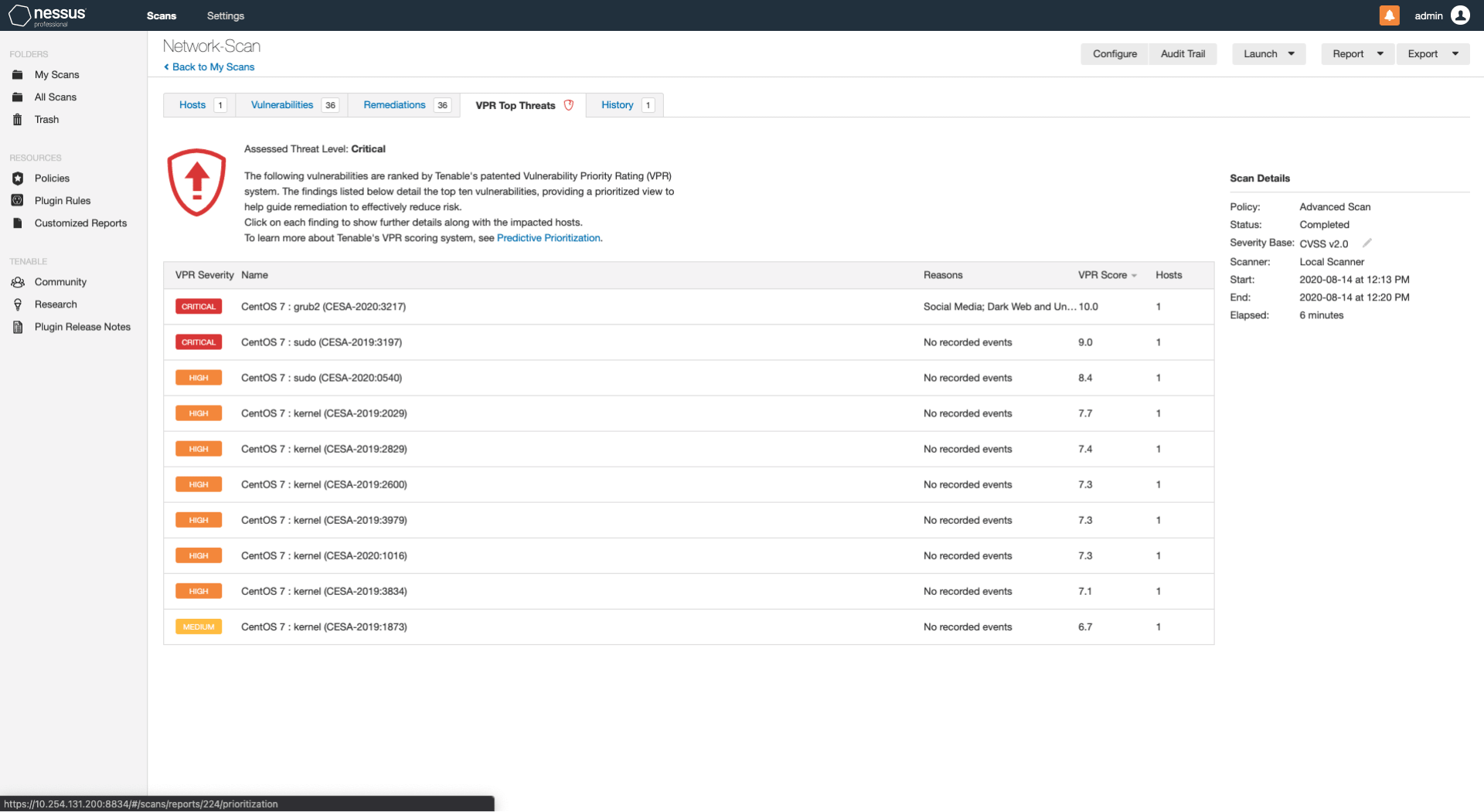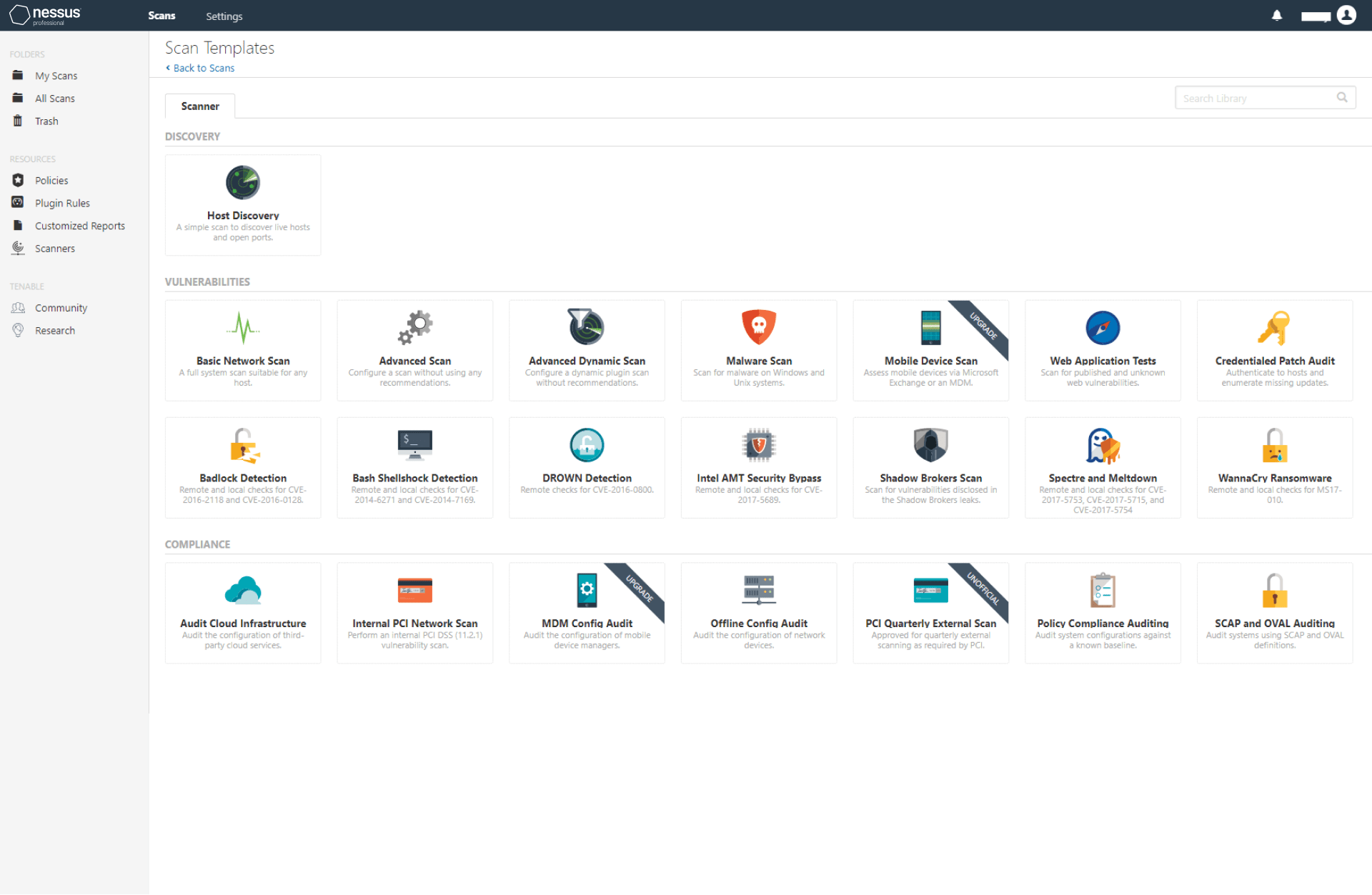