by Josef Weiss
November 15, 2016
Monitoring security areas such as user awareness, access control, and data leakage, and their effectiveness within a network can be overwhelming for any organisation to manage effectively. Unknown threats and malicious activity could potentially lead to data leakage, vulnerabilities, and damage to critical systems. The Australian Prudential Regulation Authority (APRA) and the associated Prudential Practice Guides (PPG) aims to assist regulated institutions by outlining prudent practices that can aid in managing security risks within specific elements of their business.
The APRA developed a series of PPGs specifically designed to address specific compliance requirements for regulated institutions. The PPG targets areas where APRA continues to identify weaknesses as part of its ongoing supervisory activities. The PPG does not seek to provide an all-encompassing framework, or to replace or endorse existing industry standards and guidelines. Subject to meeting APRA’s prudential requirements, regulated institutions have the flexibility to manage security risk in IT in a manner best suited to achieving their business objectives. Not all of the practices outlined in this prudential practice guide will be relevant for every regulated institution and some aspects may vary depending upon the size, complexity, and risk profile of the institution. The CPG 234 - Management of Security Risk in Information and Information Technology PPG guide was developed to provide guidance for management and IT security specialists in identifying, targeting, and managing IT security risks.
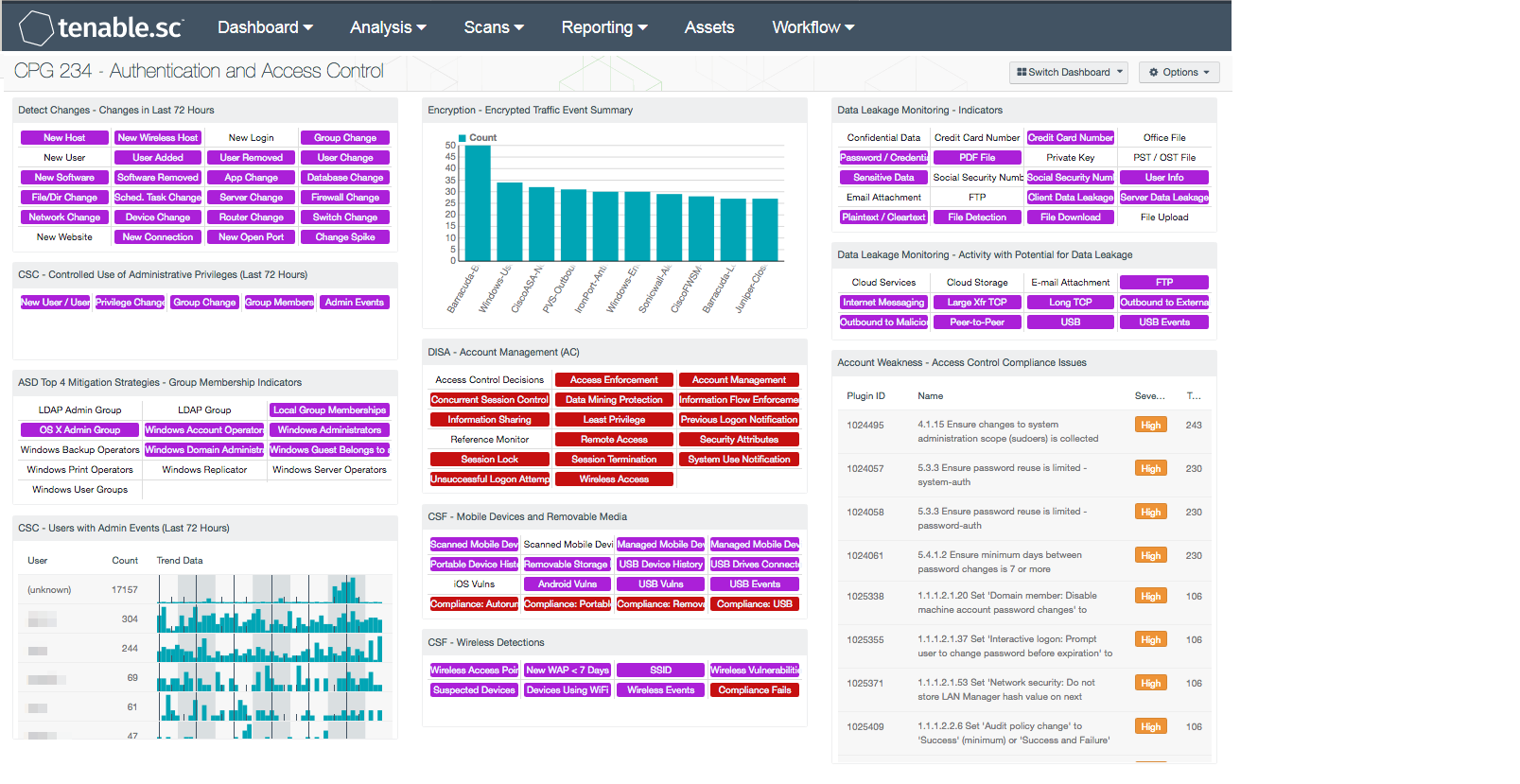
This dashboard covers key concepts within the CPG 234 guide on CPG 234 guide on authentication and access control. This dashboard addresses topics such as access control and data and information leakage. These concepts directly align with 21 mitigation strategies from the Australian Signals Directorate (ASD) Top 35 mitigation strategies framework. Included are components that assist the analyst in identifying vulnerability and compliance concerns related to access control and data and information leakage. The data presented further allows organisations to take a systematic and formalized approach to data risk management.
Additionally, these concepts also align with 21 mitigation strategies from the Australian Signals Directorate (ASD) Top 35 mitigation strategies framework that address patch management vulnerabilities, suspicious behaviour, encryption concerns, and effectiveness of existing controls. Components will alert institutions to gateway and perimeter concerns, inbound and outbound threats, account and access control concerns, and remediation opportunities.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.0
