by Cesar Navas
June 20, 2016
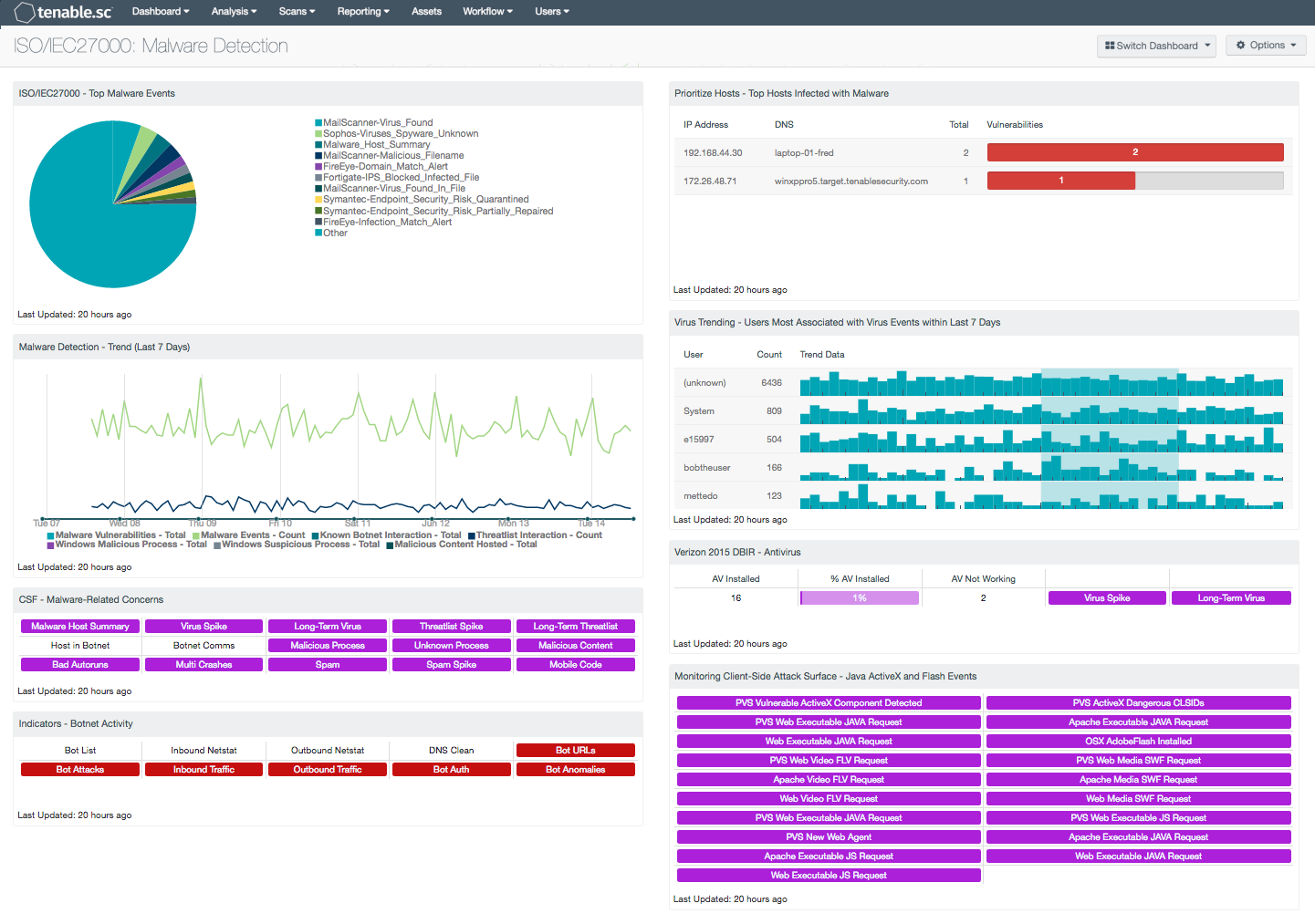
With the explosive rise in malware, many organizations fall short of having adequate protection. As the threat landscape continues to evolve, some malware can bypass traditional security prevention tools, which can leave an organization vulnerable to attack. The ISO/IEC27000 Malware Detection dashboard can assist the organization in monitoring network endpoints for potential malware, botnet interactions, malicious processes, and suspicious mobile code.
The ISO/IEC 27002:2013 framework is a global security standard that provides best practice solutions in support of the controls found in Annex A of ISO/IEC 27001:2013. The framework establishes guidelines and general principles for initiating, implementing, maintaining, and improving Information Security Management Systems (ISMS). Each security control and objective provided within the standard can be tailored to specific business and regulatory objectives, and assist with maintaining overall compliance. This dashboard focuses on the ISO/IEC 27002 12.2.1 control, which can help an organization to effectively detect and respond to malware incidents in a timely manner.
