by Megan Daudelin
August 16, 2016
Many organizations do not have adequate incident response plans to deal with compromised machines and network devices. Once a host has been compromised, malware can remain on the system for weeks or more, harvesting credentials, stealing data, and causing significant and widespread damage. Without adequate detection and reporting capabilities, organizations will not have a clear picture of the extent of an infection or compromise. Analysts could miss critical information on attack vectors that were used and the points of entry into the network. Inadequate data backups can also hamper recovery efforts as business critical information may be corrupted or lost completely. Organizations need to have a comprehensive business continuity or disaster recovery plan in place to recover and restore business operations in the event of a natural disaster or network incident. Without these plans, an incident or compromise may jeopardize an organization's competitiveness and long-term survival.
In order to perform effective incident response procedures, extensive information about the network and specific hosts impacted by the incident must be readily available. Attempting to gather detailed information from affected systems after an incident has occurred wastes precious time and resources that should be spent responding to and recovering from the effects of the incident. Integrating incident response preparation measures into regular scanning and monitoring procedures is the most effective way to prepare for and detect an incident. Many types of incidents require a swift response in order to minimize their impact, including intrusions and malware infections. If allowed to proliferate, malicious activities can spread through a network and impact critical systems and data. Tenable SecurityCenter Continuous View (CV) leverages multiple data sources in order to provide comprehensive incident response support. Active scanning by Tenable Nessus gathers detailed information about hosts and network devices, while passive listening by the Tenable Passive Vulnerability Scanner (PVS) sniffs network traffic to detect activity and connections that could be a cause for concern. The Tenable Log Correlation Engine (LCE) synthesizes data from other security devices to provide event correlation in support of early detection and incident response efforts.
The Incident Response Support report provides access to extensive details about hosts on the network in order to effectively prepare security teams in case of an incident. System information about listening port connections is presented to help support incident response planning and identify post-exploitation activity. Security teams can use the data presented to monitor the network for wireless and portable devices that have been connected to the network. Service detection on internal hosts will provide valuable information on any unauthorized or insecure services in use that could be exploited by attackers. Indicators and tables provide a comprehensive look at system information, configurations, shared drives, startup programs, and active processes on internal hosts. This information can be useful in determining an initial point of entry used by an attacker, malicious processes that may be running, data that an attacker could have access to, and other systems that may have been compromised. The chapters in this report provide security teams with exhaustive details about hosts on the network in order to most effectively respond to incidents.
Event types commonly related to compromise are also presented, providing insight into potential malware infections. Additional indicators and tables are displayed that will alert analysts to potentially compromised hosts based on detected malware, malicious processes, or suspicious behavior. A ticket activity summary is included that leverages SecurityCenter CV’s integrated ticketing system, which can be used to track incident response activities. Indicators and tables about AutoRun and startup services will alert security teams to processes, registry keys, startup programs, and scheduled tasks that could potentially execute malicious programs on hosts. Information about unusual, suspicious, or never-before-seen login activity highlights potential sources of unauthorized access attempts. This information can be useful for security teams to understand current weaknesses and how to fix them, detect compromised hosts, and track incident response activity. Organizations will be able to use the extensive information presented by elements in this report to strengthen security controls, reduce the attack surface, and improve overall incident response procedures.
Without any additional filters, this report provides an overview of the incident response support information available for the entire network. When an incident occurs, the report can be easily modified to focus on specific hosts, assets, or repositories. When the report is added from the SecurityCenter Feed, analysts can set the Targets filter in the Focus section so that specific targets will be added automatically as filters to all of the included components. Setting this filter will allow security teams to more efficiently gather information about specific targets when responding to incidents on the network.
This report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the SecurityCenter Feed under the category Monitoring. The report requirements are:
- SecurityCenter 5.3.2
- Nessus 6.7.0
- LCE 4.8.0
- PVS 5.1.0
Tenable SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist in securing an organization’s internal network and effectively responding to incidents. SecurityCenter CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Host data and data from other security products is analyzed to monitor the network for malware, intrusions, and other forms of malicious activity. SecurityCenter CV provides an organization with the most comprehensive view of the network and the intelligence needed to support proactive incident response efforts.
The following chapters are included in this report:
- Executive Summary: This chapter contains a high-level overview of information relevant to conducting effective incident response measures. The information provided can be used to quickly understand factors related to an incident that may not be direct contributors to the incident.
