Tenable Nessus® Professional
Vulnerability Assessment to Stay One Step Ahead of Attackers
Overcome scarce resources and limited time to keep pace with attackers and proactively find and fix vulnerabilities across your constantly changing attack surface.
Trust the No. 1 vulnerability assessment solution to give you peace of mind in a constantly changing security world. Trust Tenable Nessus.
With Advanced Support for Nessus Pro, your teams will have access to phone, Community, and chat support 24 hours a day, 365 days a year. This advanced level of technical support helps to ensure faster response times and resolution to your questions and issues.
Advanced Support Plan Features
Phone Support
Phone support 24 hours a day, 365 days a year, available for up to ten (10) named support contacts.
Chat Support
Chat support available to named support contacts, accessible via the Tenable Community is available 24 hours a day, 365 days a year.
Tenable Community Support Portal
All named support contacts can open support cases within the Tenable Community. Users can also access the Knowledge Base, documentation, license information, technical support numbers, etc.; utilize live chat, ask questions to the Community, and learn about tips and tricks from other Community members.
Initial Response Time
P1-Critical: < 2 hr
P2-High: < 4 hr
P3-Medium: < 12 hr
P4-Informational:
< 24 hr
Support Contacts
Support contacts must be reasonably proficient in the use of information technology, the software they have purchased from Tenable, and familiar with the customer resources that are monitored by means of the software. Support contacts must speak English and conduct support requests in English. Support contacts must provide information reasonably requested by Tenable for the purpose of reproducing any Error or otherwise resolving a support request.
Knowledge is power
Eliminate attack paths by gaining the insights you need.
Keeping pace with attackers is hard – especially with the constant barrage of new vulnerabilities and an ever-changing attack surface.