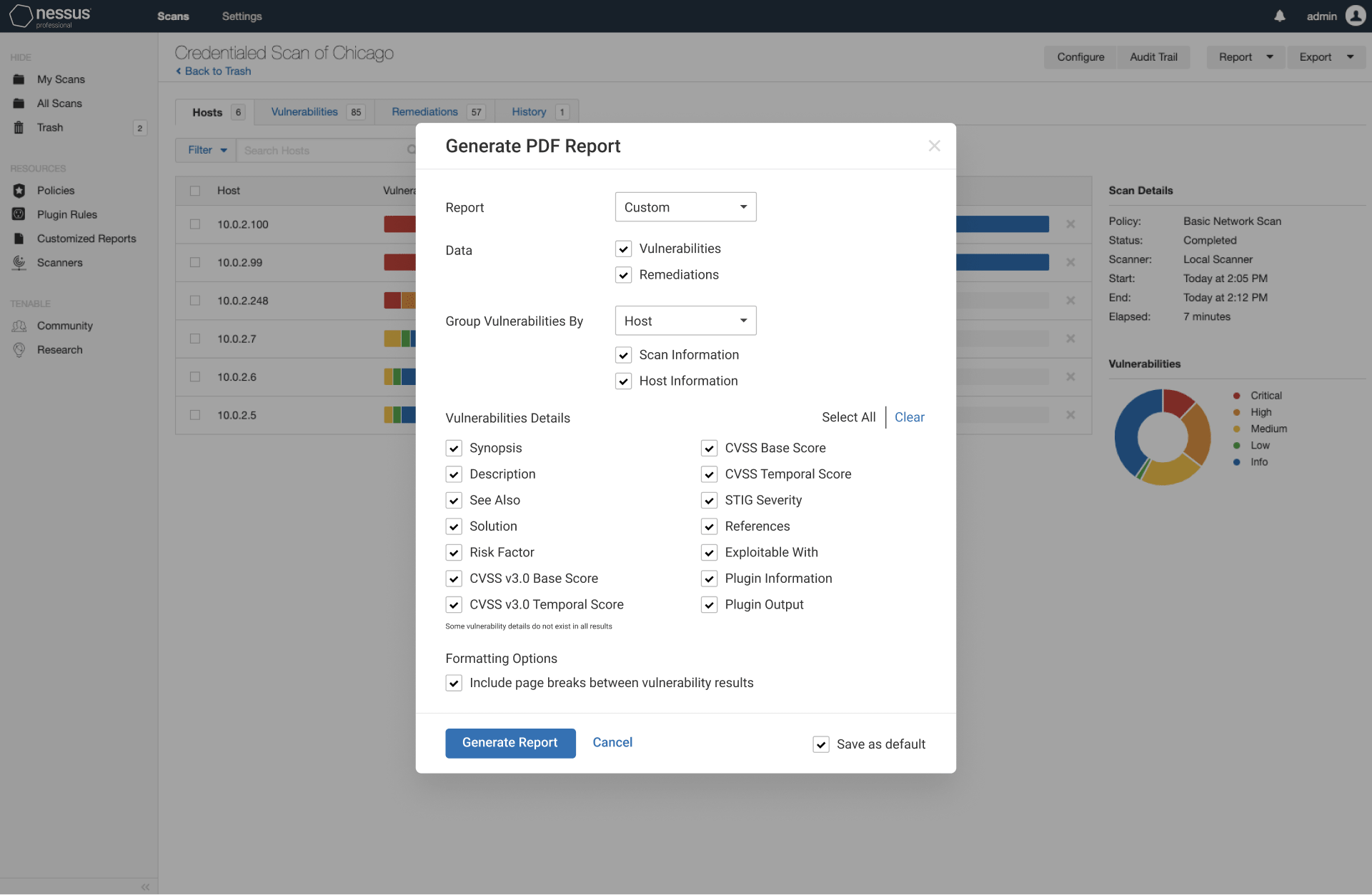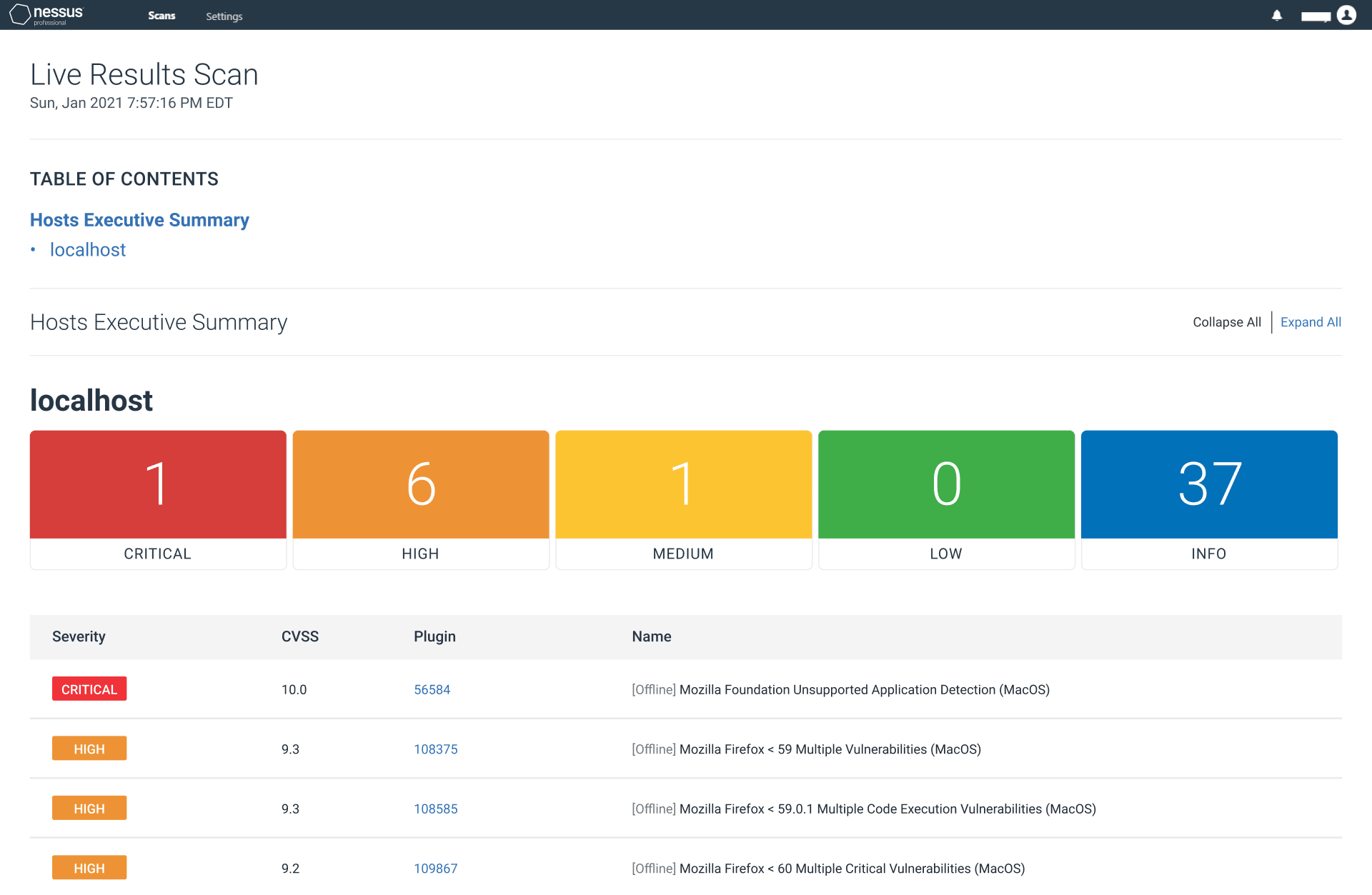