Upgrading from Nessus to SecurityCenter: Dynamic Asset Lists Drive Action
Note: Tenable SecurityCenter is now Tenable.sc. To learn more about this application and its latest capabilities, visit the Tenable.sc web page.
Most of us involved with vulnerability management have probably used a Nessus® filter to display specific reporting results. For example, I have used a query to select all of the Windows servers in an environment, and then report on the high and critical severity vulnerabilities. Queries like this focus analysis and increase insight from reports. Report queries are useful for vulnerability management – so valuable that their usage raises two questions in my mind.
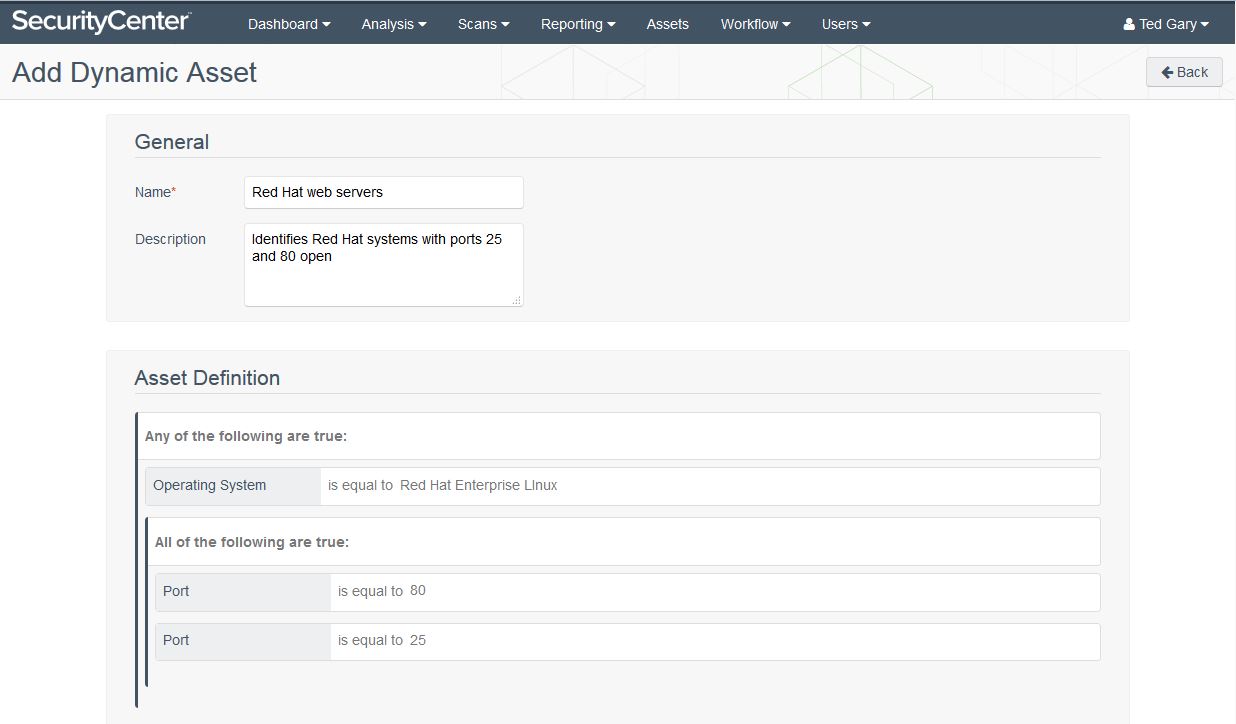
First, can we apply queries across the entire vulnerability management process, instead of just during reporting? For example, can we define a query to refine assessments of specific assets; perhaps select Red Hat web servers running in a DMZ and then configure a vulnerability scan and tailored configuration audit to assess those systems every day?
Second, can we use queries to define criteria for grouping assets that will be automatically applied to newly discovered assets? For example, when new web servers are deployed, will the vulnerability scan and configuration audit defined above automatically detect and assess the new systems?
SecurityCenter’s dynamic asset list feature applies across the vulnerability management process
SecurityCenter’s dynamic asset list feature applies across the vulnerability management process. Plus, it automatically adds newly discovered assets to all applicable asset lists. SecurityCenter™ has the ability to parse the results of Nessus, PVS™, or LCE® event data to build dynamic lists of assets, and a single asset can be a member of multiple asset lists. For example, a dynamic rule can be created to generate a list of IP addresses that has ports 25 and 80 open. These rules can be very sophisticated and take into account addressing, open ports, specific vulnerability IDs, and discovered vulnerability content.
Intuitive forms guide dynamic asset list creation
Dynamic asset lists also direct multiple SecurityCenter functions. They can be paired with user permissions to control SecurityCenter scanning, manage blackout windows, and inform workflow. As an example application: if SecurityCenter finds a critical, exploitable vulnerability on a Red Hat web server, it can notify the system administrator responsible for the asset list via email or a ticket.
Dynamic asset lists inform reports, dashboards, and Assurance Report Cards (ARCs)
And of course, dynamic asset lists inform reports, dashboards, and Assurance Report Cards (ARCs). The Critical and Exploitable Vulnerabilities report could easily be configured to run against the Red Hat web server asset list after each daily scan, and the results could automatically be emailed to the appropriate stakeholders. Dynamic asset lists can focus dashboards to display a complete security and compliance view for all the assets in the DMZ. This view could show vulnerability trends over time, vulnerability ages, configuration compliance and more.
Dashboards can focus on a specific asset list
SecurityCenter includes more than 200 dynamic asset list templates that you can use out of the box or you can tailor for your specific requirements. Additionally, you can easily create your own templates using a web-based wizard.
You can also create dynamic asset lists on the fly and apply them to existing SecurityCenter data
You can also create dynamic asset lists on the fly and apply them to existing SecurityCenter data. Consider this hypothetical example: it is Friday at 4:00 p.m. and you are looking forward to going away on a weekend skiing trip. However, a new vulnerability, Heartshock, has just been publicly announced that affects FTP services on Red Hat systems 6.4 and older. You can quickly create an asset list to identify any systems in your environment that might ruin your weekend plans. What’s really amazing is that this asset list doesn’t require a new scan! Rather, it will run against data already collected by SecurityCenter. You can have results in seconds, and if any vulnerable systems are identified, you can notify the appropriate system administrators in minutes. Weekend saved!
SecurityCenter’s dynamic asset lists let you slice and dice your assets as you need to automate much of your security and compliance program. To learn more about them, plan to attend our upcoming webcast on Four Ways You Can Make Vulnerability Management More Efficient and Effective.
Learn more
- Nessus
- SecurityCenter
- Vulnerability Management
- Vulnerability Scanning





Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success