by Ron Gula
July 16, 2015
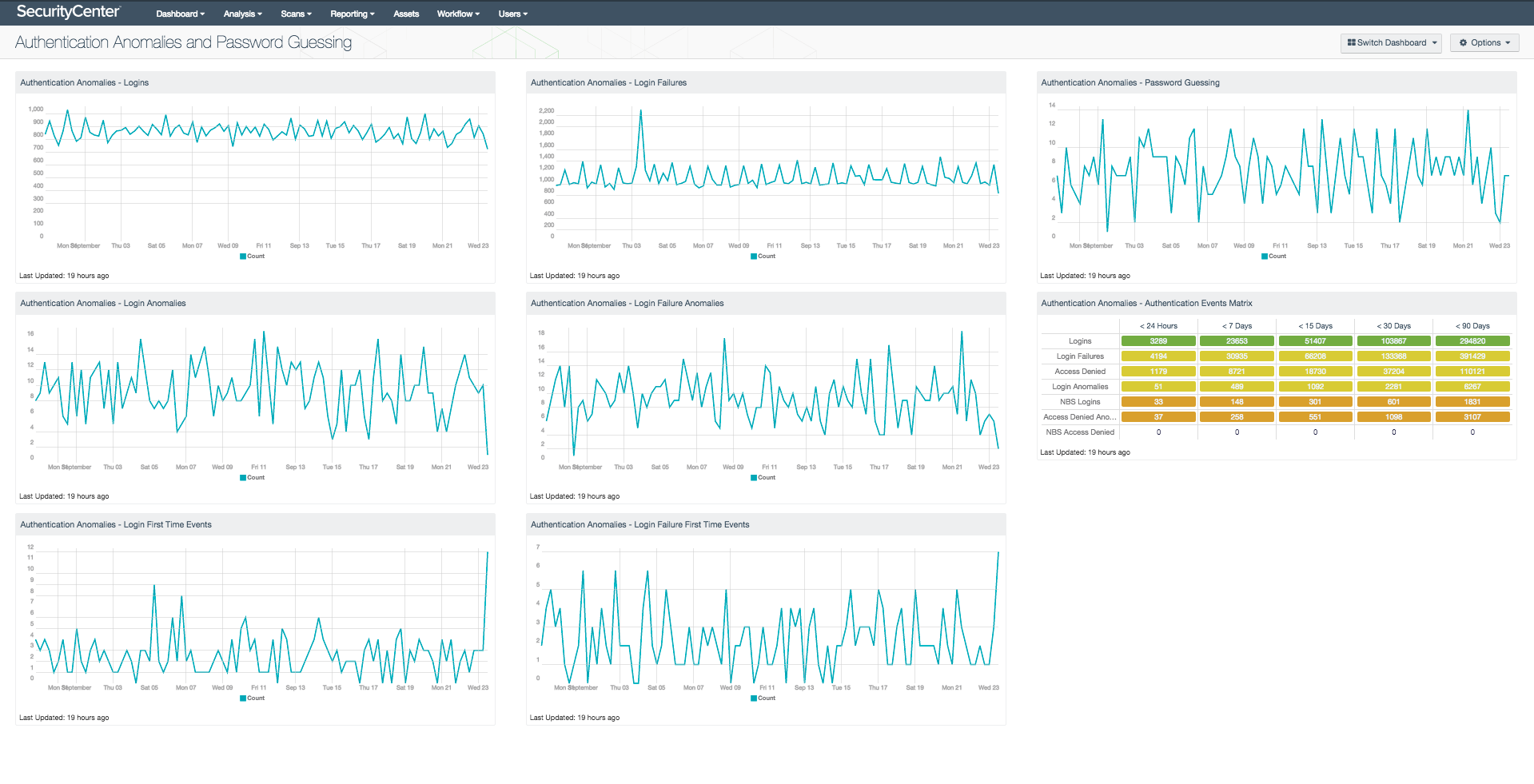
Anomalies in authentication behavior can indicate changes in network usage. These changes may be due to new applications or new servers, or they may be due to attackers and compromised systems. This dashboard displays trend charts for login, login failure, and password guessing events and anomalies in the last 25 days, to enable an analyst to quickly spot potentially suspicious activity and allow further investigation.