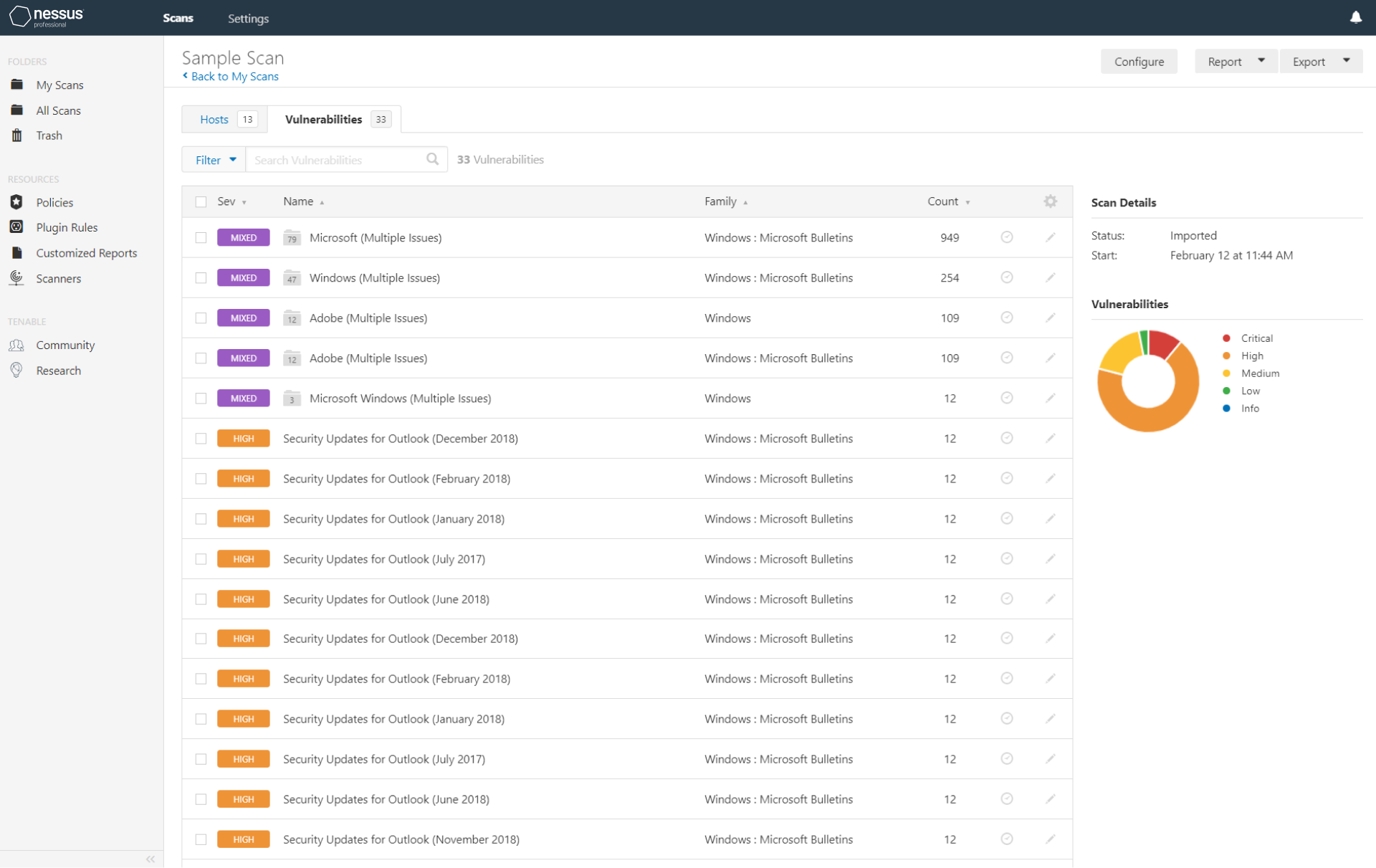
Nessus is the de-facto industry standard vulnerability assessment solution for security practitioners. The latest intelligence, rapid updates, an easy-to-use interface.