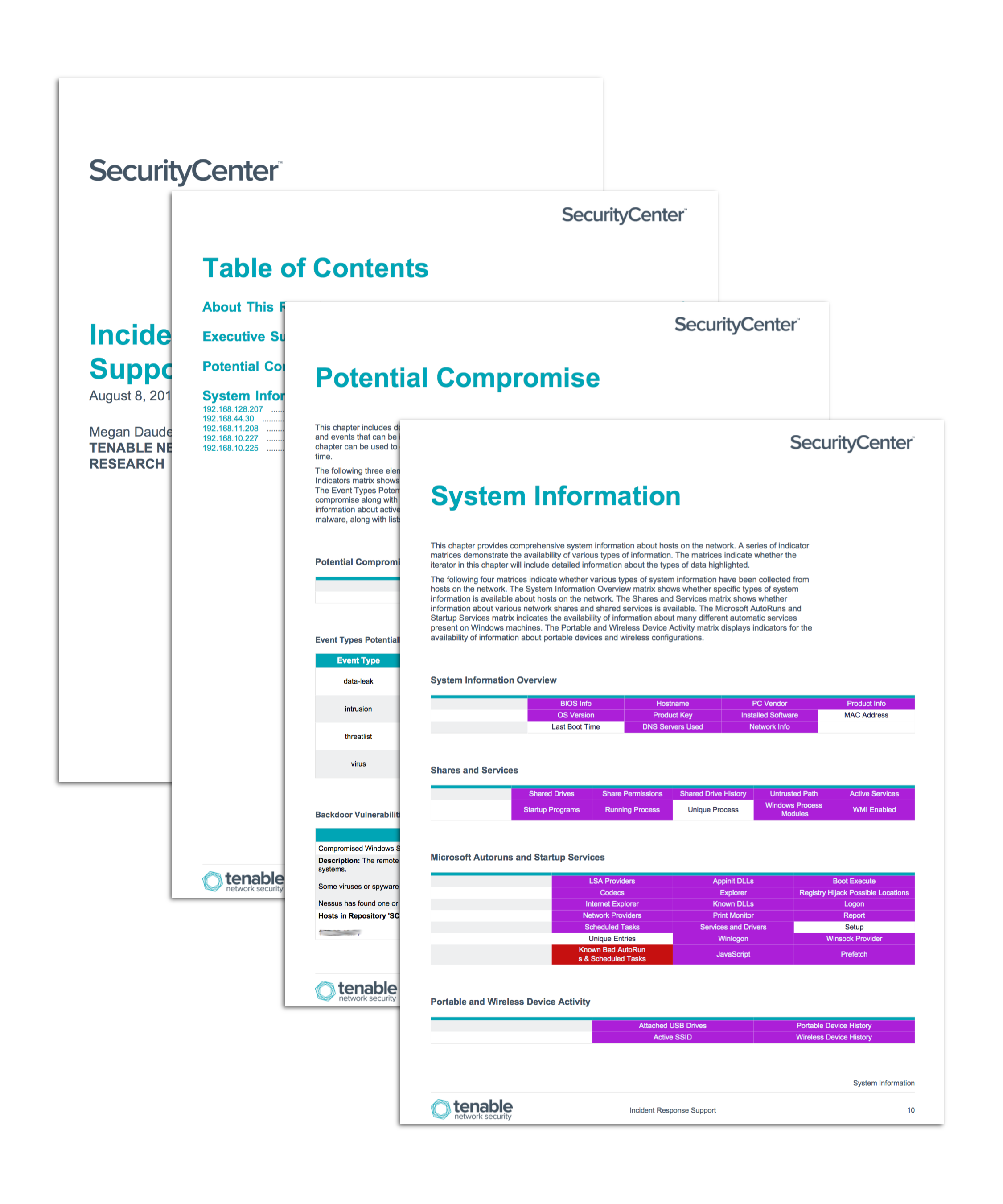
- Potential Compromise: This chapter includes detailed information about potential sources of system compromise. Vulnerabilities and events that can be indicative of compromise are analyzed and relevant information is presented. This chapter can be used to quickly identify sources of potential compromise in order to reduce incident response time.
- System Information: This chapter provides comprehensive system information about hosts on the network. A series of indicator matrices demonstrate the availability of various types of information. The matrices indicate whether the iterator in this chapter will include detailed information about the types of data highlighted.