Since 1998, Nessus has helped security teams stay a step ahead. It provides the visibility, accuracy and speed you need to protect your organization against unacceptable risk.

"The flexibility of the program and innovative Tenable technology allow us to build solutions that fit our customers' needs. It’s a key part of how we drive improvement with metrics-driven vulnerability management programs instead of limiting ourselves to one-time vulnerability scanning and assessment services."Jordan Mauriello, CTO of Tenable partner, Critical Start
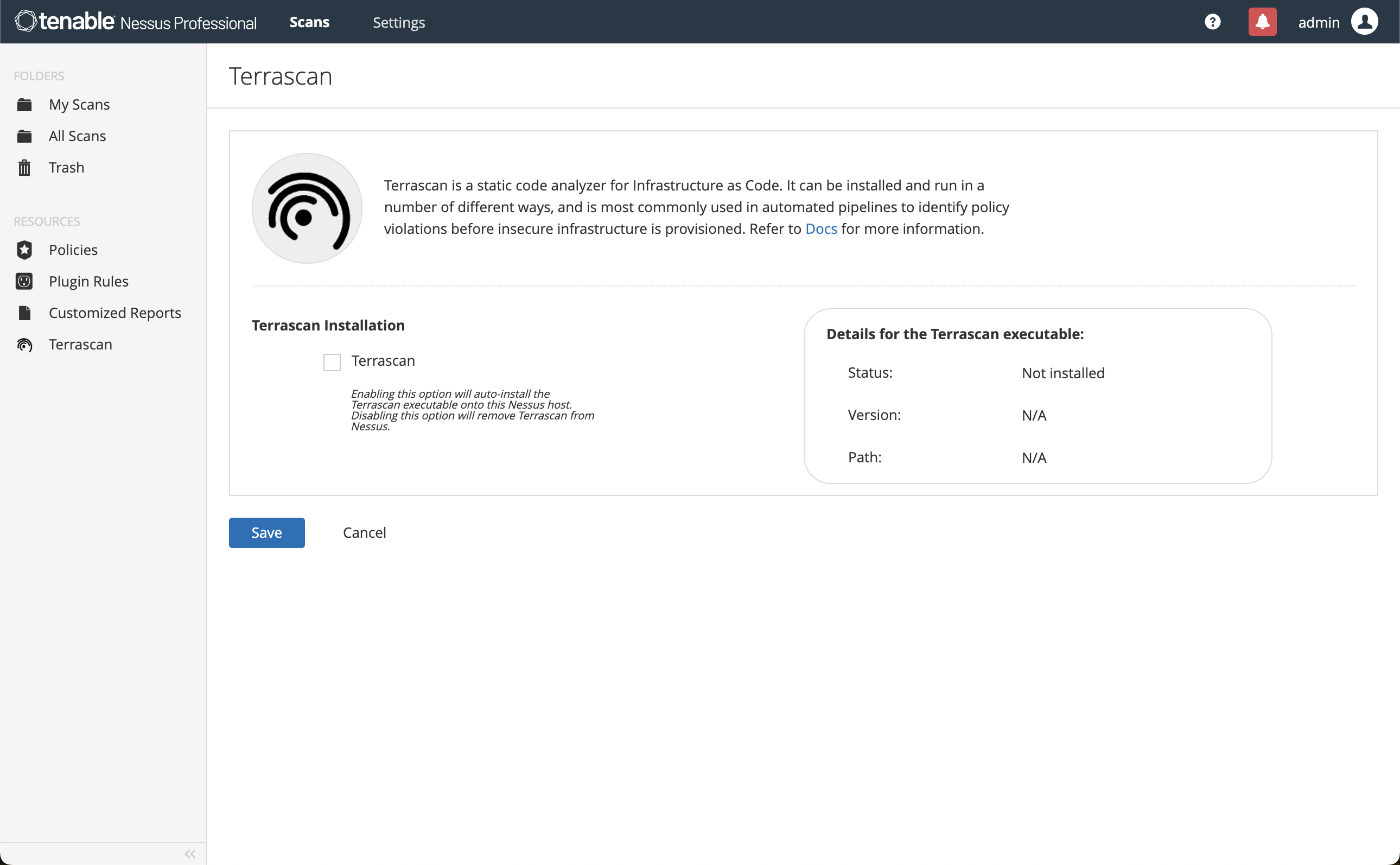
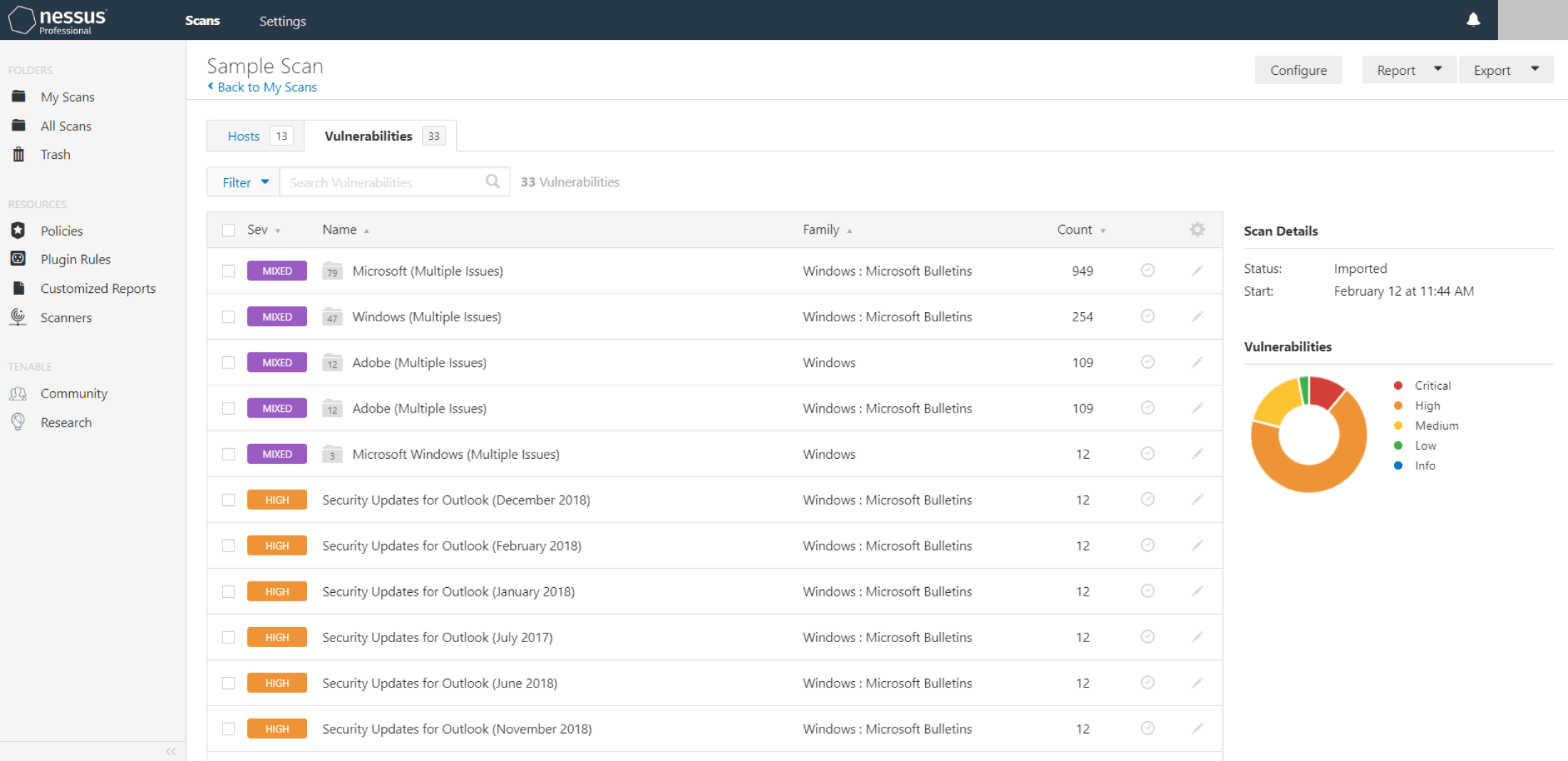
Built by Practitioners
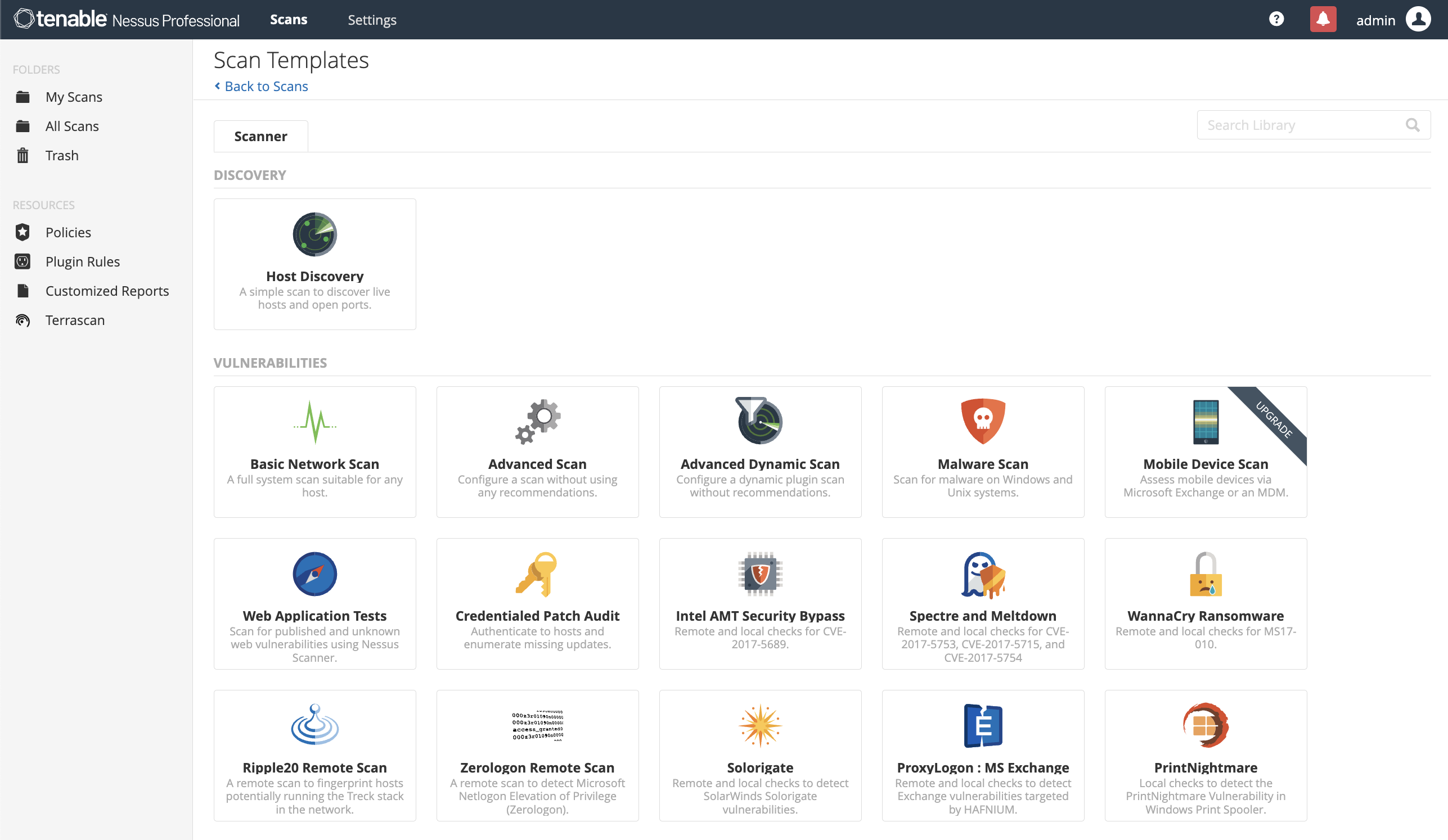
Nessus is built from the ground-up with a deep understanding of how security practitioners work. Every feature in Nessus is designed to make vulnerability assessment simple, easy and intuitive. The result: less time and effort to assess, prioritize and remediate issues. Learn more about the features here.
