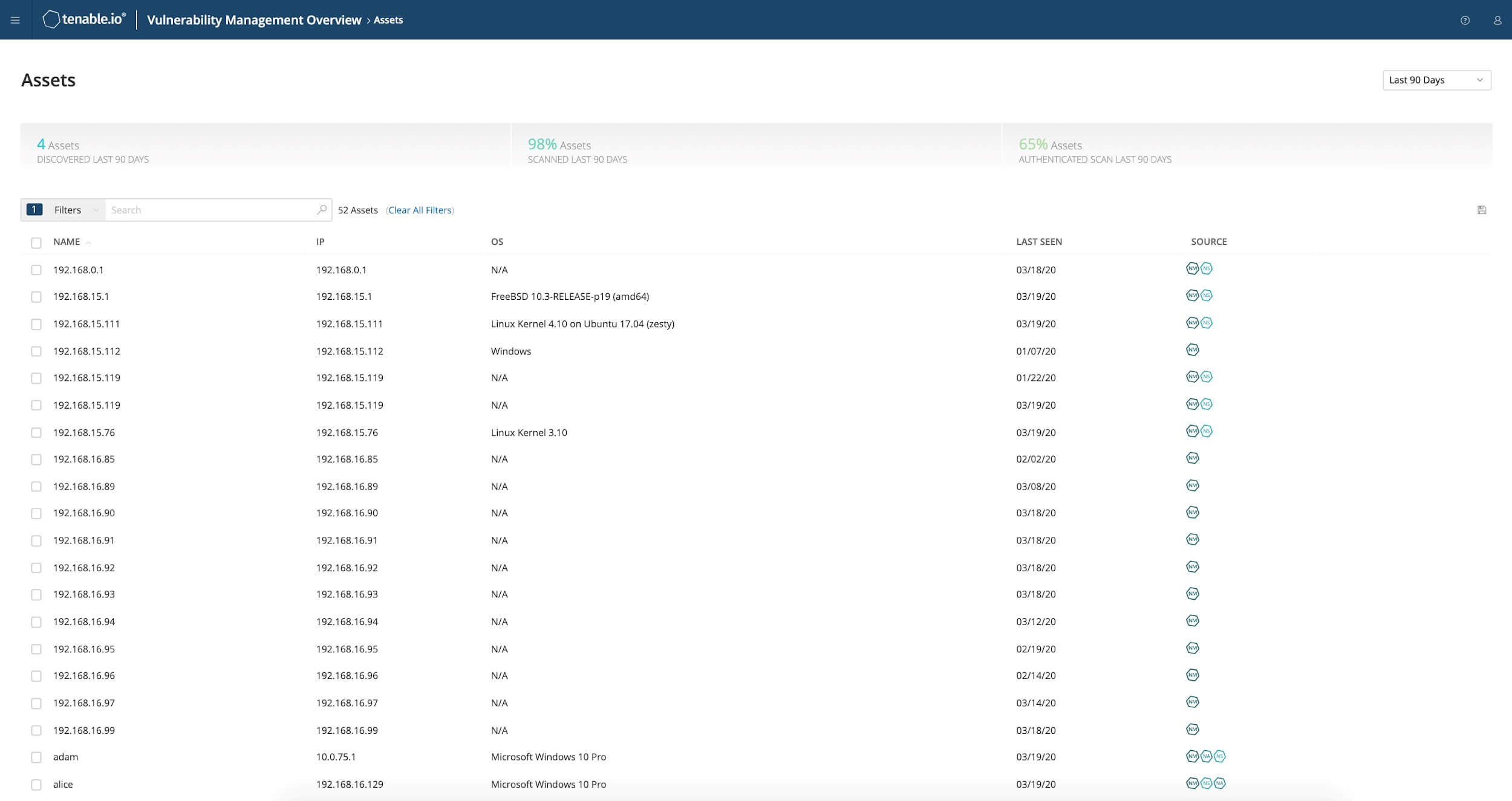
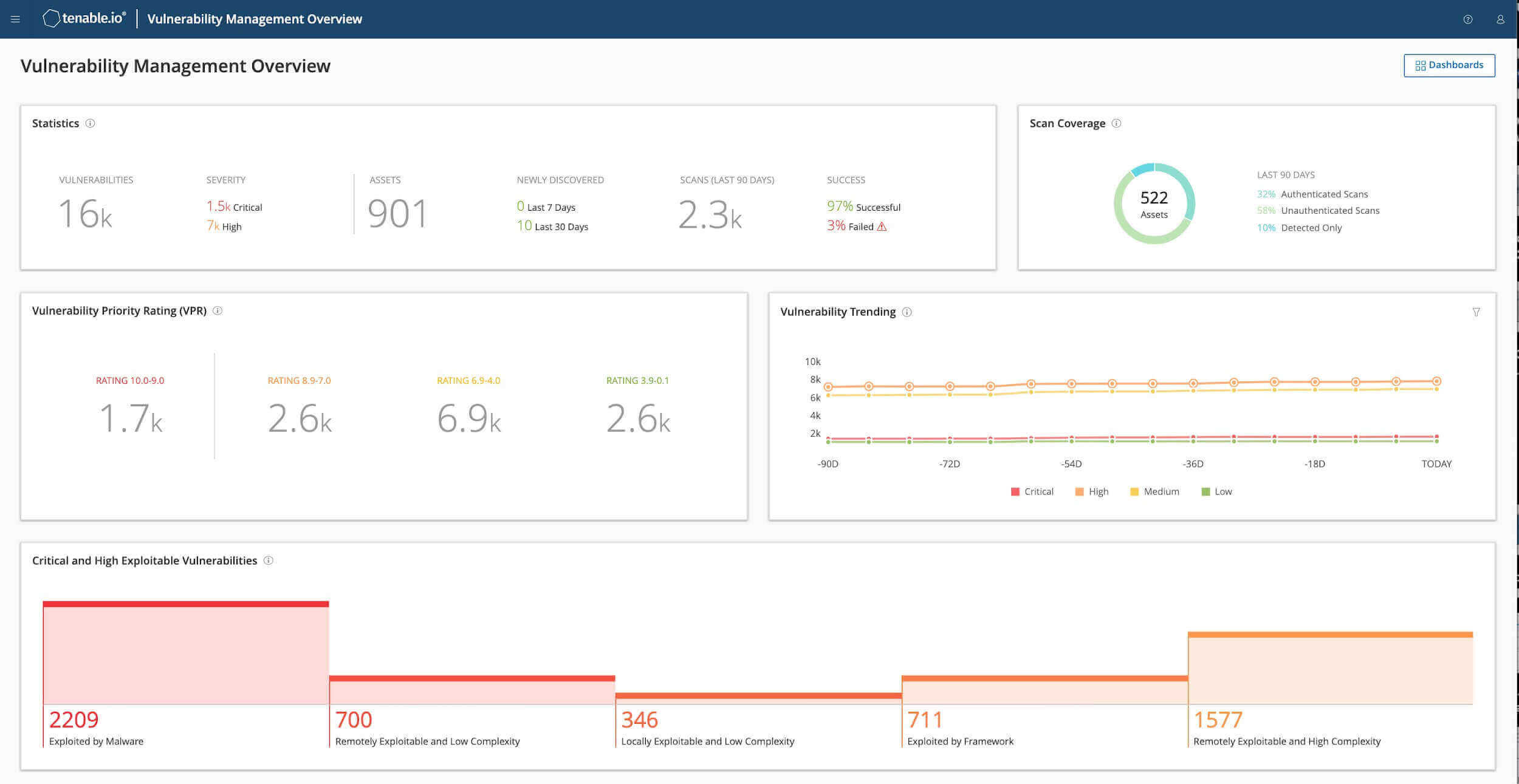
A diverse array of sensors automatically gathers and analyzes your security and vulnerability data. You get full visibility into your entire attack surface - for any asset on any computing platform.