The Log Correlation Engine (LCE) normalizes logs that indicate successful authentication attempts to the 'login' event type. The 'login-failure' event type is used to classify failures to authenticate. This dashboard leverages these event types, as well as the corresponding anomalies detected by the LCE stats daemon and the never-before-seen alerting, to identify potentially suspicious authentication attempts.
Never before seen login and login failure events occur most often when new hosts or servers are added to the network and authentication logs are received from them for the first time. In addition, new types of authentication will generate logs that have not been seen before. For example, the first time a user logs in via VNC instead of Windows Terminal Services (RDP), a new event will be generated. These new events indicate changes in access patterns and can indicate new behaviors from existing users, or potentially from hackers or insiders.
Statistical anomalies in login failures can also indicate subtle types of brute force password guessing. The LCE does detect brute force password guessing, and these events are charted in the 'Password Guessing' component. However, this type of correlation is rate-based within a certain time period. The stats daemon's login failure analysis is more in-depth and will identify many common forms of low-and-slow password guessing that don't create a large amount of login failures.
If trending over a shorter or longer period of time is desired, the components in this dashboard can be edited and the Date Range field can be adjusted.
The dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, assurance report cards and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.2
- LCE 4.4.1
SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring platform. SecurityCenter CV includes active vulnerability detection with Nessus and passive vulnerability detection with the Passive Vulnerability Scanner (PVS), as well as log correlation with the Log Correlation Engine (LCE). Using SecurityCenter CV, an organization will obtain the most comprehensive and integrated view of its network.
Listed below are the included components:
- Authentication Anomalies - Logins - This chart displays the trend of login events in the last 25 days. Any type of login event is included, such as to an application, operating system, VPN, firewall, or other type of device.
- Authentication Anomalies - Login Failures - This chart displays the trend of login failure events in the last 25 days. A login failure event is any type of authentication log that indicates credentials were presented and were incorrect. This is distinct from application logs that show an IP address was blocked or access to a resource was denied. Those events are logged under event types of 'firewall' or 'access-denied', respectively.
- Authentication Anomalies - Password Guessing - This chart displays the trend of password guessing events in the last 25 days. A password guessing event is generated by LCE when a large number of failed logins to the same IP address are detected. This could indicate brute force password guessing against the host.
- Authentication Anomalies - Login Anomalies - This chart displays the trend of login anomaly events in the last 25 days. A login anomaly event is generated by LCE when a large number of login events are detected relative to the number of login events detected during that hour in previous days. A spike in login activity indicates a change in network behavior and may indicate malicious over-usage of an account, such as when hackers share compromised account information.
- Authentication Anomalies - Login Failure Anomalies - This chart displays the trend of login failure anomaly events in the last 25 days. A login failure anomaly event is generated by LCE when a large number of login failure events are detected relative to the number of login failure events detected during that hour in previous days. A spike in login failure activity indicates a change in network behavior and may indicate brute force password guessing.
- Authentication Anomalies - Login First Time Events - This chart displays the trend of Never Before Seen (NBS) login events in the last 25 days. Never before seen login events occur most often when new hosts or servers are added to the network and authentication logs are received from them for the first time. In addition, new types of authentication (such as a user logging in via VNC instead of Windows Terminal Services for the first time) will generate logs that have not been seen before. These never before seen events indicate changes in access patterns and can indicate new behaviors from existing users, or potentially from hackers or insiders.
- Authentication Anomalies - Login Failure First Time Events - This chart displays the trend of Never Before Seen (NBS) login failure events in the last 25 days. Never before seen login failure events occur most often when new hosts or servers are added to the network and authentication logs are received from them for the first time. In addition, new types of authentication (such as a user logging in via VNC instead of Windows Terminal Services for the first time) will generate logs that have not been seen before. These never before seen events indicate changes in access patterns and can indicate new behaviors from existing users, or potentially from hackers or insiders.
- Authentication Anomalies - Authentication Events Matrix - This matrix displays the counts of various authentication-related events over time. The columns are filtered by timeframe and the rows reflect the counts of particular event types and normalized events. The data illustrated by this component can be used to track the occurrence of authentication events and anomalies.