by Cesar Navas
June 10, 2016
The Payment Card Industry Security Standards Council (PCI SSC) maintains, evolves, and promotes Payment Card Industry standards for the safety of cardholder data across the globe. The PCI SSC provides technical and operational requirements for organizations accepting or processing payment transactions. The guidance also applies to software developers and manufacturers of applications and devices used in those transactions.
The Payment Card Industry Data Security Standard (PCI DSS) helps entities understand and implement standards for security policies, technologies, and ongoing processes that protect payment systems from breaches and theft of cardholder data. The standards have historically been revised on a 2-3 year cycle, but the PCI SSC is transitioning to a posture of revising the PCI DSS as required based on changes to the current threat landscape. The current standard revision is PCI DSS Version 3.2, released in April 2016. Any organization that handles payment card information must adhere to the PCI DSS and must demonstrate compliance annually. Tenable's Tenable.sc Continuous View (CV) is able to help organizations monitor ongoing PCI DSS compliance by integrating with Tenable Nessus, Tenable Nessus Network Monitor (NNM), and Tenable Log Correlation Engine (LCE).
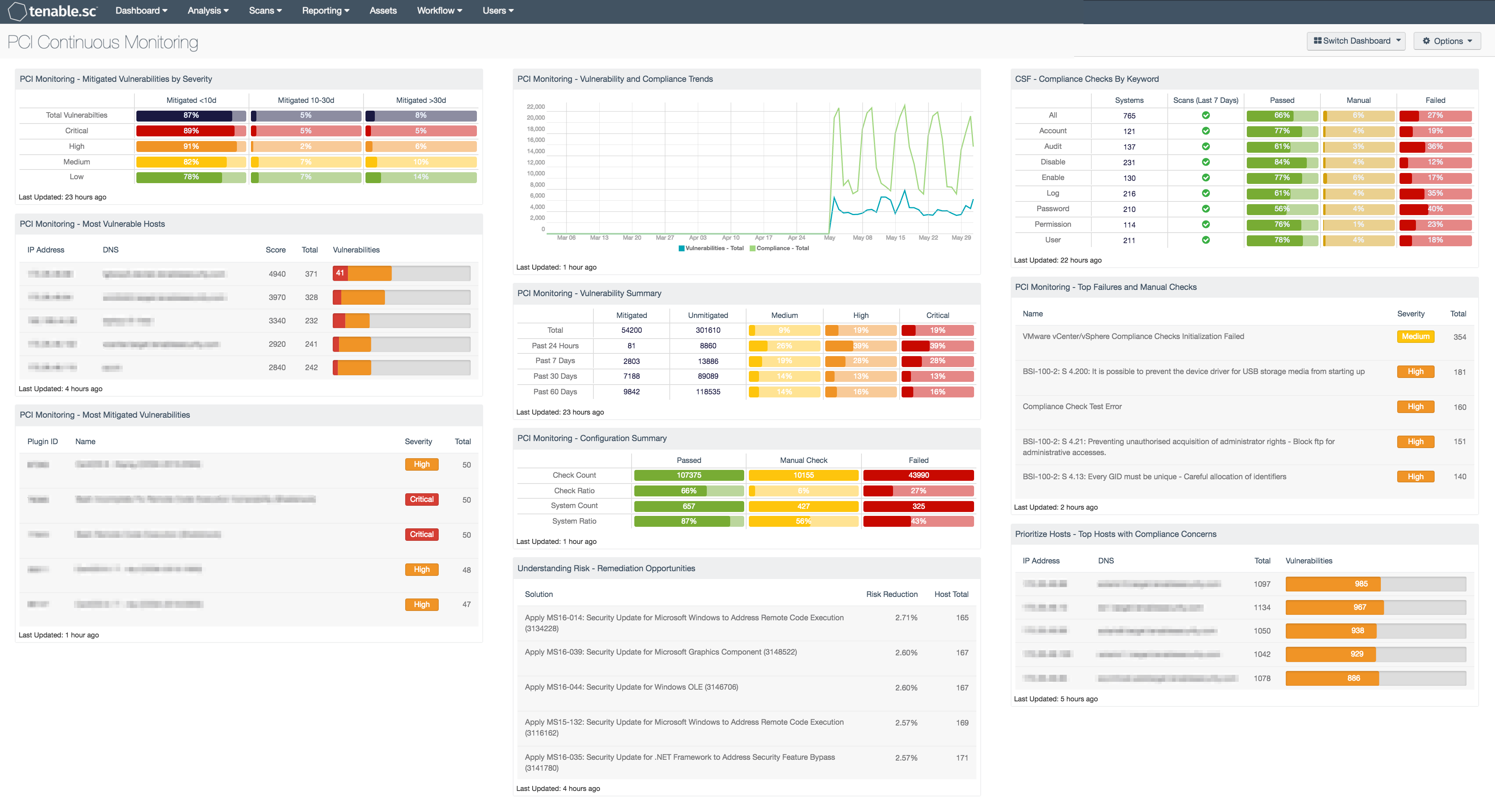
The PCI Continuous Monitoring dashboard presents extensive data about the vulnerability and configuration status of the network based on the available data. The dashboard can be used to gain insight into all vulnerability and configuration results, or it can be modified to focus exclusively on the results related to the cardholder data environment (CDE). Organizations can configure repositories or asset lists in order to tailor the focus of the dashboard. When the dashboard is added from the Tenable.sc Feed, the appropriate assets, IP addresses, or repositories can be specified. Assigning one of the options to the dashboard will update all filters in the components. Security teams can use this dashboard to identify and monitor vulnerability remediation and configuration adjustments across the organization.
