by Josef Weiss
April 14, 2016
The Daily Command and User Summary report presents information on active users and issued commands on each reporting host. The ability to detect active users and executed commands across hosts is very useful for identifying any new changes, such as those possibly being issued maliciously.
Many types of malicious software execute commands or may even create rogue user accounts; being able to alert on issued commands and users is key in maintaining a secure environment. The Log Correlation Engine (LCE) will summarize and report all users who executed commands in the past 24 hours. This data is tracked utilizing the Daily_User_Summary event. LCE will also summarize and report all command names executed in the past 24 hours. This is tracked utilizing the Daily_Command_Summary event. The ability to identify these events can assist analysts in determining if inappropriate accounts are issuing commands, and if any unusual commands are being issued.
Auditing the commands that each host is executing each day and what user accounts are active can be administratively impossible. Tenable LCE leverages Unix and Windows clients to collect application execution logs. When monitored by the LCE, every program running on every laptop, desktop, and server is logged and gathered for automated analysis and anomaly detection. These events are normalized and forwarded to SecurityCenter. This data is of great use for alerting on behavior indicative of malicious software.
This report utilizes filters for daily user and daily commands based on normalized events from the LCE. The normalized events identified in this report are generated using TASL (Tenable Application Scripting Language). The TASL identifies active user accounts and issued command events over the last 24 hours. The report is comprised of chapters for Daily User and Daily Command summary events.
The report and its elements are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the SecurityCenter Feed under the category Monitoring.
The dashboard requirements are:
- SecurityCenter 4.8.2
- LCE 4.6.1
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. SecurityCenter CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new types of regulatory compliance configuration audits. SecurityCenter CV allows for the most comprehensive and integrated view of network health.
The dashboard contains the following components:
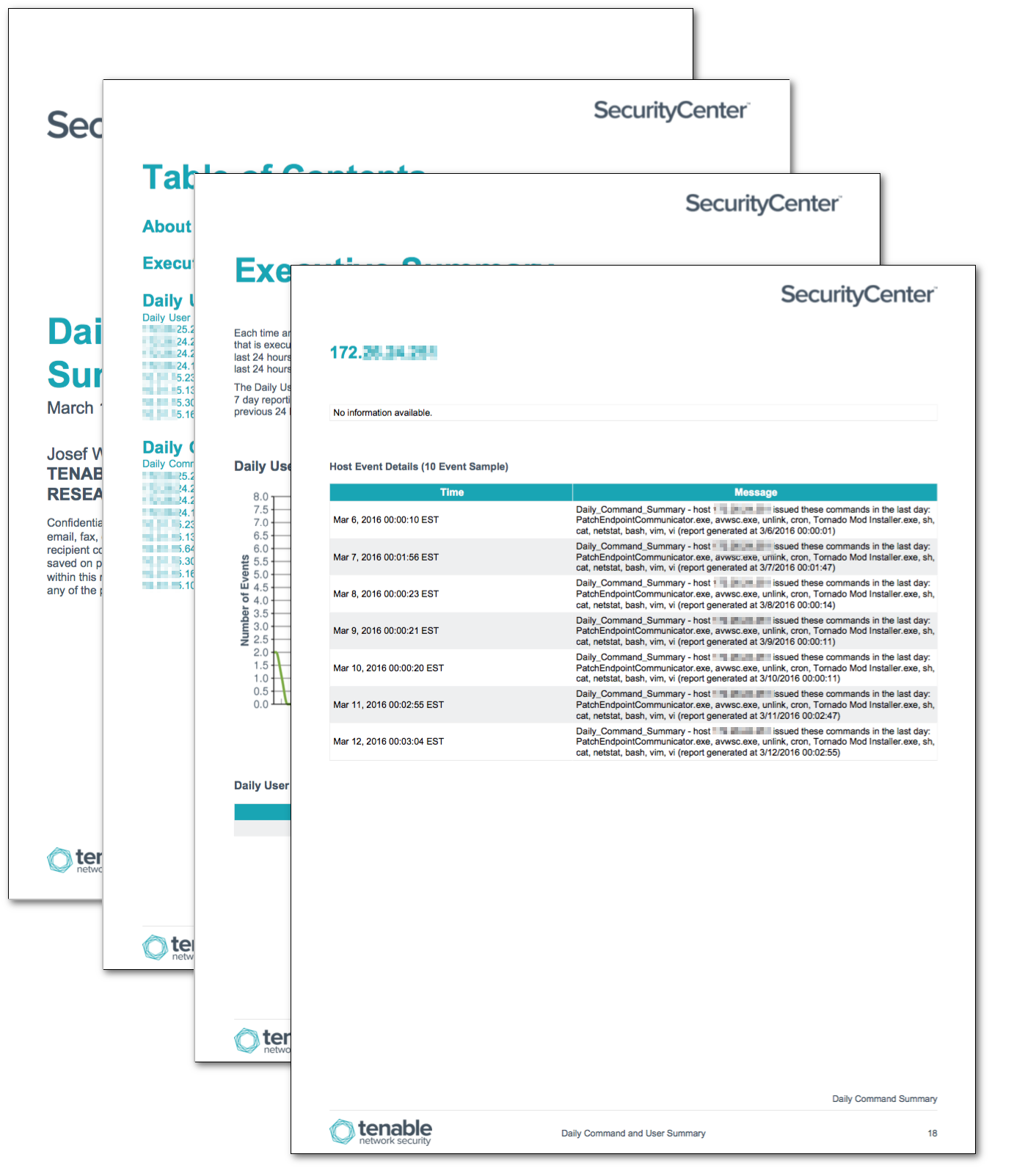
- Executive Summary - Each time an active user issues a command on a host that user account name is recorded. Each command that is executed on the host is also recorded. For each of these events the LCE keeps a global list for the last 24 hours. This chapter trends the number of hosts with Daily User and Daily Command events for the last 24 hours, trending over the last 7 days.
- Daily User Summary - When an active user account issues a command, an event is generated for Windows or Unix systems based on the system type. This chapter includes elements displaying the Class C networks and hosts, with counts, for those networks where user issuing commands have been detected. A host event table displaying the user accounts that issued commands is also presented.
- Daily Command Summary - When a command is executed, this alert is generated. This chapter includes elements displaying the Class C networks and hosts, with counts, for those networks where commands have been executed. A host event table displaying the commands executed is also presented.