by Sharon Everson
January 7, 2016
Indicators of compromise (IOC) are artifacts of unusual or unexplained network activity, behavior, pattern, or configuration changes that could indicate a potential breach has occurred. A good approach in identifying attacks and data breaches is to monitor the network for unusual activity. Monitoring the environment for this type of behavior can be a time consuming effort.
As network complexity is continuously evolving, attackers are utilizing new methods to infiltrate organizations. Security teams may find difficulty to keep pace with growing networks, and constantly changing attack surfaces. Numerous controls within the Center for Internet Security (CIS) Critical Security Controls, and Tenable’s Critical Cyber Controls call for network monitoring. Nessus, the Nessus Network Monitor, and the Log Correlation Engine offer a wide variety of detections for IOC and suspicious activity.
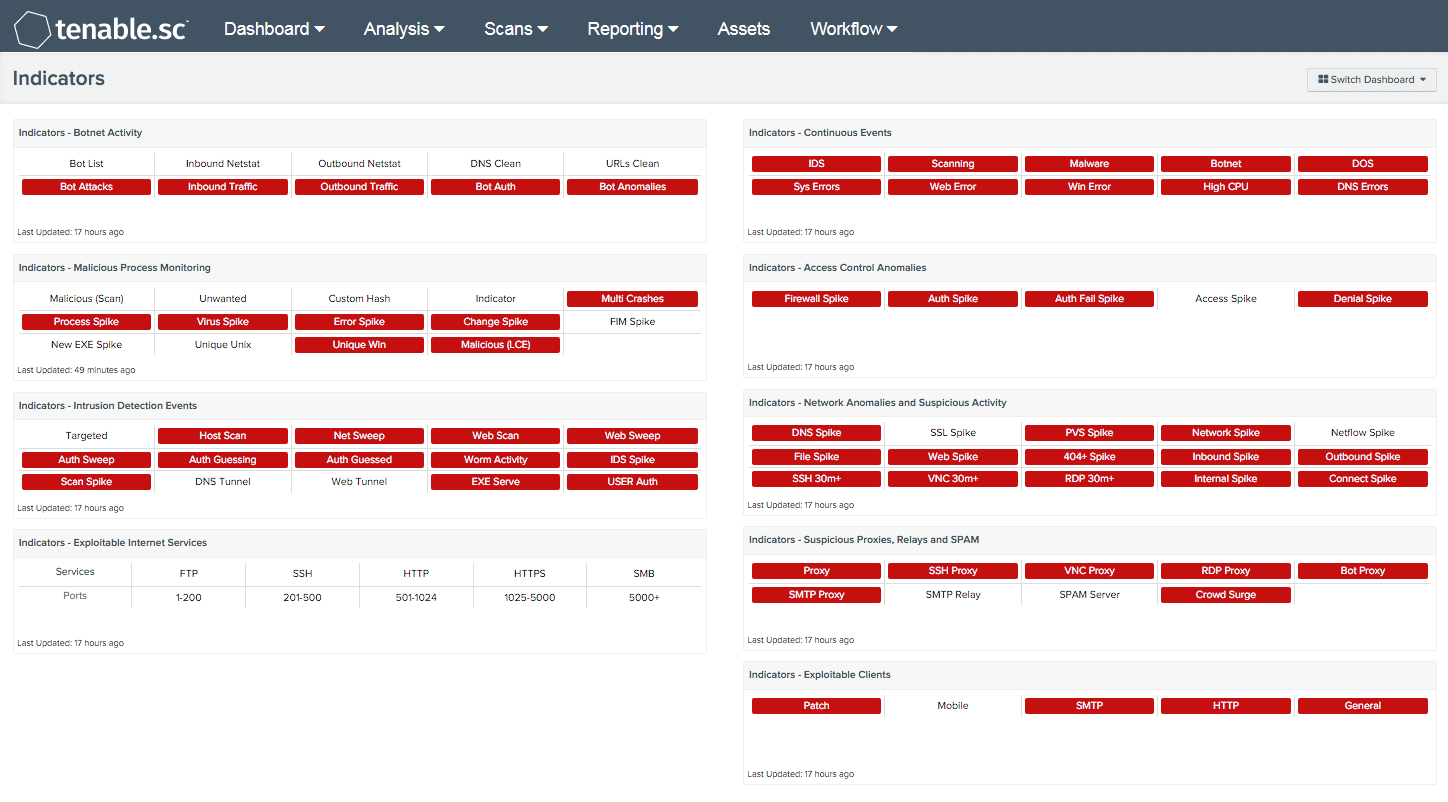
The Indicators dashboard displays close to 100 different IOC and suspicious activity alerts based on malicious file hashes, anomalies in network traffic, correlated attacks, and much more. Each dashboard element is identified with a single phrase, which will turn red when a particular query has active results. Queries and refresh times should be defined for the organization’s needs and requirements.
Triggered indications provide clues to unusual activity, which help analysts spot attacks quickly, and within the earliest stage possible. Early detection helps identify threats and mitigate potential security risks before attackers can take full advantage of them.
Many of the different types of techniques utilized in this dashboard have been discussed on the Tenable blog, the Discussions Forum, or have been covered in detailed papers in our Whitepapers section of our website, such as the LCE Correlation, CIS Critical Security Controls, or the Strategic Malware Auditing papers.
The dashboard requirements are:
- Tenable.sc 5.0.1
- LCE 6.0.0
- Nessus 8.5.1
- NNM 5.9.0
Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new types of regulatory compliance configuration audits. LCE correlates real-time events, such as DNS queries, and then performs analysis to discover vulnerabilities and Indicators of Compromise (IOC). Tenable.sc CV includes active vulnerability detection with Nessus and passive vulnerability detection with Nessus Network Monitor (NNM). LCE also has the capability to discover users, operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and other critical infrastructure. Tenable.sc CV allows for the most comprehensive and integrated view of network health.
The dashboard contains the following components:
- Indicators - Botnet Activity - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot.
- Indicators - Malicious Process Monitoring - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot. This component is included in dashboards related to the 2015 Verizon Data Breach Investigation Report (DBIR).
- Indicators - Intrusion Detection Events - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot.
- Indicators - Exploitable Internet Services - This component indicates when NNM has detected any Internet facing exploitable services. This component is included in dashboards related to the 2015 Verizon Data Breach Investigation Report (DBIR).
- Indicators - Continuous Events - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot.
- Indicators - Access Control Anomalies - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot.
- Indicators - Network Anomalies and Suspicious Activity - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot.
- Indicators - Suspicious Proxies, Relays and SPAM - This component takes many of the various detection technologies for botnets, malicious file hashes, anomalous network traffic, spikes in system logs, and continuous scanning activity and places them into one spot. This component indicates when LCE has detected any general suspicious proxy events
- Indicators - Exploitable Clients - This component indicates when a Nessus patch audit found any exploitable vulnerabilities against clients.