by Cody Dumont
April 18, 2016
Governance, Risk Management, and Compliance (GRC) is a substantial part of any information assurance program. GRC requires information systems to be audited, regardless of the standard to which the audit is performed. This dashboard provides audit results for Oracle database systems.
One of the initial steps in a successful GRC program is to set configuration guidelines and establish a supportable set of security policies. Tenable.sc Continuous View (CV) can measure compliance using audit files that cover a wide range of major regulations and other auditable standards. Tenable provides over 500 audit files in the Tenable.sc feed and are available for download from the Tenable Support Portal, in categories such as operating systems, applications, databases, and network devices. Tenable products can be used to audit systems based on SCAP content, and many Tenable audit policies have been certified by the Center for Internet Security (CIS). More information about audit files can be found in the Tenable Discussion Forums, Tenable Support Portal, Nessus Compliance Checks, and Nessus Compliance Reference.
Tenable.sc Continuous View (CV) using Nessus has several built-in functions to perform the Oracle database compliance checks. Oracle database compliance checks can be conducted by executing commands from the command line, Application Program Interface (API), and several other methods. There are also built-in checks such as password length, permission management, and Suspicious File Content. Other more complex checks can use regular expressions and other pattern matching methods.
Audit files are easily created or modified to support an organization’s existing security policies. When an audit scan is performed, for each individual compliance check, Nessus attempts to determine if the host is compliant, non-compliant, or if the results are inconclusive and need to be verified manually. Unlike a vulnerability check that only reports if the vulnerability is actually present, a compliance check always reports a result. The data collected can be used as the basis of an audit report to show that a host passed or failed a specific test, or if configuration check could not be properly tested.
The dashboard and its components are available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessments. The dashboard requirements are:
- Tenable.sc 5.1.0
- Nessus 8.5.2
- Compliance Data
- This dashboard requires “Full Text Search” to be enabled for each analyzed repository.
Tenable.sc CV is the market leader in providing a unique combination of vulnerability detection, compliance auditing, and reporting. Tenable.sc CV supports auditing more technologies than any other vendor, including operating systems, network devices, hypervisors, databases, tablets, phones, web servers, and critical infrastructure. Nessus is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audits. This makes Tenable.sc CV the market-defining continuous network monitoring platform, and Nessus the market-defining vulnerability scanning for auditors and security analysts.
Components
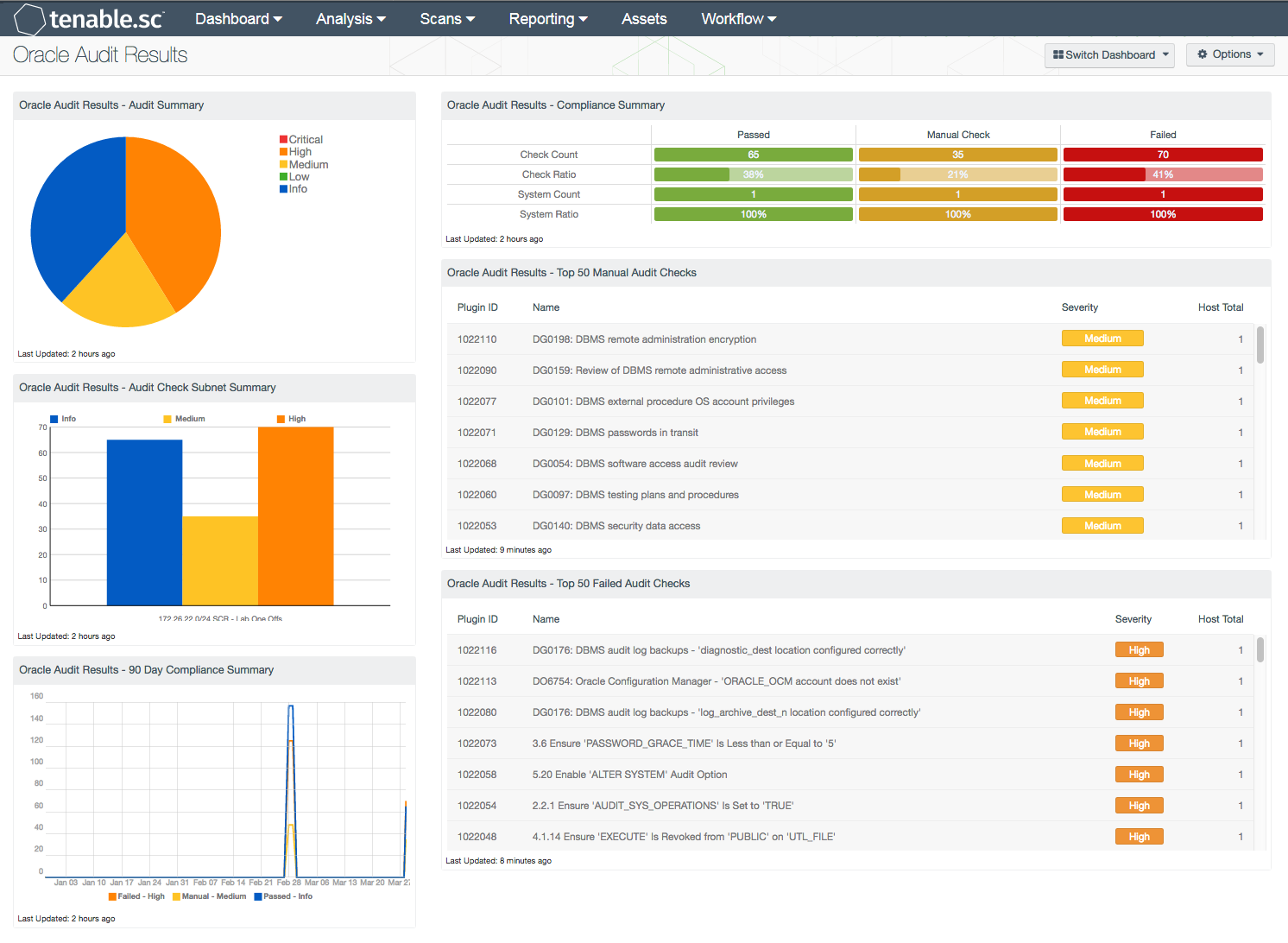
Oracle Audit Results - Audit Summary: The Oracle Audit Summary is a severity-based pie chart that helps to summarize the current compliance status. The chart provides a conceptual view of the compliance status. High severity denotes checks that have failed to meet the compliance threshold. Medium severity shows checks that need to be manually reviewed to assess their compliance state. Informational severity status is used for checks that have passed the compliance check.
Oracle Audit Results - Audit Check Subnet Summary: The Oracle Audit Check Subnet Summary chart provides a summary of the top 30 affected subnets. The columns are sorted using the failed compliance check (vulnerability) count column. The audit checks return one of three values: Info severity represents passed checks, High severity represents failed audit checks, and Medium severity represents checks that must be manually verified.
Oracle Audit Results - 90 Day Compliance Summary: The Oracle 90-Day Compliance Summary line chart provides analysts with a historic view of compliance status over the past 90 days.
Oracle Audit Results - Compliance Summary: When performing configuration audits of systems in accordance with a GRC program, security analysts can benefit from a summary view of the data set. The Oracle Compliance Summary matrix provides a high-level view of the Oracle compliance status.
Oracle Audit Results - Top 50 Failed Audit Checks: The Oracle Top 50 Failed Audit Host Details table is an informative table providing the audit checks that have failed compliance checks.
Oracle Audit Results - Top 50 Manual Audit Checks: The Oracle Top 50 Manual Audit Host Details table is an informative table providing the audit checks that need to be manually verified.