ISO / IEC 27001 / 27002
Facilitate ISO 27000 Technical Control Implementation
The ISO/IEC 27001/27002 frameworks are internationally recognized best practice standards that enhance information security by enabling organizations to identify risks and implement appropriate controls.
Many organizations, especially multinationals, have chosen to utilize ISO/IEC 27001/27002 frameworks to help them continually identify security gaps, comply with numerous compliance requirements and obtain international certification.
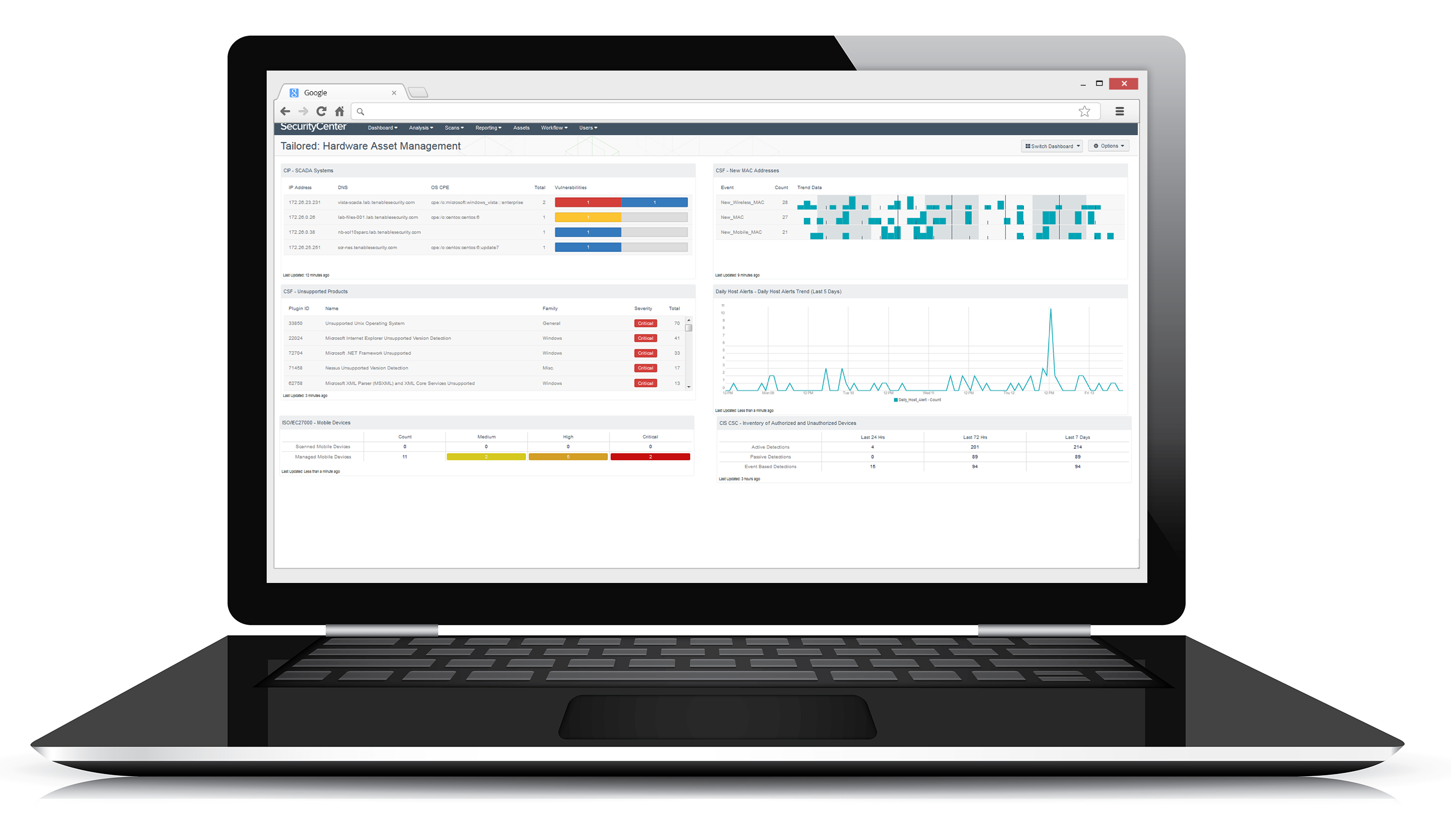
Tenable Security Center provides an automated approach to implementing and maintaining many technical controls included in an Information Security Management System based on ISO/IEC 27001/27002 (ISO-27K) standards. It provides both active and passive monitoring to provide stakeholders with near real-time visibility of technical control status. In addition, you can use its out-of-the-box reports, dashboards and Assurance Report Cards® (ARCs) to simplify your ability to track and demonstrate conformance.
Get the Solution Story
Security Frameworks & Tenable
Learn how Tenable Security Center automates and continuously monitors technical controls.
Advanced Security With Tenable
Tenable Security Center collects data from multiple sensors to provide advanced analysis of vulnerability, threat, network traffic and event information and deliver a continuous view of IT security across your environment. It gives you the information you need to continuously adapt and improve your security posture to protect your organization.
Broadest Coverage
Supports most technical controls prescribed in the NIST CSF, ISO/IEC 27002 and CIS CSC frameworks, and builds them into an automated control foundation for managing risk and securing the business.
Continuous Visibility
Use active scanning combined with continuous listening to obtain a complete view of control conformance across your environment.
Analyze Third-Party Security Products
Audit configurations of many third-party products and analyze events generated by them to identify control weaknesses.
Dynamic Asset Grouping
Focus dashboards to display a complete security and compliance view for services in your industrial control system and IT networks, including physical and virtual infrastructure, cloud and mobile environments.
Measure, Visualize and Communicate Adherence to Controls
Easily measure, visualize and understand your technical control conformance status by using dashboard templates, and identify gaps between where you are and where you want to be.
Map Technical Control Status to Business Objectives
Use Tenable Security Center Assurance Report Cards to compare your current security status to the desired status and help you build a roadmap for demonstrating a defensible security program.
“35% of organizations are using ISO 27000 – 48% of organizations with more than 10,000 employees. An additional 9% expect to adopt it in the coming year.”Dimensional Research: Trends in Security Framework Adoption, March, 2016