by Josef Weiss
November 3, 2016
Media player applications are applications running on a host that allow for playing of multimedia files, such as movies and music. These applications include well-known programs such as Apple QuickTime, Adobe Director, RealNetworks RealPlayer, and many others, are widely available on different platforms. Many organizations utilize digital signage technologies such as LCD and projection devices, to display content such as digital images and streaming video. Digital signs can be found in airports, doctor’s offices, retail locations, corporate offices, and other locations to provide information or advertising. Many of these devices utilize some form of media player to display data, and can range from simple non-networked devices to complex enterprise-wide or campus-wide installations.
A large number of media players can also be found on desktops and laptops for an individual’s own personal use. Local IT Administrators may not control patching of third-party digital signage devices and individual installations of media player applications. Many of these applications are considered third party, and are not managed by organizational patch management solutions. This can allow for media players to become outdated and contain vulnerabilities that can be exploited.
This report presents a high-level overview of detected vulnerabilities on media player applications across the enterprise. Analysts are provided with vulnerability data, which can be easily used to assist in reducing media player application vulnerabilities.
The elements in this report leverage data gathered by active vulnerability scanning with Tenable Nessus and passive vulnerability detection with Tenable Passive Vulnerability Scanner (PVS). The data collected is filtered to provide insight into the vulnerabilities related to media players in the environment. Vulnerabilities are tracked by time, severity, and exploitability in order to provide a more complete view of the security status of the network. Security teams can use all of the components in this dashboard to assist in identifying, monitoring, and remediating vulnerabilities within media players that may expose their organization to risk.
This report uses the Common Platform Enumeration (CPE) filter to identify many of the software programs used in enterprise networks. According to NIST, the CPE is a structured naming scheme for information technology systems, software, and packages. Based upon the generic syntax for Uniform Resource Identifiers (URI), CPE includes a formal name format, a method for checking names against a system, and a description format for binding text and tests to a name. Tenable assigns CPEs to plugins where appropriate. This allows for analysts to search for common CPE prefixes such as cpe:/a:apple:quicktime, cpe:/a:adobe:director, and others. Associating CPE strings with vulnerabilities allows the analysts to separate operating system vulnerabilities from application vulnerabilities, and adds to the level of vulnerability detail provided to the organization.
This report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments.
The report requirements are:
- SecurityCenter 5.3.1
- Nessus 6.8.1
- PVS 5.0.0
- LCE 4.8.0
Tenable Network Security transforms security technology for the business needs of tomorrow through comprehensive solutions that provide continuous visibility and critical context, enabling decisive actions to protect the organization. SecurityCenter is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. Active scanning examines running processes and services, including remote access services, and detects vulnerable software applications, configuration settings, and additional vulnerabilities. Monitoring the network to ensure that all systems are secured against vulnerabilities is essential to ongoing security efforts. With more than one million users and more than 20,000 enterprise customers worldwide, organizations trust Tenable for proven security innovation. Tenable’s customers range from Fortune Global 500 companies, to the Department of Defense, to mid-sized and small businesses in all sectors, including finance, government, healthcare, higher education, retail, and energy. Transform security with Tenable, the creators of Nessus and leaders in continuous monitoring, by visiting tenable.com.
The corresponding dashboard can be found here:
Media Player Summary DashboardThe following chapters have been developed to provide a quick visual representation of the number of systems certain media player applications are installed on, the number of associated vulnerabilities, ratio of vulnerable systems, and percentage of systems with exploitable media player vulnerabilities. Vulnerability Trend displays media player application vulnerabilities over the last 90 days. By default, trend data is only stored for 30 days, and must be set to 90 days in SecurityCenter. Vulnerability observed dates are set to the last 3 days within the trend as well.