Vulnerability-related components in this dashboard are filtered for high and critical severity vulnerabilities in order to focus on vulnerabilities of particular concern to PCI internal network scans. Identified vulnerabilities are tracked by time, severity, and host in order to provide multiple perspectives into the vulnerability status of the organization. By adding asset lists or repository filters, organizations can tailor the dashboard to only use data specifically related to internal vulnerability scanning requirements (PCI DSS 11.2.1). Different views of the vulnerability data provide a comprehensive view of the vulnerability status of the CDE or organization.
Components within this dashboard also focus on configuration data gathered from all available configuration scan results. The components are filtered for failed and manual configuration checks based on severity in order to identify checks specifically related to ongoing PCI security requirements. Failed configuration checks are identified as high severity, and checks requiring manual verification are identified as medium severity. Identifying and remediating failed configuration checks are especially important to ensuring ongoing adherence with PCI DSS. Configuration checks are tracked by time, severity, and host in order to provide a thorough perspective on the configuration status of the network.
Organizations can assess their level of adherence with PCI requirements focusing on continuous monitoring. The components in this dashboard are focused on PCI requirements 1, 2, 5 through 8, 10, and 11. The components in this dashboard cover sub-requirements such as 1.1, 1.4, 2.1, 2.2, 5.1, 5.2, 5.3, 6.1, 6.2, 7.2, 8.1, 10.2, 10.3, 11.2, and 11.3.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
- Tenable.sc 5.3.1
- Nessus 8.5.1
Tenable's Tenable.sc Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. Tenable.sc is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. Tenable Nessus Network Monitor (NNM) performs deep packet inspection to enable discovery and assessment of operating systems, network devices, hypervisors, databases, tablets, phones, web servers, cloud applications, and critical infrastructure. Tenable Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with Nessus, NNM, and LCE, Tenable.sc CV’s continuous network monitoring is able to detect systems and vulnerabilities across the enterprise.
This dashboard contains the following components:
- PCI Monitoring - Mitigated Vulnerabilities By Severity: The “PCI Monitoring - Mitigated Vulnerabilities by Severity” matrix component displays a concise overview of vulnerabilities and when the vulnerabilities were mitigated
- PCI Monitoring - Most Vulnerable Hosts: The “PCI Monitoring - Most Vulnerable Hosts” table lists the top 25 most vulnerable hosts by score
- PCI Monitoring - Most Mitigated Vulnerabilities: The “PCI Monitoring - Most Mitigated Vulnerabilities” table component lists the top 25 vulnerabilities that are in the “Mitigated” data source
- PCI Monitoring - Vulnerability and Configuration Trends: The “PCI Monitoring - Vulnerability and Configuration Trends” trend component displays the trend of vulnerabilities and configuration checks over the last 3 months
- PCI Monitoring - Vulnerability Summary: The “PCI Monitoring - Vulnerability Summary” matrix component displays an overview of vulnerabilities over time
- PCI Monitoring - Configuration Summary: The “PCI Monitoring - Configuration Summary” matrix displays the counts and ratios of passed, failed, and manual configuration checks
- Understanding Risk - Remediation Opportunities: This table displays the top remediations for the network
- CSF - Compliance Checks By Keyword: This component uses results from the compliance audit to trigger on specific plugin keywords
- PCI Monitoring - Top Failures and Manual Checks: The “PCI Monitoring - Top Failures and Manual Checks” table lists the configuration checks that failed or require manual verification on the greatest number of hosts
- Prioritize Hosts - Top Hosts with Compliance Concerns: This table displays the top hosts on the network that have either compliance failures or compliance checks that must be performed manually