by Cody Dumont
November 10, 2016
In today’s ever-evolving technology market, companies are merging and gaining the benefits of acquisition, but also taking on new risks as a result. In April 2016, Dell and EMC announced their merger, which combined several well-known companies. As Dell and EMC change their corporate business models and processes to work in the new environment as Dell Technologies, organizations should ask the question, “how does this merger impact risk to our organization?” The Dell Technologies report uses CPE filters to identify vulnerabilities related to software and hardware made by Dell Technologies.
The products from Dell Technologies are often found in enterprise environments. Dell Technologies provides products and services that cover technologies such as desktops and servers, cloud-based application services, virtualization, and many other valuable services. However, with each of these products, there are new vulnerabilities still being found and detected with Tenable Nessus. Organizations with these products need an easy and efficient way to monitor vulnerabilities from Dell Technologies.
The report uses the Common Platform Enumeration (CPE) filter to identify software and hardware distributed by specific vendors. According to NIST, the CPE is a structured naming scheme for information technology systems, software, and packages. Based upon the generic syntax for Uniform Resource Identifiers (URI), CPE includes a formal name format, a method for checking names against a system, and a description format for binding text and tests to a name. Tenable assigns CPEs to plugins where appropriate. This allowing for analysts to search for common CPE prefixes such as “cpe:/o:dell:idrac6_firmware,” “ cpe:/h:sonicwall,” “cpe:/h:rsa:secured,” and “cpe:/a:emc:networker”. Associating CPE strings with vulnerabilities allows the analysts a greater view into separating operating system vulnerabilities from application vulnerabilities, and adds to the level of a vulnerability detail provided to the organization.
- Dell is a manufacturer of computer and server hardware. Dell has many other products related to information technology and is known to be a well-recognized company the marketplace.
- Dell EMC is best known for data storage, analytics, cloud computing, and other products and services that enable businesses to store, manage, protect, and analyze data.
- Pivotal is known for its cloud development platforms and methodologies.
- Quest Intrust enables organizations to collect, store, search and analyze massive amounts of IT data from numerous data sources, systems and devices.
- RSA is an information security company known for SecurID two-factor authentication, Archer GRC, and many other security products.
- Sonicwall is known for their firewall appliance and other security related products.
- VMWare is known for server virtualization and supporting technologies.
- SecurityCenter 5.3.0
- Nessus 6.8.1
Tenable SecurityCenter provides extensive network monitoring by leveraging a unique combination of detection, reporting, and pattern recognition utilizing industry recognized algorithms and models. SecurityCenter is continuously updated to detect advanced threats and vulnerabilities. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context and enabling decisive action that transforms the security program from reactive to proactive. Continuous vulnerability analysis enables security teams to more effectively tailor remediation efforts. Monitoring the network to ensure that all systems are secured against vulnerabilities is essential to ongoing security efforts. Tenable’s extensive network monitoring capabilities can verify that systems are successfully scanned regularly and secured against vulnerabilities, enabling ongoing improvements to an organization’s security posture.
Chapters
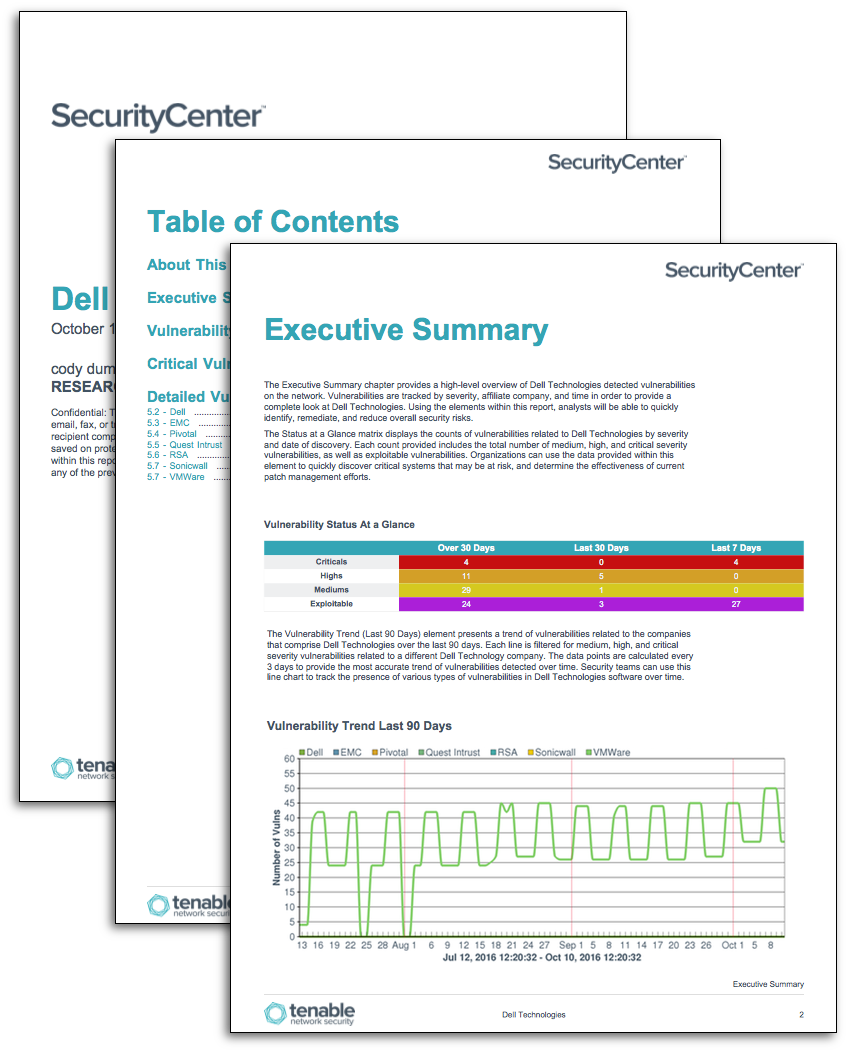
Executive Summary: The Executive Summary chapter provides a high-level overview of Dell Technologies products detected on the network. Vulnerabilities are tracked by severity, affiliate company, and time in order to provide a complete look at Dell Technologies. Using the elements within this report, analysts will be able to quickly identify, remediate, and reduce overall security risks.
Vulnerability Status at a Glance: The Vulnerability Status at a Glance chapter provides insight into Dell Technologies vulnerabilities detected within the network. Each table included within this chapter provides lists of the vulnerabilities detected in the past 7 and 30 days. Each table presents the latest information on relevant vulnerabilities, including plugin, name, family, severity, and total count of vulnerabilities detected. Data presented within this chapter can be modified to include additional host information, and additional details on the detected vulnerability.
Critical Vulnerability Information: The Criticals at a Glance chapter includes a list of the top critical Dell Technologies vulnerabilities detected in the environment. Vulnerabilities with a critical severity level are presented and filtered using Dell-based CPE strings, which will highlight vulnerabilities that present the highest level of risk to the organization. Each table is sorted by severity, and includes the plugin name and total number of hosts affected. Using elements within this chapter, security teams can use this element to identify and remediate the highest risk vulnerabilities.
Detailed Vulnerability Summary: The Detailed Vulnerability Summary chapter provides detailed information about Dell Technologies vulnerabilities detected in the environment. Vulnerabilities are separated by category and filtered using Dell-based CPE strings, which will provide comprehensive view of the vulnerabilities impacting the network. Each element in this chapter provides detailed information about the vulnerabilities that could impact critical systems and services within the organization.