Tenable Network Security transforms security technology for the business needs of tomorrow through comprehensive solutions that provide continuous visibility and critical context, enabling decisive actions to protect the organisation. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. Active scanning examines running systems and services, detects vulnerable software applications, and analyses configuration settings. Passive listening collects data to continuously monitor traffic, collect information about user privilege changes, and administrative activity, along with the discovery of additional vulnerabilities. Monitoring the network to ensure that all systems are secured against vulnerabilities is essential to ongoing security efforts. Tenable enables powerful, yet non-disruptive, continuous monitoring that will enable organisations with the information needed to proactively respond to threats within the enterprise.
The dashboard contains the following components:
- Detect Changes - Changes in Last 72 Hours - This component assists in maintaining up-to-date inventories and detecting changes.
- CSC - Controlled Use of Administrative Privileges (Last 72 Hours) - This component presents indicators of events related to user accounts and administrative privilege use. Indicators are included for new user and user account change events, privilege change events, and group and group membership change events.
- ASD Top 4 Mitigation Strategies - Group Membership Indicators - This Group Membership component is a matrix of saved queries, which quickly identifies plugins that match on group membership settings.
- CSC - Users with Admin Events (Last 72 Hours) - This table presents those users associated with events that indicate performed or attempted administrative actions.
- Encryption - Encrypted Traffic Event Summary – The Encrypted Traffic Events chart presents an overview of encrypted session activity within the last 72 hours.
- DISA - Account Management (AC) - This matrix provides indicators for failed audit checks that are members of the Account Management (AC) NIST 800-53 and related Control Correlation Identifiers (CCI).
- CSF - Mobile Devices and Removable Media - This component assists an organisation in monitoring mobile devices and removable media.
- CSF - Wireless Detections - This component presents a breakdown of detected wireless access points, wireless vulnerabilities, and wireless event activity on the network.
- Data Leakage Monitoring – Indicators - This component presents warning indicators to draw attention to types of data that may have been leaked and methods whereby data may be leaking.
- Data Leakage Monitoring - Activity with Potential for Data Leakage - This component presents indicators for activity detected on the network that has the potential for data leakage.
- Account Weakness - Access Control Compliance Issues - This component displays a table of compliance checks related to an organisation's access control.