by Cesar Navas
October 11, 2016
As organizations continue to support workforce mobility, more will rely on using cloud, remote access solutions, and portable devices for accessing critical data both internally and externally. Although these solutions can help to enhance employee productivity, failing to monitor and apply appropriate security controls can result in devastating consequences for an organization. Malware can be introduced as employee-owned mobile and USB devices are connected to the network. Attacks against externally-accessible systems can be launched from the internet. Internal and external trust relationships can be exploited, allowing infiltration of supposedly secure subnets. These issues can be especially dangerous in Bring Your Own Device (BYOD) environments and within organizations that have large numbers of connections to third party networks. Without adequate control, network connectivity can be exploited, leading to the compromise of critical systems and sensitive data.
The French Network and Information Security Agency (Agence nationale de sécurité des systèmes d’information or ANSSI) developed the "40 Essential Measures for a Healthy Network" to assist organizations in safeguarding the security of information systems within a network. Following these measures, or rules, for a healthy network will provide basic protection for an organization's critical data. ANSSI states that the majority of IT attacks that have involved ANSSI stepping in could have been prevented had the IT measures set out in the guide been applied.
This dashboard aligns with Section II of the ANSSI 40 Essential Measures for a Healthy Network: Control the Network. This section contains two rules:
Rule 4 emphasizes the importance of limiting the number of internet access points and connections with other networks to only those that are necessary. Limiting access in this way will assist in monitoring and controlling traffic.
Rule 5 recommends prohibiting the connection of personal devices to the network. Personal devices such as tablets, smartphones, MP3 players, and USB sticks are controlled by their users and any organizational security measures will likely not be applied to them. Keeping these personal devices from connecting to the network will prevent malware or other malicious content on these devices from being transferred to the network.
Using this dashboard, an organization will be able to better monitor network connectivity, access control, and connections of mobile and removable devices. This information will assist the organization in better controlling connectivity to the network, in order to protect critical systems and data on the network from malware and potential attacks.
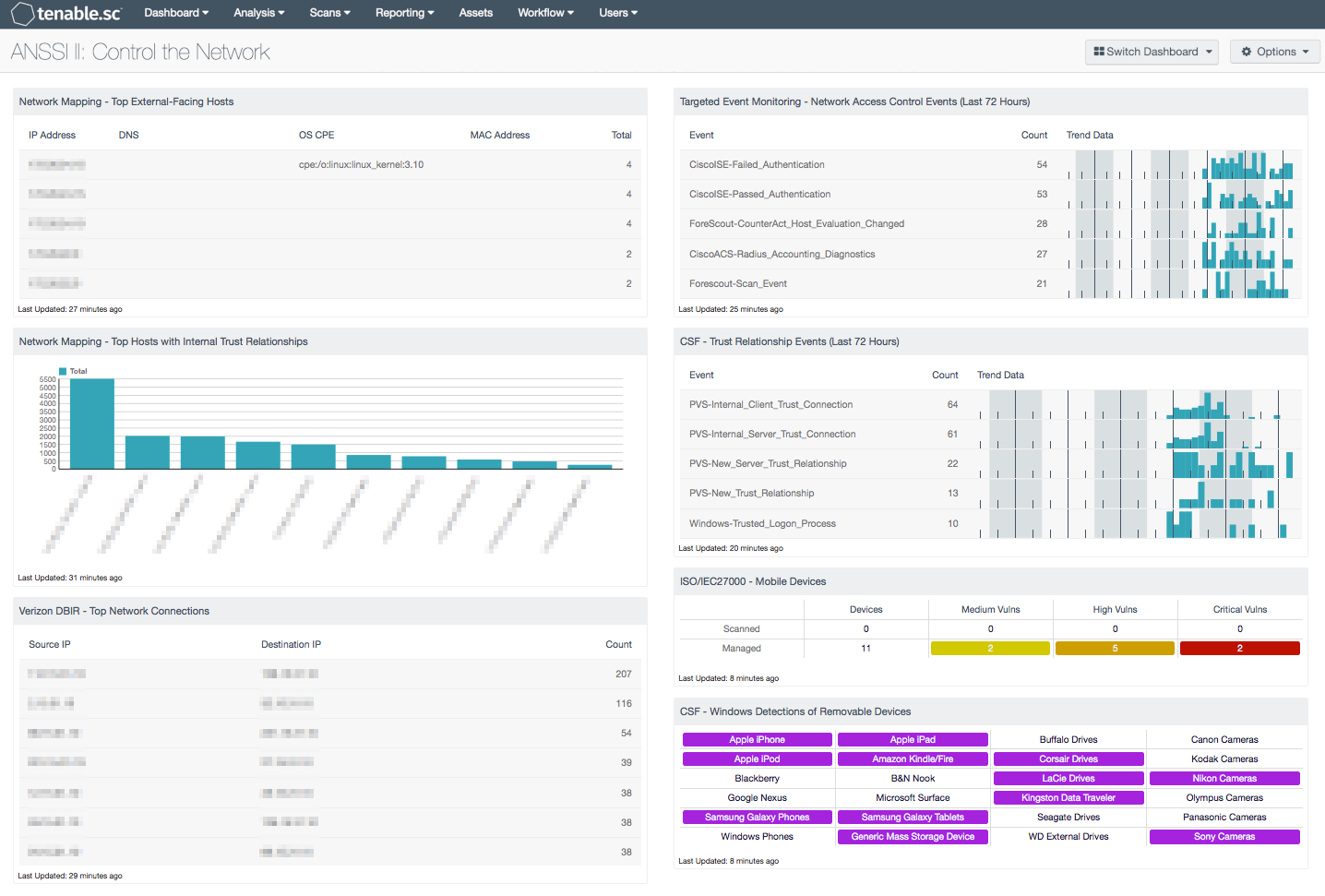
Several components on this dashboard highlight network system connectivity. The top systems that connect externally to systems outside the internal network are presented, as well as the top systems that connect internally to other systems. The top network connections by source and destination IP address are also displayed. Trust relationship events are presented, which can give information on trusted connections and modifications of trusted relationships. Network access control activity is noted, to assist in monitoring for unauthorized authentication attempts and device connectivity issues. In addition, detections of mobile and removable devices such as smartphones, tablets, external drives, and digital cameras are highlighted. Analysts can use this dashboard to easily drill down into the data presented and gain more detailed information.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.0
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.1
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist an organization in controlling access to the network. Active scanning periodically examines devices to determine vulnerabilities and compliance concerns. Passive listening collects data to continuously detect devices and monitor network connections and activity. Host data and data from other security investments is analyzed to monitor network access control and trust relationships. Tenable.sc CV provides an organization with the most comprehensive view of the network, and the intelligence needed to control network connectivity in order to safeguard critical assets and information.
This dashboard contains the following components:
- Network Mapping - Top External-Facing Hosts: This component identifies internal hosts participating in connections to systems outside of the internal network
- Network Mapping - Top Hosts with Internal Trust Relationships: This bar chart presents the top internal hosts with client-server trust relationships to other internal hosts
- Verizon DBIR - Top Network Connections: This component displays the top sessions collected using data collected using the Network Monitoring and Netflow collectors
- Targeted Event Monitoring - Network Access Control Events (Last 72 Hours): This component displays events collected by LCE in the last 72 hours from network access control solutions
- CSF - Trust Relationship Events (Last 72 Hours): The Trust Relationships Event component displays detected trust relationship event changes within the last 72 hours
- ISO/IEC27000 - Mobile Devices: This component presents both scanned and managed mobile devices on a network
- CSF - Windows Detections of Removable Devices: This component presents a matrix of Windows detections of removable storage devices