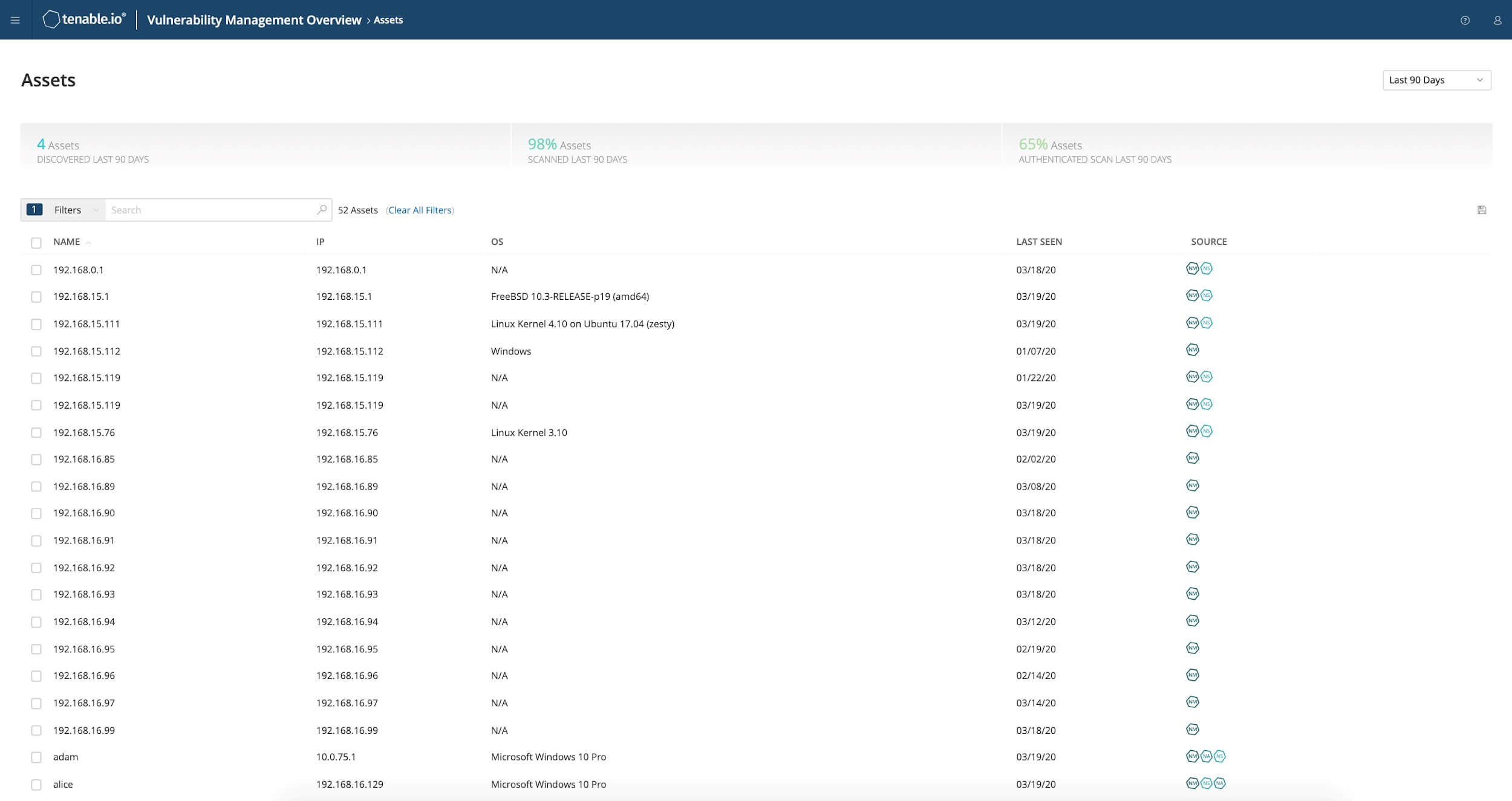
Continuously track and assess known and unknown assets and their vulnerabilities—even highly dynamic IT assets like mobile devices, virtual machines, containers and cloud instances.