The report contains the following chapters:
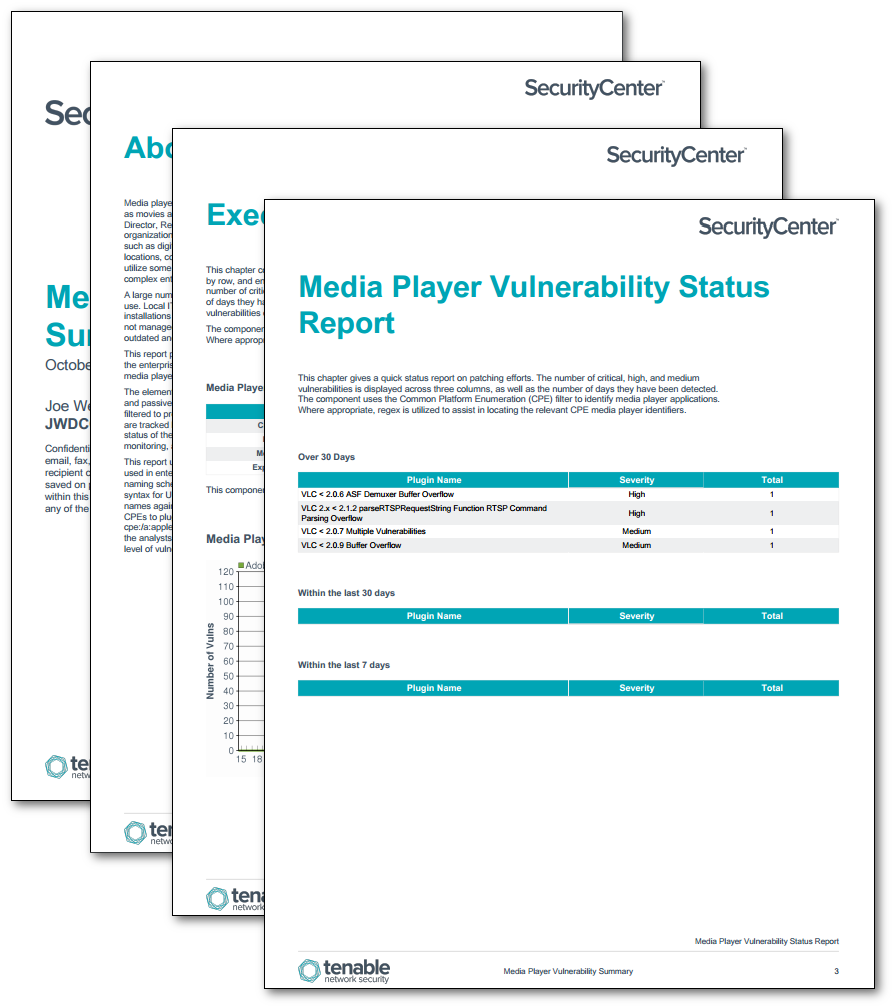
- Executive Summary – This chapter contains elements that present a visual overview of various defined technologies by row, and enumerates any found vulnerabilities across the columns. Included elements present the number of critical, high, and medium vulnerabilities, displayed across three columns, as well as the number of days they have been detected. The Media Players Trend chart presents a trend of detected media player vulnerabilities over the last 90 days.
- Media Player Vulnerability Status Report – This chapter gives a quick status report on patching efforts. The number of critical, high, and medium vulnerabilities is displayed across three columns, as well as the number of days they have been detected.
- Media Player Critical Vulnerability Information – The Media Player Critical Vulnerability Information chapter displays the most critical vulnerabilities in a text format for a fast, readable reference without having to do a deep dive.
- Media Player Detailed Vulnerability Summary –This chapter reports the number of systems on which media player applications have been identified in terms of critical, high, and medium vulnerabilities. The tables display the total number of identified vulnerabilities, including the associated repository, DNS, NetBIOS, MAC address, and IP address of the vulnerable systems for each network services vendor. Each element in this chapter provides detailed information about media player vulnerabilities that could impact critical systems and services within the organization.