As the threat landscape continues to evolve, organizations must be vigilant in continuously monitoring for targeted attacks and advanced persistent threats. Networks have become increasingly vulnerable as the addition of cloud and mobile solutions have added additional threat vectors that organizations must account for. Policies such as Bring Your Own Device (BYOD) have incorporated additional mobile devices that may have malicious software or malware installed, which can introduce significant risks to a network. Implementing a multi-layered security strategy will help to create a proactive security posture, which can aid in reducing potential damage or impact from malware.
This dashboard provides a comprehensive solution to monitor network devices and alert the analyst to potential malware, network attacks, and other suspicious events. Hosts and users with malware related activity present valuable information that can discover potential misuse or malicious activity. Indicator components will alert on malicious traffic, botnet activity, long-term threats, and mobile code related events from devices that are forwarding event data to the Log Correlation Engine (LCE). Tenable’s Nessus Network Monitor (NNM) and Nessus provide real-time information on network endpoints to detect malware, suspicious traffic, and malicious software. Analysts can use this information to reduce the risk of malware infections. Together, this will provide analysts the ability to detect, respond, and recover more effectively, thus allowing organizations to stay on top of an progressively challenging threat landscape.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.3.2
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.1
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring platform. Tenable’s Log Correlation Engine (LCE) performs automatic discovery of users, infrastructure, and vulnerabilities across more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. NNM provides deep packet inspection to continuously discover and track users, applications, cloud infrastructure, trust relationships, and vulnerabilities. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Tenable.sc CV, Nessus, Log Correlation Engine (LCE) and Nessus Network Monitor (NNM) scales to meet future demand of monitoring virtualized systems, cloud services, and the proliferation of devices.
This dashboard contains the following components:
- ISO/IEC27000 - Top Malware Events: This component displays a pie chart of the IP addresses with the most events of type 'virus' that have occurred in the last 7 days. These events were reported by various applications and collected by the LCE. This information will provide targeted information that security teams and analysts can use to investigate suspicious events, detect malware, virus infections, and other malicious activity.
- Malware Detection - Trend (Last 72 Hours): This component displays trends for various malware-related information over the last 7 days. Note that because the chart scales to accommodate the trend line with the greatest height, trend lines that are less high may be difficult to see.
- CSF - Malware-Related Concerns: This matrix displays warning indicators for potential malware-related events and vulnerabilities detected on the network, such as virus and threatlist event spikes, botnet interactions, malicious processes and web content, bad Windows autoruns, multiple system crashes, and detections of spam and mobile code. Clicking on a highlighted indicator will bring up the analysis screen to display more details and allow further investigation. In the analysis screen, setting the tool to IP Summary will display the systems on which the detections and events occurred. For vulnerability detections, setting the tool to Vulnerability Details will display the full details for each vulnerability, including a description, the solution to fix the vulnerability, and in some cases, links to more information. For events, setting the tool to Raw Syslog will display the raw syslog of the events, which can give more details. The LCE maintains 24-hour summaries of malware or virus events detected on hosts; these summaries can be viewed by clicking on the Malware Host Summary indicator.
- Indicators - Botnet Activity: This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs and continuous scanning activity and places them into one spot.
- Prioritize Hosts - Top Hosts Infected with Malware: This table displays the top hosts on the network that have actively or passively detected malware infections. The list is sorted so that the host with the worst malware problem is at the top. A count of malware detections and a bar graph indicating the severity of the malware are given for each host. Use this table to determine the hosts with the biggest malware problems on the network.
- Virus Trending - Users Most Associated with Virus Events within Last 7 Days: Displayed is trend data for those users most associated with virus activity within the last 7 days, along with their associated event counts. The top 15 users with the highest event counts are displayed. This component provides insight into which users may be engaging in activity that exposes the network to viruses.
- Verizon DBIR - Antivirus: The Verizon DBIR advocates deploying an antivirus solution. This matrix assists the organization in monitoring its antivirus deployment. The AV Installed column displays the number of scanned hosts that have AV installed and working properly; the % AV Installed column displays a bar graph of the ratio of systems with AV installed to total systems scanned. The AV Not Working column displays the number of scanned hosts that have AV installed, but it is not working properly or not up to date. The Virus Spike indicator is highlighted purple if a large spike in virus activity was detected in the last 72 hours. The Long-Term Virus indicator is highlighted purple if in the last 72 hours an IP address has been the source of virus or malware events continuously for more than 20 minutes. Clicking on a highlighted indicator will bring up the analysis screen to display details on the detections and events and allow further investigation.
- Monitoring Client-Side Attack Surface - Java ActiveX and Flash Events: This matrix monitors for 19 normalized events that report on ActiveX, Java, and Flash events. The events included detect Flash Player requests, executable Java requests, and dangerous ActiveX controls. This information provides an analyst with easy access to suspected malicious events detected in syslogs.