by Megan Daudelin
March 15, 2017
Monitoring for intrusions is one of the many challenges that organizations face. Security teams are tasked with preventing, detecting, and stopping intrusions. Left alone, intruders can cause major damage to an organization through data theft and system compromise. Tenable SecurityCenter Continuous View (CV) is able to leverage log data processed by the Tenable Log Correlation Engine (LCE) in order to provide detailed insight into intrusion activity on the network.
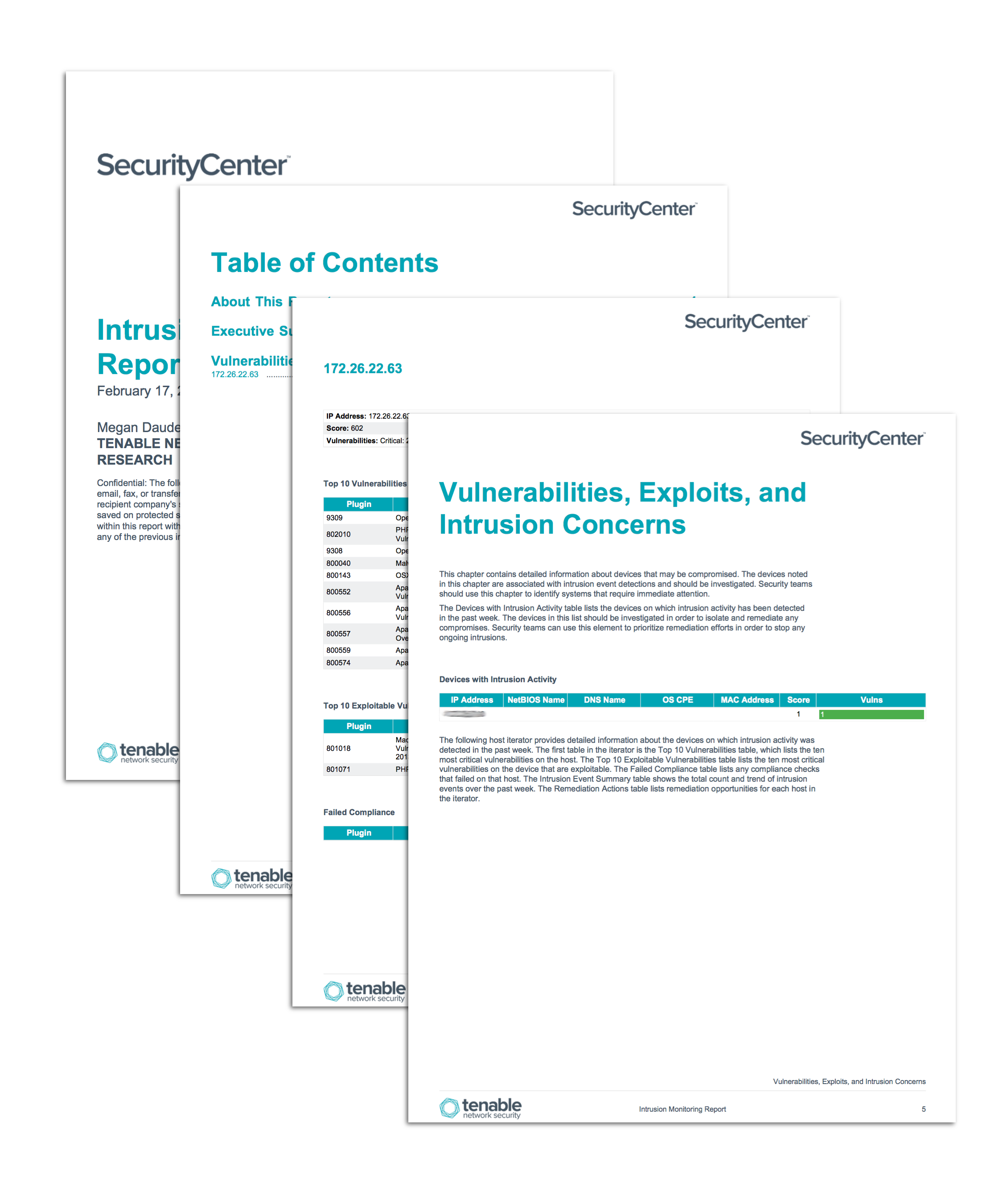
The Intrusion Monitoring report details events indicative of intrusions on the network and vulnerabilities that may leave the network exposed to intrusion. Intrusion events are monitored over time by LCE for unexpected spikes. Vulnerabilities are tracked by severity and exploitability in order to help security teams prioritize remediation efforts to reduce the risk of intrusion. By monitoring the network specifically for activity related to intrusion exposure, security teams can more effectively prevent and detect intrusions on their network.
The chapters in this report leverage data gathered by active vulnerability scanning with Tenable Nessus and passive vulnerability detection with the Tenable Passive Vulnerability Scanner (PVS). Aggregated and correlated logs from LCE are also analyzed by elements in this report. The data collected is filtered to provide insight into the vulnerabilities, hosts, and events specifically related to intrusion exposure or activity. Security teams can use all of the information in this report to assist in identifying hosts vulnerable to intrusion, in order to more effectively prevent and detect intrusion activity.
This report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the SecurityCenter Feed under the category Monitoring. The report requirements are:
- SecurityCenter 5.4.3
- LCE 5.0.0
- Nessus 6.10.1
- PVS 5.2.0
Tenable SecurityCenter Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist in securing an organization’s internal network and effectively responding to intrusions and attacks. SecurityCenter CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to determine vulnerabilities and compliance concerns. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Host data and data from other security products is analyzed to monitor the network for malware, intrusions, and other forms of malicious activity. SecurityCenter CV provides an organization with the most comprehensive view of the network and the intelligence needed to support proactive intrusion prevention efforts.
The following chapters are included in this report:
- Executive Summary: This chapter contains a high-level overview of information relevant to monitoring the network for intrusion activity.
- Vulnerabilities, Exploits, and Intrusion Concerns: This chapter contains detailed information about devices that may be compromised.