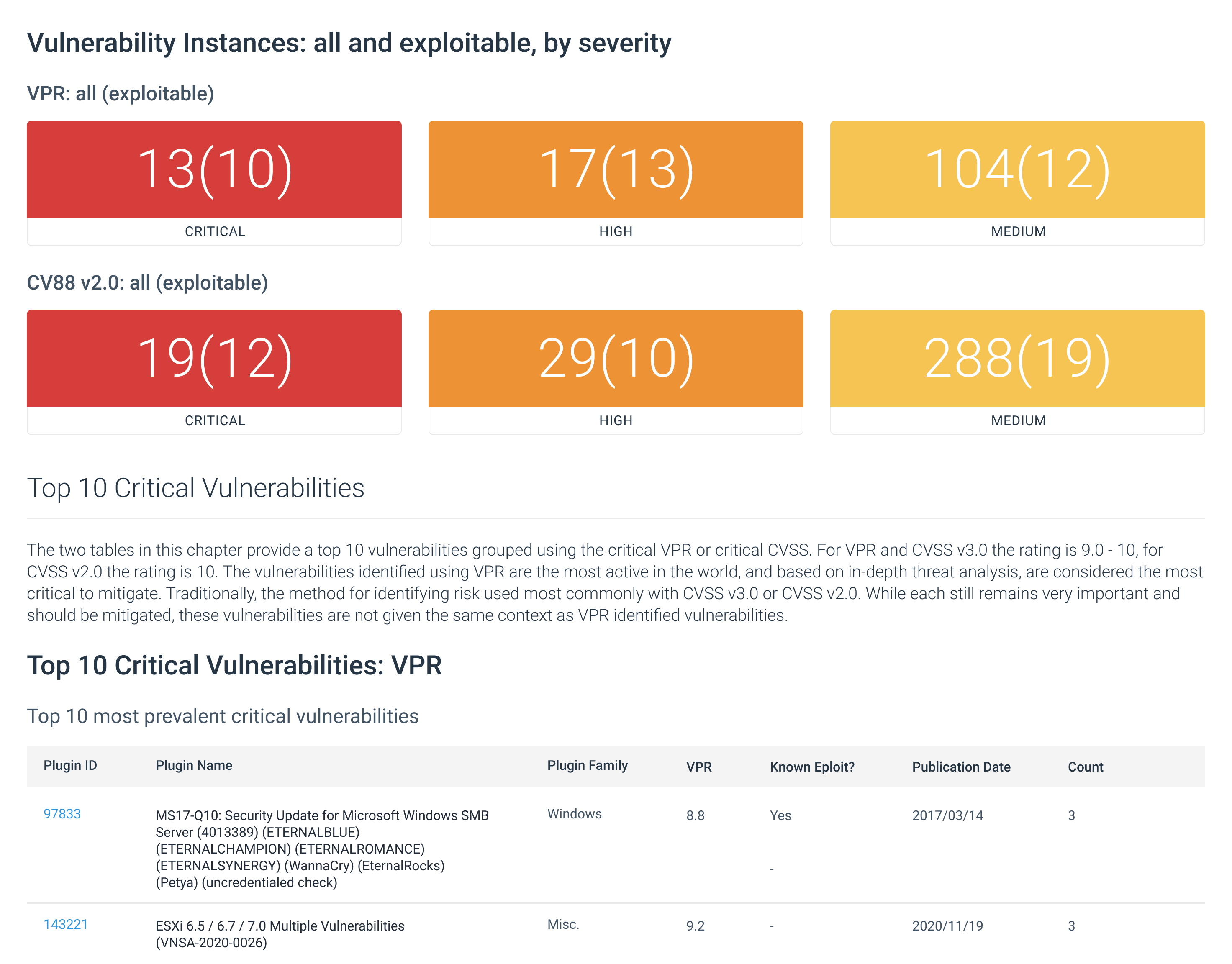
- Covers an industry-leading 85,000+ vulnerabilities
- Unlimited scans at no extra cost
- Compliant with PCI, HIPAA, GLBA, CIS, NIST, and more