by David Schwalenberg
February 18, 2015
Data leakage happens when private data ends up in places it should not be, either by accident or by malicious intent. Data leakage is especially concerning for those entities that deal with financial information, credit cards, and personally identifiable information (PII). Data leakage can lead to loss of sensitive information, identity theft, and financial loss.
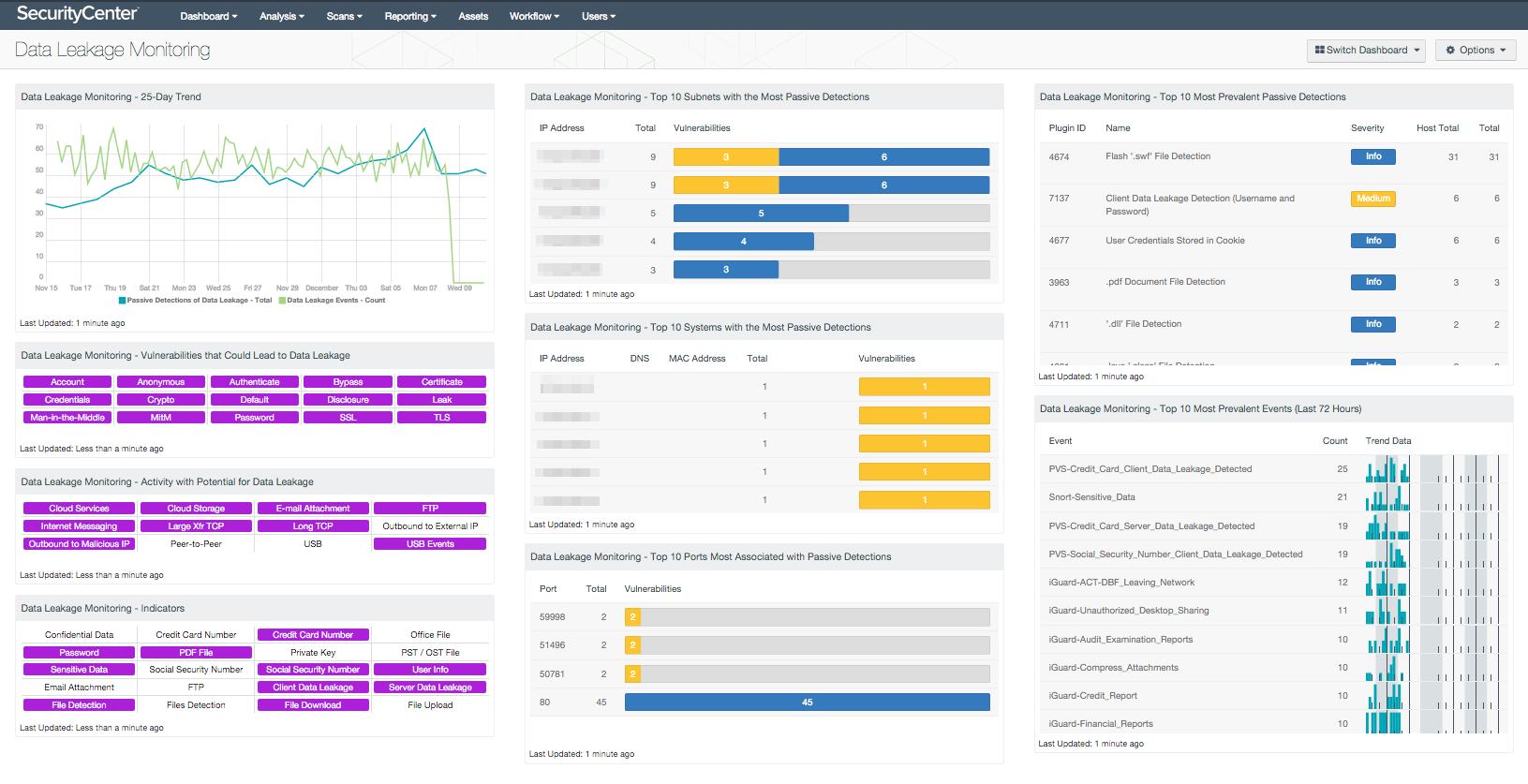
This dashboard brings together many sources of information to allow an organization to monitor its network for data leakage, as well as detect vulnerabilities and activity on the network that could lead to data leakage. The Passive Vulnerability Scanner (PVS) analyzes data in motion and can identify sensitive data, such as credit card numbers, as well as general types of documentation sharing. Logged events from Data Loss Prevention (DLP) systems can be forwarded to the Log Correlation Engine (LCE). Nessus scans can identify vulnerabilities that could lead to data leakage. The information presented in this dashboard can assist the organization as it seeks to reduce its chances of data leakage by securing systems (e.g., critical servers and point-of-sale systems) and by monitoring for suspicious activity.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.2
- Nessus 6.1.1
- PVS 4.0.3
- LCE 4.4.1
Tenable's SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus and passive vulnerability detection with Tenable’s Passive Vulnerability Scanner (PVS), as well as log correlation with Tenable’s Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network.
