by Cody Dumont
April 14, 2015
The Cisco ASA firewall has the ability to log all sessions, Access Control List (ACL) actions, VPN connections, and several other events. If these types of logs are not normalized, they would be virtually unusable due to the sheer quantity of events. Fortunately SecurityCenter Continuous View (CV) uses the Log Correlation Engine (LCE) to normalize Cisco ASA logs into several events across 18 different event types. Additionally, the LCE statistics engine also tracks normalized events.
The LCE statistics engine keeps an average count (using all collected data) of Cisco ASA events per hour for each IP address. This enables LCE to 'learn' the average count of events for certain times of the day. If for a certain hour, the count of failed login attempts is significantly more or less than the average for that hour, an anomaly event is triggered. Counts of events per hour are not compared to other hours to generate anomalies; a count is compared only to the average count of events for that specific hour for days in the past. Thus, an anomaly is a deviation from what historically occurred at that time of day, not a deviation from what occurred earlier in the day.
The advantages gained by SecurityCenter CV users are not limited to log analysis. Using the Passive Vulnerability Scanner (PVS), the organization can monitor for VPN client usage and RADIUS systems from the firewalls to the appropriate servers. Using Active and Compliance scanning, the Nessus vulnerability scanner provides the ability to identify vulnerabilities in the ASA operating system and in VPN clients, such as AnyConnect and WebVPN.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.2
- Nessus 6.2.1
- LCE 4.4.1
- PVS 4.2.0
SecurityCenter CV allows for the most comprehensive and integrated view of network health. SecurityCenter CV provides a unique combination of detection, reporting, and pattern recognition, utilizing industry recognized algorithms and models. SecurityCenter CV utilizes the Log Correlation Engine (LCE) to provide deep log and event inspection to continuously discover and track users, applications, and authentication events. Nessus and PVS provide the ability to analyze configurations using both Active and Passive detection methods. SecurityCenter CV tightly integrates with SIEMs, log management tools, malware defenses, the PVS network sensor, NetFlow, BYOD, firewalls, web, and authentication systems.
Components
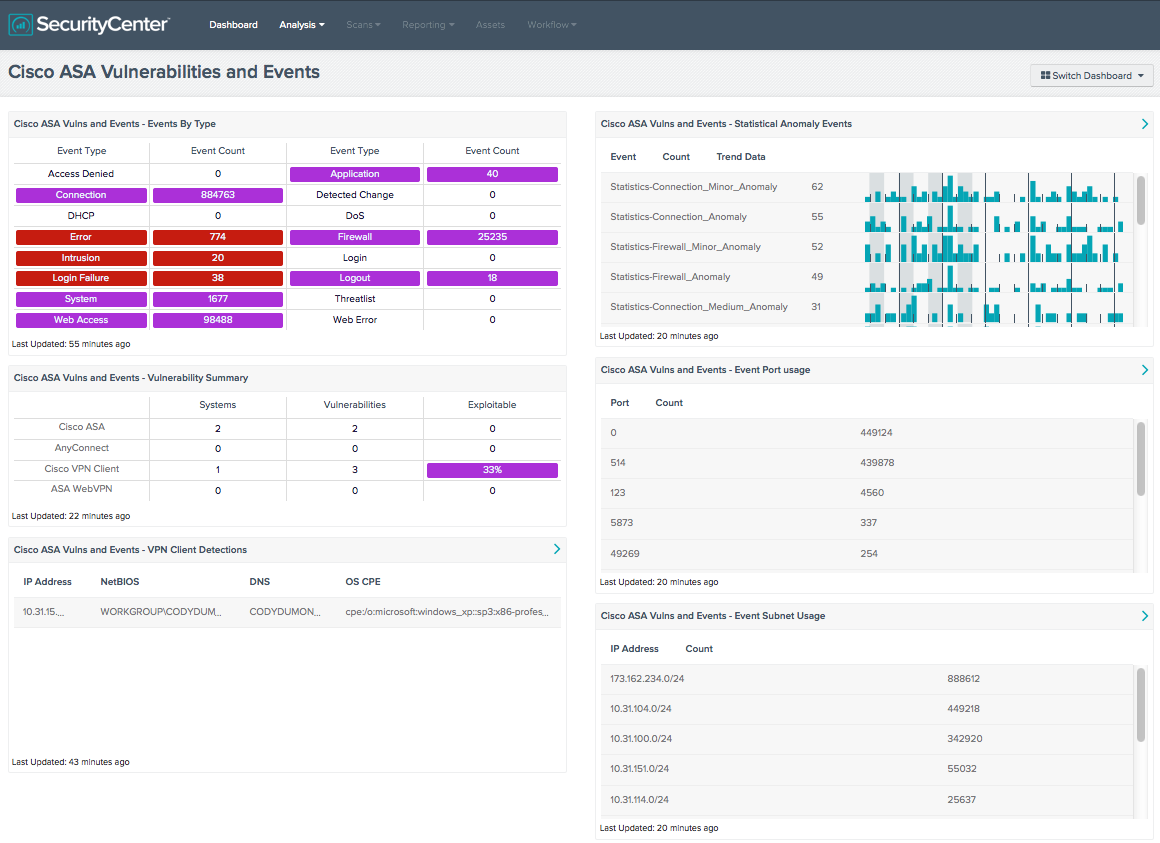
Cisco ASA Vulns and Events - Events By Type: This matrix component provides a summary of the event types collected from the Cisco ASA firewall. Analysts can monitor these logs to obtain an understanding of firewall events collected over the past 72 hours.
Cisco ASA Vulns and Events - Vulnerability Summary: This matrix provides counts of vulnerabilities discovered in the Cisco ASA or in VPN clients used by an ASA. The Cisco ASA and VPN client software performs critical roles in the security of an organization. Due to its critical nature, this component provides a deep insight of overall risk to an organization.
Cisco ASA Vulns and Events - VPN Client Detections: This table uses several VPN client detection plugins to provide a list of machines with a Cisco VPN Client installed.
Cisco ASA Vulns and Events - Statistical Anomaly Events: This table provides a list of statistical anomaly events identified as Cisco ASA events.
Cisco ASA Vulns and Events - Event Port Usage: This table provides a port count based on the connection events collected from Cisco ASA firewalls. The Cisco ASA tracks all communications using the XLATE table. The XLATE table tracks the IP addresses, network interfaces, and communication ports. The XLATE tables are logged using the “create translation” normalized events.
Cisco ASA Vulns and Events - Event Subnet Usage: This table provides a subnet usage summary based on the connection events collected from Cisco ASA firewalls.