Nessus Pro Benefits

Easy-to-Deploy, Easy-to-Use
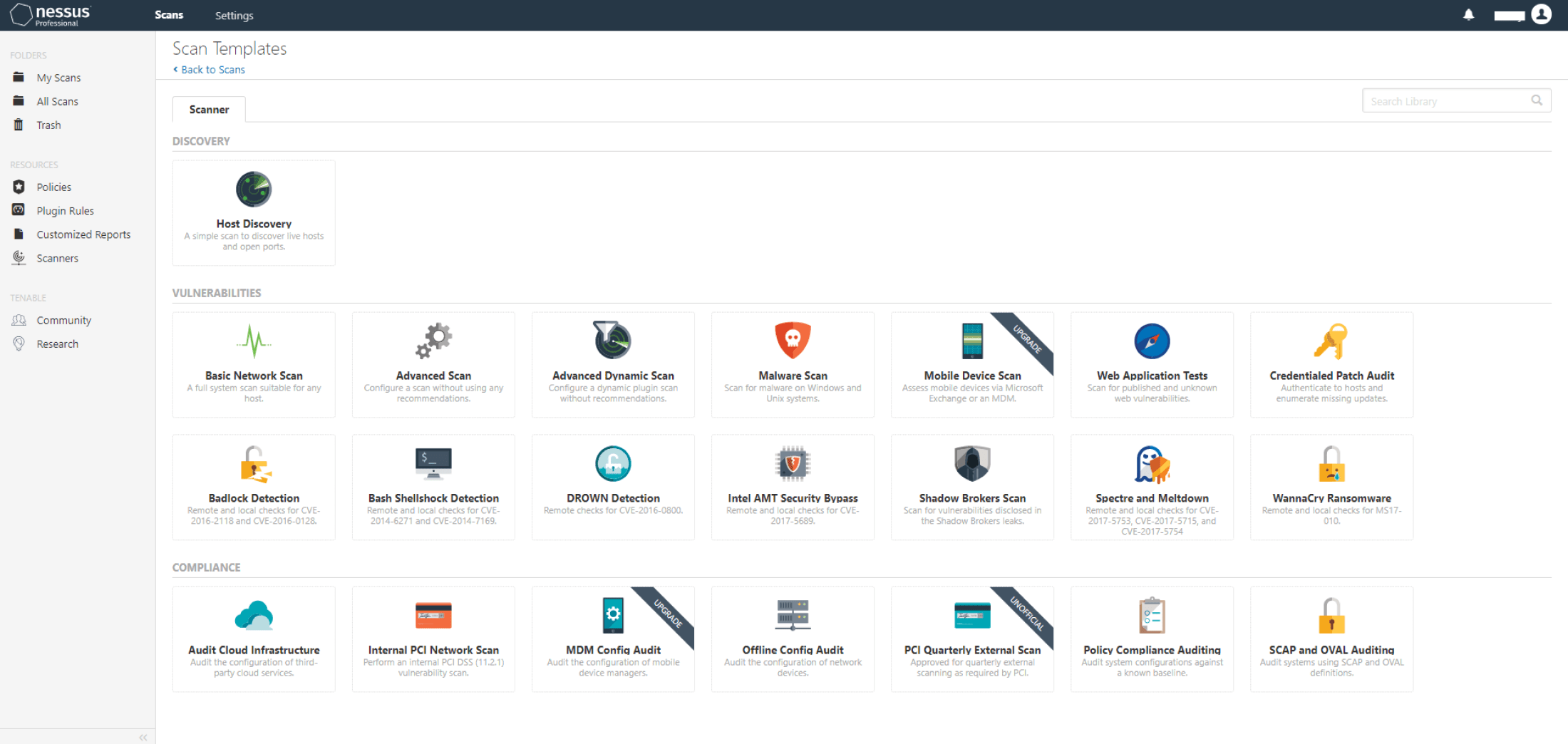
A fully portable vulnerability assessment solution that can be deployed virtually anywhere. Policy creation is simple and only requires a few clicks to scan an entire corporate network.