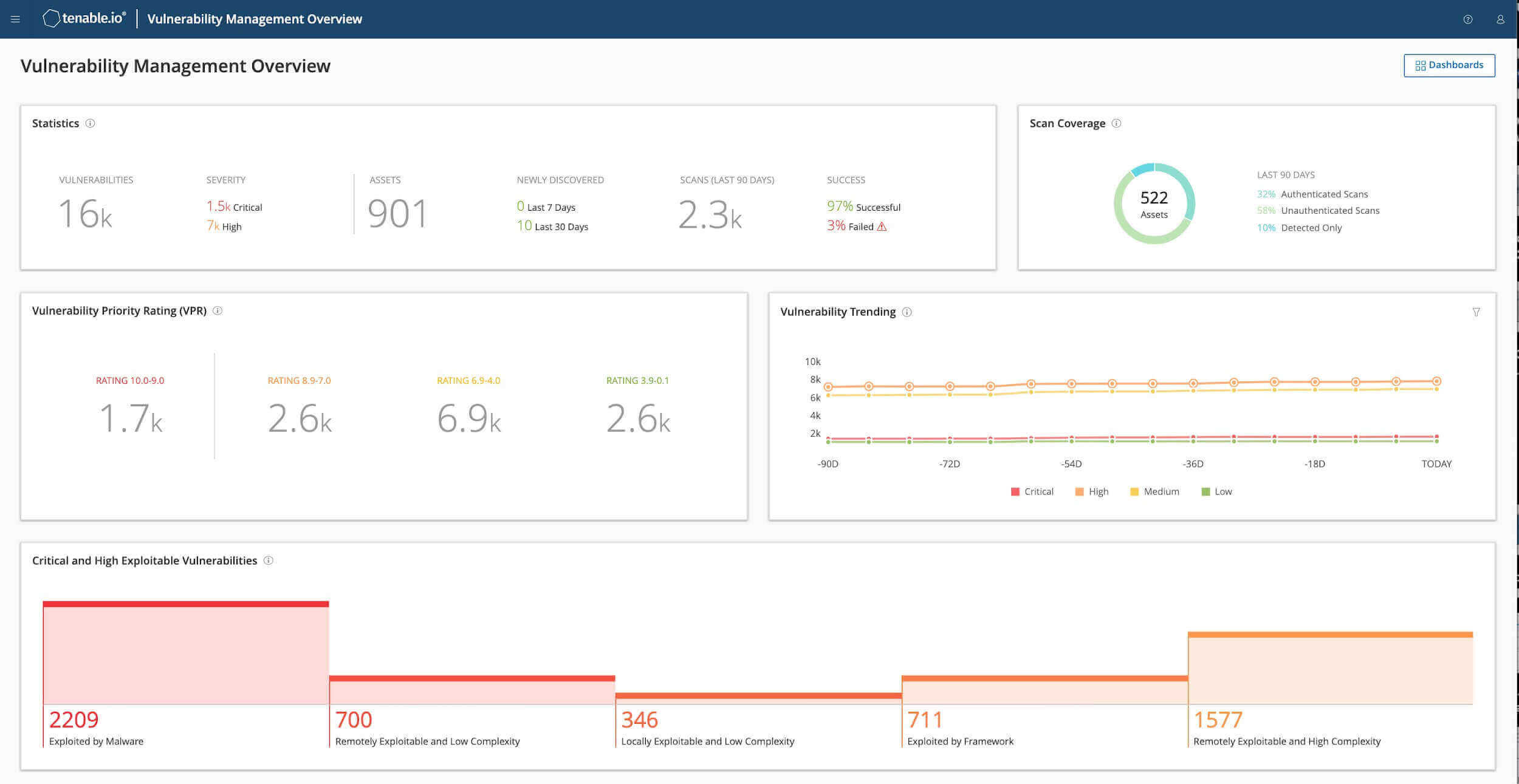
Proactively identify and prioritize vulnerabilities with the highest impact to your organization. Get targeted alerts when new threats appear to quickly respond.
