by Megan Daudelin
January 26, 2016
Monitoring a network for indications of abuse, compromise, and intrusion is a daunting task for any security team to tackle. Close monitoring of system log data can help reduce incident response time, but keeping pace with the rate of syslog generation can prove impossible. By leveraging the capabilities of the Log Correlation Engine (LCE), SecurityCenter is able to present concise data about indications of compromise.
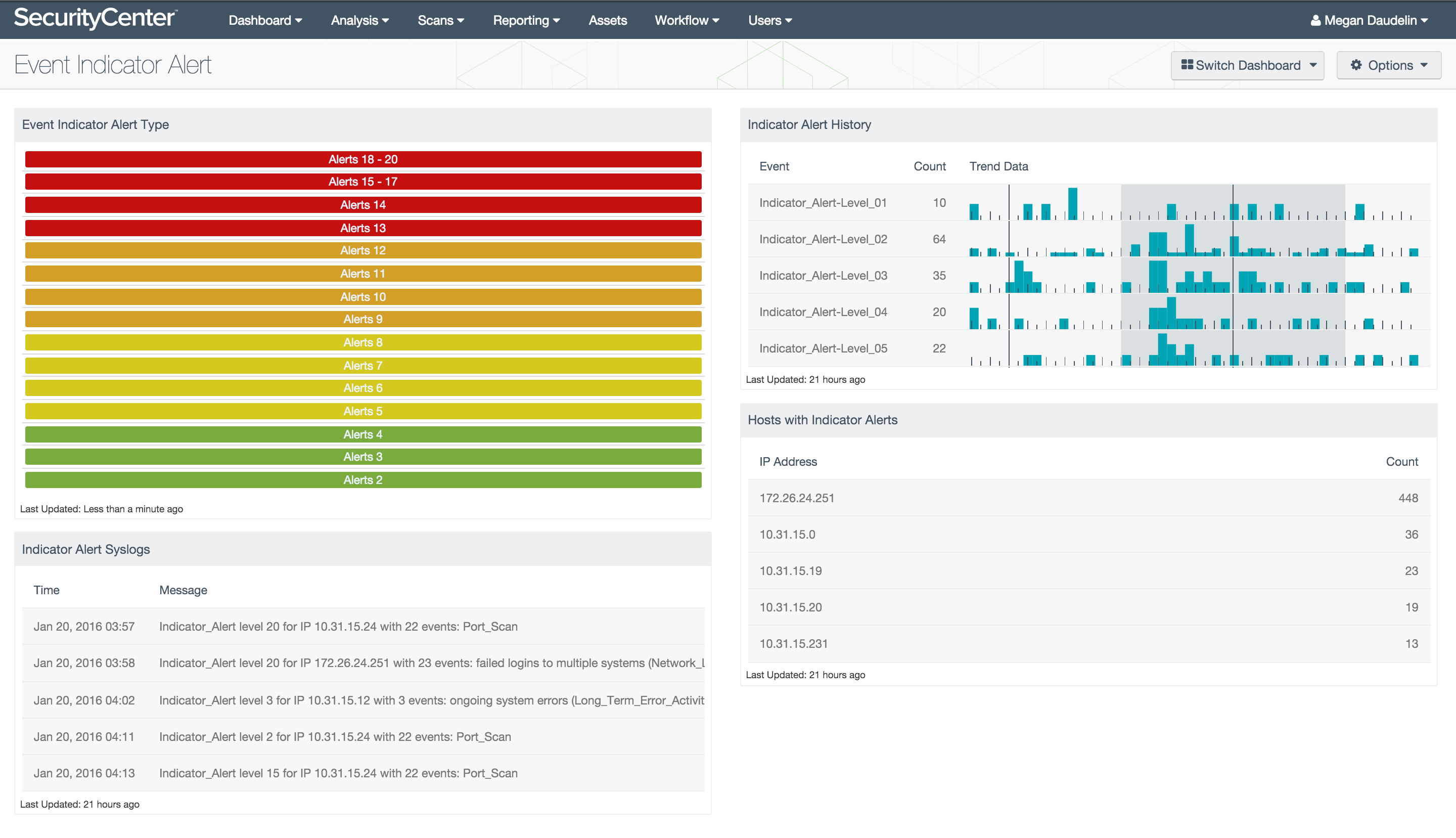
The Event Indicator Alert dashboard monitors events that could be indicative of compromise. The “indicator” normalized event type is used to identify events of potential concern. The event type “indicator” is used by LCE to note monitored events that are triggered multiple times during a 24-hour period. The alert level of the indicator event is raised each time the event is triggered, and the maximum level is 20. The “indicator” event type monitors and analyzes particular normalized events for chains of activity that could indicate potential abuse, compromise, or attack. This dashboard leverages the “indicator” event type to alert security teams to events of concern.
The components in this dashboard provide distinct views of potentially concerning events. A matrix of indicators provides a quick view of the indicator levels reached during the past 24 hours. The latest syslogs related to indicator events are listed to help analysts monitor relevant activity. Recent trend data is provided for each indicator alert level along with counts of events in the past 24 hours. Additionally, a list of hosts that have triggered indicator alerts is included to identify hosts that may be compromised. Together, the components in this dashboard enable security teams to monitor for potential indicators of compromise or abuse.
This dashboard and its components are available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. This dashboard can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The dashboard requirements are:
- SecurityCenter 4.8.2
- LCE 4.6.0
SecurityCenter Continuous View (CV) provides continuous network monitoring, vulnerability identification, risk reduction, and compliance monitoring. The Log Correlation Engine (LCE) performs deep log analysis and correlation to continuously discover and track systems, applications, cloud infrastructure, trust relationships, and vulnerabilities. By integrating with LCE, SecurityCenter CV’s continuous network monitoring is able to detect systems and vulnerabilities across the enterprise.
The following components are included in this dashboard:
- Event Indicator Alert Levels: The Event Indicator Alert Levels matrix shows whether indicator alerts of each level have been identified within the past 24 hours.
- Indicator Alert Syslogs: The Indicator Alert Syslogs table lists normalized syslog messages from the past 6 hours.
- Indicator Alert History: The Indicator Alert History table displays trend data for each indicator alert level.
- Hosts with Indicator Alerts: The Hosts with Indicator Alerts table lists the top 30 hosts with the highest counts of indicator alert events.