Listed below are the included components:
- Data Leakage Monitoring - 25-Day Trend - This chart presents a 25-day data trend of both passive detections of data leakage and logged data leakage events. The passive detections are vulnerabilities reported by PVS in the 'Data Leakage' plugin family. The logged events are reported by LCE under the ‘data-leak’ event type. This component can be used to determine if any data leakage activity has occurred over the last 25 days.
- Data Leakage Monitoring - Vulnerabilities that Could Lead to Data Leakage - This component presents indicators by keyword for actively and passively detected vulnerabilities that could lead to data leakage. Vulnerabilities at all severity levels except Informational are included. The keywords cover disclosures, cryptographic issues, man-in-the-middle vulnerabilities, and weak authentication concerns. A purple indicator means that one or more vulnerabilities contain the keyword. Clicking on the indicator will bring up the analysis screen to display details on the vulnerabilities. In the analysis screen, setting the tool to IP Summary will display the systems on which the vulnerabilities are present. This component can be used to investigate vulnerabilities that could lead to data leakage.
- Data Leakage Monitoring - Activity with Potential for Data Leakage - This component presents indicators for activity detected on the network that has the potential for data leakage. The indicators are based on events logged in the last 72 hours and on actively and passively detected vulnerabilities. Indicators are included for such things as cloud interaction, outbound traffic to external IP addresses, peer-to-peer file sharing vulnerabilities, and USB usage. A purple indicator highlights a vulnerability/event detection. Clicking on a highlighted indicator will bring up the analysis screen to display details on the vulnerabilities/events. In the analysis screen, setting the tool to IP Summary will display the systems on which the vulnerabilities/events are present. This component can be used to investigate the potential for data leakage.
- Data Leakage Monitoring - Indicators - This component presents warning indicators to draw attention to types of data that may have been leaked and methods whereby data may be leaking. These indicators make use of both passive detections and events logged within the last 72 hours. A purple indicator highlights a vulnerability/event detection. In two cases (Credit Card Number and Social Security Number), there are two indicators: one to highlight data leakage detected passively and one to highlight data leakage detected through logged events. Clicking on a highlighted indicator will bring up the analysis screen to display details on the vulnerabilities/events. In the analysis screen, setting the tool to IP Summary will display the systems on which the vulnerabilities/events are present. This component can be used to further investigate any data leakage.
- Data Leakage Monitoring - Top 10 Subnets with the Most Passive Detections - This table presents the top 10 Class C subnets with the most passive detections of data leakage. These passive detections are vulnerabilities reported by PVS in the 'Data Leakage' plugin family. The list is ordered so that the subnet with the worst data leakage is at the top. A count of detections and a bar graph indicating the severity of the detections are given for each subnet.
- Data Leakage Monitoring - Top 10 Systems with the Most Passive Detections - This table presents the top 10 systems with the most passive detections of data leakage. These passive detections are vulnerabilities reported by PVS in the 'Data Leakage' plugin family. The list is ordered so that the system with the worst data leakage is at the top. A count of detections and a bar graph indicating the severity of the detections are given for each system.
- Data Leakage Monitoring - Top 10 Ports Most Associated with Passive Detections - This table presents the top 10 ports associated with the most passive detections of data leakage. These passive detections are vulnerabilities reported by PVS in the 'Data Leakage' plugin family. The list is ordered so that the port associated with the worst data leakage is at the top. A count of detections and a bar graph indicating the severity of the detections are given for each port.
- Data Leakage Monitoring - Top 10 Most Prevalent Passive Detections - This table presents the top 10 most prevalent passive detections of data leakage. These passive detections are vulnerabilities reported by PVS in the 'Data Leakage' plugin family. A count of detections is given for each vulnerability; the list is ordered so that the vulnerability with the greatest number of detections is at the top. The severity of the vulnerability and a count of hosts on which the vulnerability was observed are also given for each vulnerability.
- Data Leakage Monitoring - Top 10 Most Prevalent Events (Last 72 Hours) - This table presents the most prevalent logged data leakage events in the last 72 hours. The logged events are reported by LCE under the ‘data-leak’ event type, and include events forwarded via syslog from PVS. A count of occurrences is given for each logged event; the list is ordered so that the event that occurred most often is at the top. A trend graph is also given for each event.