Get immediate insight with intuitive dashboard visualizations for rapid analysis. Customize reports to inform security teams about critical issues.
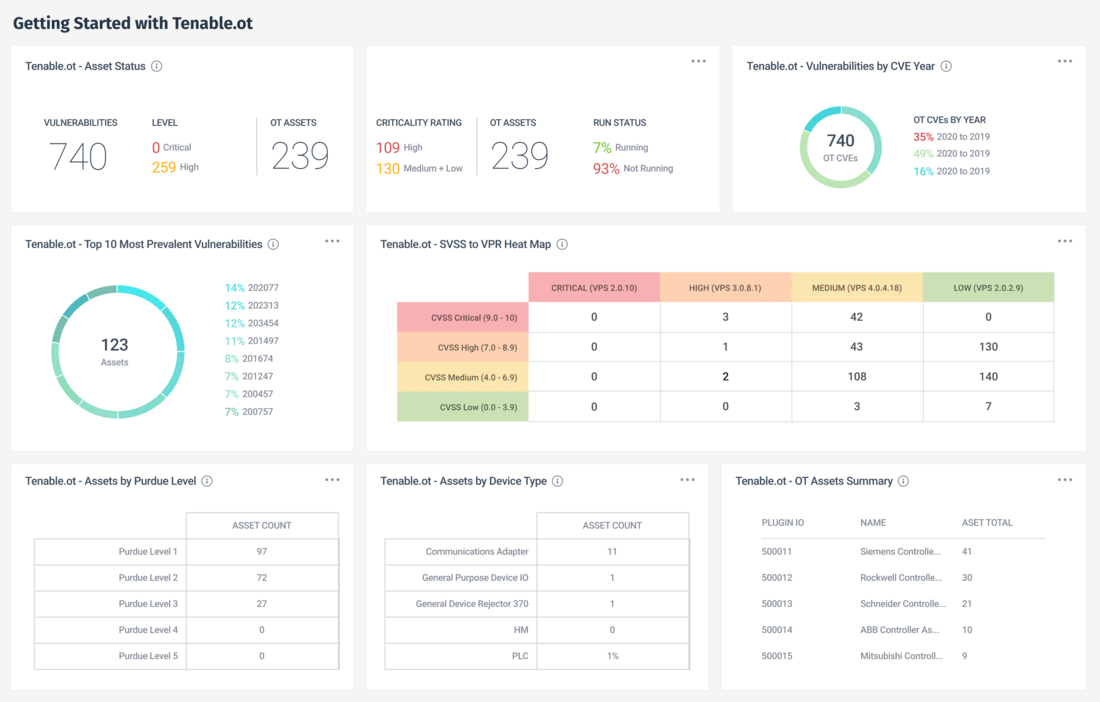
Reduce Risk Across OT Operations,
From Anywhere
If you are involved in industrial operations or critical infrastructure, you know risk does not stop with IT.
Tenable Vulnerability Management now integrates with Tenable OT Security so you can gain full visibility of your IO risk and manage your environment from the cloud.
Harness the Power of Data to Respond Faster
#1
in CVE
Coverage
59K
Vulnerabilities assessed with 147,000+ Plugins
#1
in Zero Day
Research
98
Vulnerabilities disclosed in 2020
#1
in Vulnerability
management
<24hrs
Median time for coverage of high profile issues
Ready to protect your modern attack surface?
Buy Tenable Vulnerability Management Now Try Tenable Vulnerability Management FREE To the Top
To the Top


