by Megan Daudelin
September 2, 2015
The membership rates of social networking websites are at an all-time high. As of 2014, Facebook had 1.3 billion active accounts, followed in popularity by Twitter’s 646 million accounts. Out of concern for employee productivity, many company use policies now contain provisions about the use of social networking websites. While social networks can be a great resource for employees, overuse taxes the network and brings productivity into question. An organization can use Tenable’s SecurityCenter Continuous View (CV) to track social network use and determine what steps may be necessary.
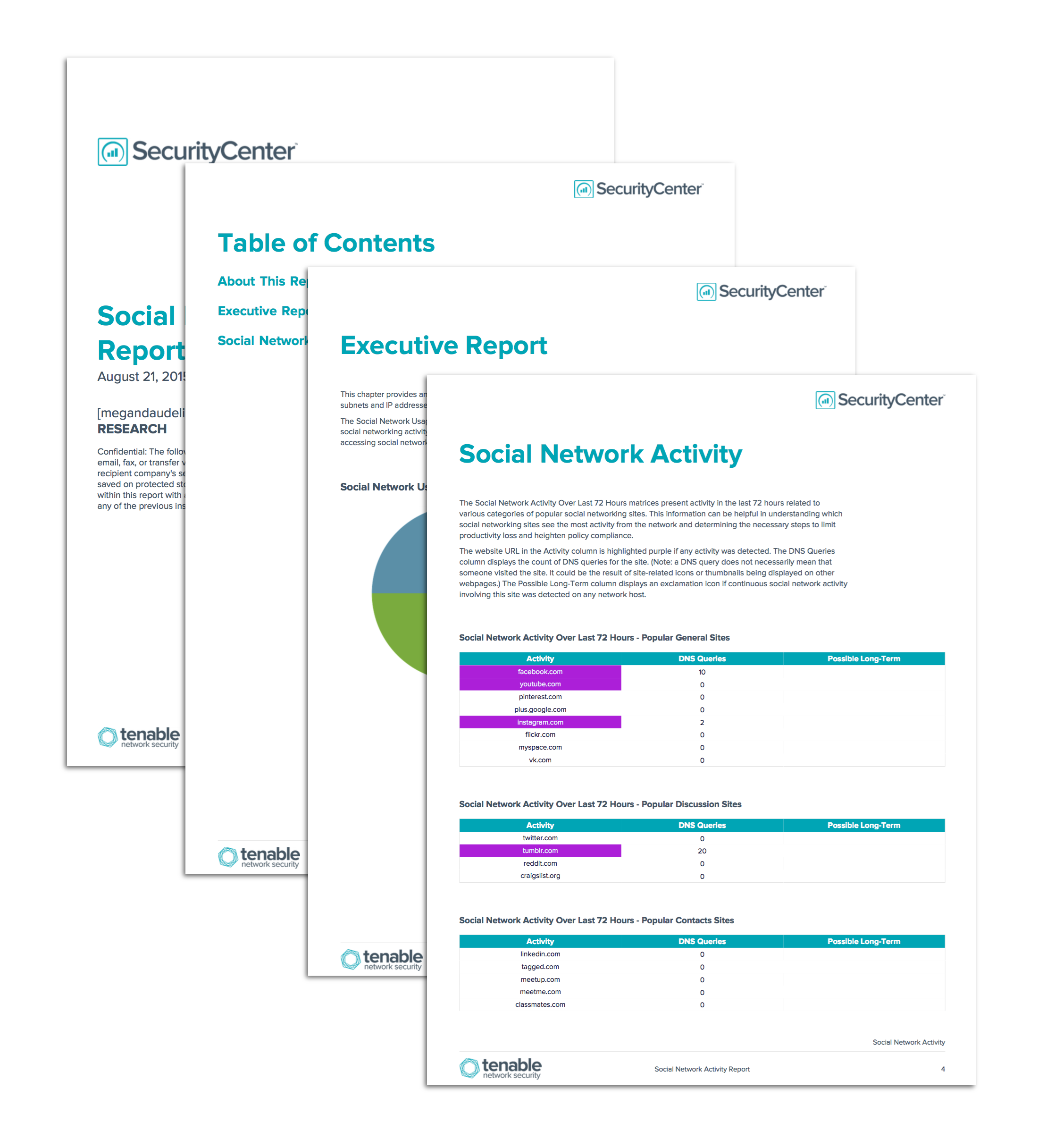
The Social Network Activity Report provides high-level information about the use of social networking in an organization. A series of charts and tables illustrate the activity associated with popular social networking websites. Two charts show which subnets and IP addresses generate the highest counts of social network activity. Three matrices show activity for different categories of social networking websites over the last 72 hours. A matrix details hosts that have continuously accessed social networking sites for long periods during the last 72 hours. A final two tables show trend information about specific events and overall social network access over the last 72 hours and 25 days, respectively.
The report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The report can be easily located in the SecurityCenter Feed under the category Executive.
The report requirements are:
- SecurityCenter 5.0.1
- PVS 4.0.1
- LCE 4.2.2
Note: This report relies on Passive Vulnerability Scanner (PVS) detections being forwarded to the Log Correlation Engine (LCE). Make sure that the PVS is configured to send syslog messages to the LCE: in Configuration > PVS Settings > Syslog, include the LCE host (with port 514) in the Realtime Syslog Server List. The LCE listens for syslog messages by default.
SecurityCenter Continuous View (CV) provides organizations with proactive continuous network monitoring to identify policy violations and misuse within the network. SecurityCenter CV enables the organization to react to policy non-compliance and breaches of acceptable use. SecurityCenter CV supports more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure.
Chapters:
- Executive Summary: This chapter provides an overview of the social network activity seen on the network. The charts show which subnets and IP addresses generate the highest counts of social network activity in the network.
- Social Network Activity: The Social Network Activity chapter contains several charts and tables displaying data about social network activity. Three matrices show activity for different categories of social networking websites over the last 72 hours. The next matrix details hosts that have continuously accessed social networking sites for long periods during the last 72 hours. The last two tables show trend information about specific events and overall social network access over the last 72 hours and 25 days, respectively.