by Cody Dumont
April 25, 2016
Overlooking threat vectors in an organization can be disastrous, and network infrastructure such as routers and switches often escape the purview of vulnerability scans. Scanning network infrastructure devices is important; however, most of the useful information collected from these devices is gained through log collection. This dashboard provides a centralized view of vulnerability and log data collected on Cisco devices such as routers, switches, and firewalls.
Performing vulnerability scans on Cisco devices is perfectly safe. However, there is a stigma surrounding vulnerability scanning a router, switch and firewall. Due to this stigma, Cisco devices are often regulated to being scanned on monthly basis and in very limited time windows. Creating targeted scan policies and only scanning the necessary devices can help reduce the negative stigma and allow the network team to become more comfortable with the vulnerability scanning of Cisco devices.
In addition to vulnerability scanning, SecurityCenter comes with many audit files for Cisco devices. The audit files are automatically updated as part of the SecurityCenter plugin feed, and are now easily downloaded using the templates provided in SecurityCenter GUI. The audit files support checks against DISA STIGs, CIS Configuration Guides, and other documented best practices. SecurityCenter also supports editing audit files using a new GUI interface where key values such as NTP Server, Logging Server, and other settings can be easily modified. Once downloaded, audit files can be manually edited and re-imported into SecurityCenter. By adding audit files to vulnerability scans, the network team can obtain information of potential configuration vulnerabilities found in the Cisco device configurations.
During the times between vulnerability and audit scans, the Passive Vulnerability Scanner (PVS) can detect over 100 Cisco vulnerabilities, such as ACL bypass, shell detection, SNMP configuration, VPN detections, and TFTP usage. In addition to PVS, the Log Correlation Engine (LCE) can also be used to collect logs and NetFlow from Cisco devices. By collecting logs, LCE can identify Cisco devices, software version, and other possible vulnerabilities. LCE also normalizes over 1000 syslog events for easier analysis and threat detection.
When incorporating SecurityCenter Continuous View (CV) into the daily operations of both the network team and security team, the overall improvement of security will increase. Using vulnerability and audit scans, along with PVS and log collection, the organization will be able to gain a clear view of the risks and security concerns of the Cisco devices.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 5.1.0
- Nessus 6.5.6
- LCE 4.8.0
SecurityCenter Continuous View (CV) is the standard by which other solutions should measure themselves. SecurityCenter CV provides continuous network monitoring to identify vulnerabilities, reduce risk, and ensure compliance. Continuous monitoring with SecurityCenter CV allows for the most comprehensive and integrated view of network health. SecurityCenter CV supports more technologies than any other vendor including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. The tight integration of vulnerability analysis, compliance review, and log correlation can help to make your Cisco network infrastructure more secure and stable.
Components
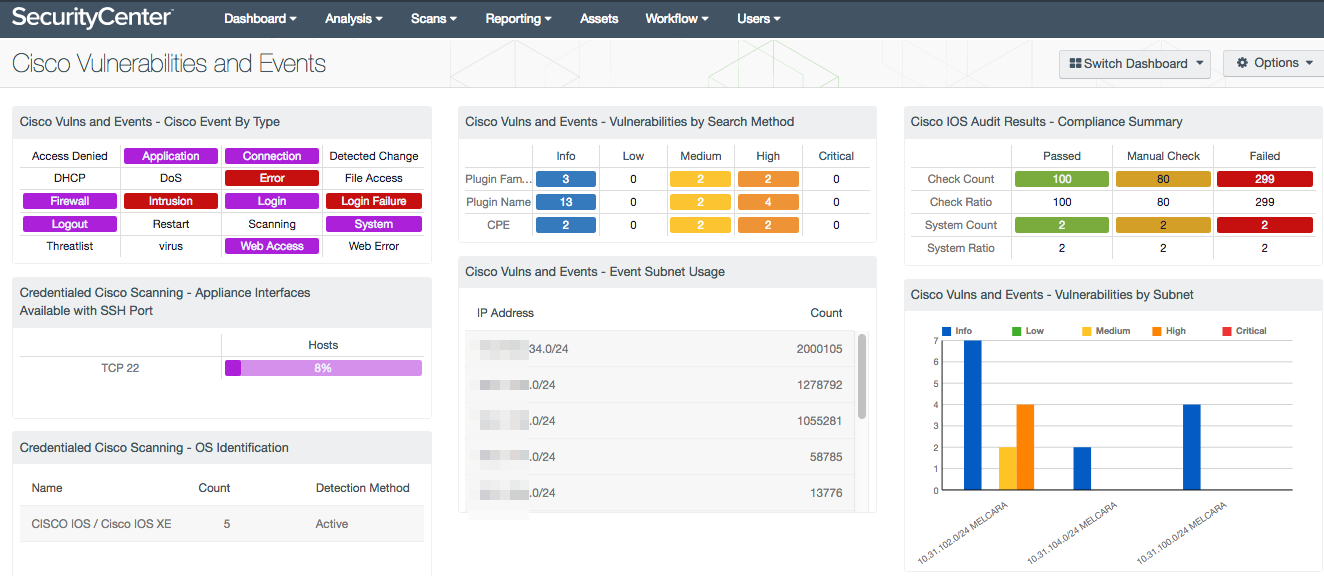
Cisco Vulns and Events - Cisco Event By Type: This matrix provides indicators for the event types attributed to Cisco events. The indicators provide an easy-to-use method for analyzing log data.
Credentialed Cisco Scanning - Appliance Interfaces Available with SSH Port: This matrix component indicates the percentage of Cisco hosts with vulnerabilities discovered on TCP port 22 (SSH). Nessus uses Secure Shell (SSH) for credentialed scans on Cisco devices. Nessus supports three types of authentication methods for use with SSH: username and password, public/private keys, and Kerberos. If SSH servers are running on another port, the scan policies will need to be modified, and the filter in this matrix will need to be modified to reflect the correct SSH service port.
Credentialed Cisco Scanning - OS Identification: This table component displays the various Cisco appliances being audited with credentialed scans. This table is sorted by OS count and displays the OS version, count, and detection method. This information is useful to an analyst who needs to know the number of Cisco platforms that are being scanned in the network environment. This component filters using passive and active plugins to locate all Cisco systems. The OS Identification plugins use several techniques to identify the OS, with differing levels of confidence. This component uses the vulnerability text string “cisco” in conjunction with plugin IDs.
Cisco Vulns and Events - Vulnerabilities by Search Method: This matrix provides an easy and effective method to locate all Cisco related vulnerabilities, using three common search methods. The first method uses the Plugin Family as the filter, which is comprised of Active plugins. Active plugins are used by Nessus to identify vulnerabilities. The second row uses the Plugin Name, which encompasses Active, Passive, and Event based plugins. The third row uses Common Platform Enumeration (CPE) as the search string to identify vulnerabilities. This method is useful for finding software components such client software or packages that may be manufactured by Cisco, but do not use Cisco in the name of the product.
Cisco Vulns and Events - Event Subnet Usage: This table provides a summary by subnet of logs attributed to a subnet where hosts reside. The component searches for Cisco in the Normalized Event name, and then summarizes the based on a 24 Bit Classless Inter-Domain Boundary (CIDR). The analysts should monitor this component for sudden changes over time and then investigate as necessary.
Cisco IOS Audit Results - Compliance Summary: When performing configuration audit of systems in accordance with a GRC program, security analysts can benefit from a summary view of the data set. The Cisco IOS Compliance Summary table provides a high-level view of the Cisco IOS compliance status.
Cisco Vulns and Events - Vulnerabilities by Subnet: This chart provides a summary by subnet for the top 10 most vulnerable subnets with respect to Cisco vulnerabilities. The chart uses the searches with Plugin Name filter of “Cisco” and the returns the results for each subnet along with a 24 Bit Classless Inter-Domain Boundary (CIDR).