Advanced Detection Means More Protection
65K CVEs – the most in the industry. Nessus scans more technologies and uncovers more vulnerabilities than competing solutions.

Cost Effective for Companies of All Sizes
Cost effective for any consultant or team, Nessus provides complete vulnerability scanning with unlimited assessments for one low price.

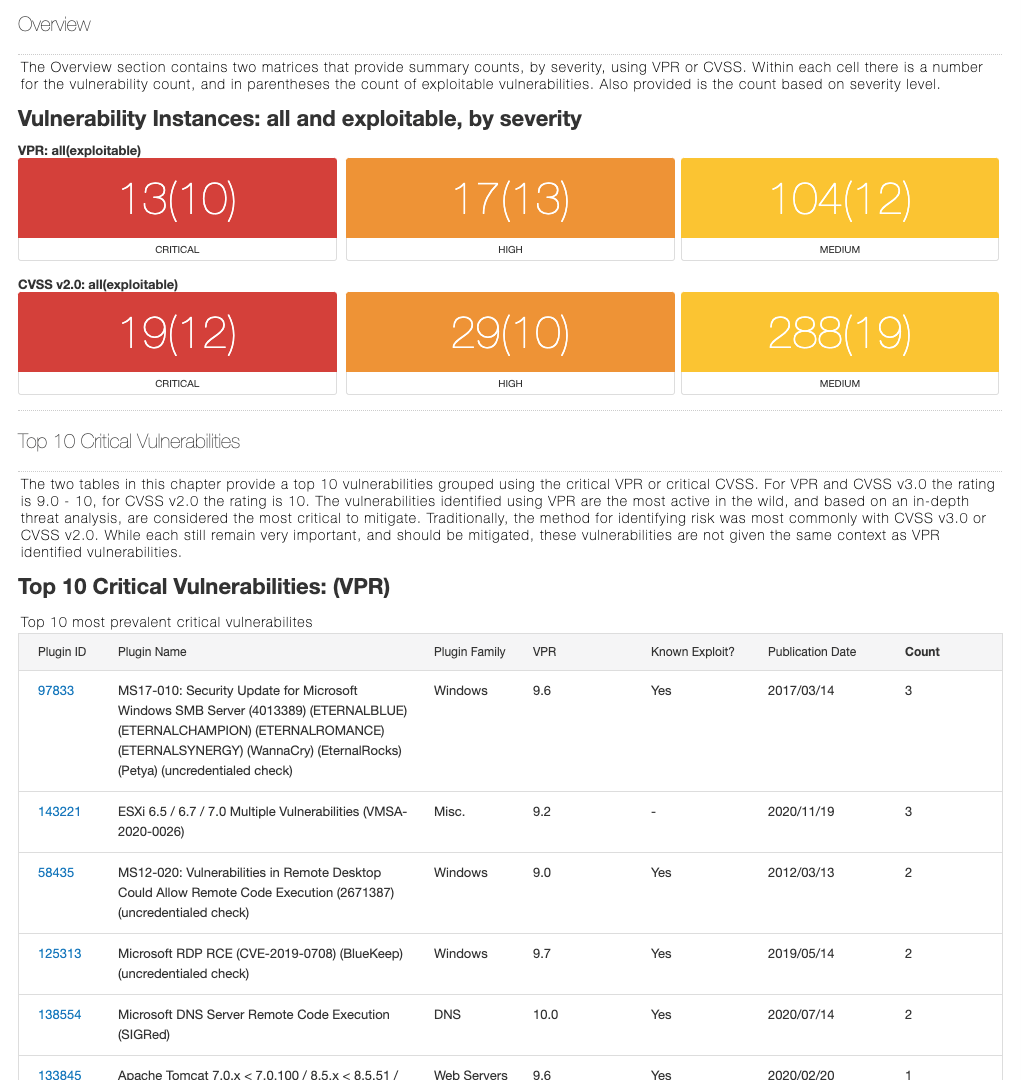
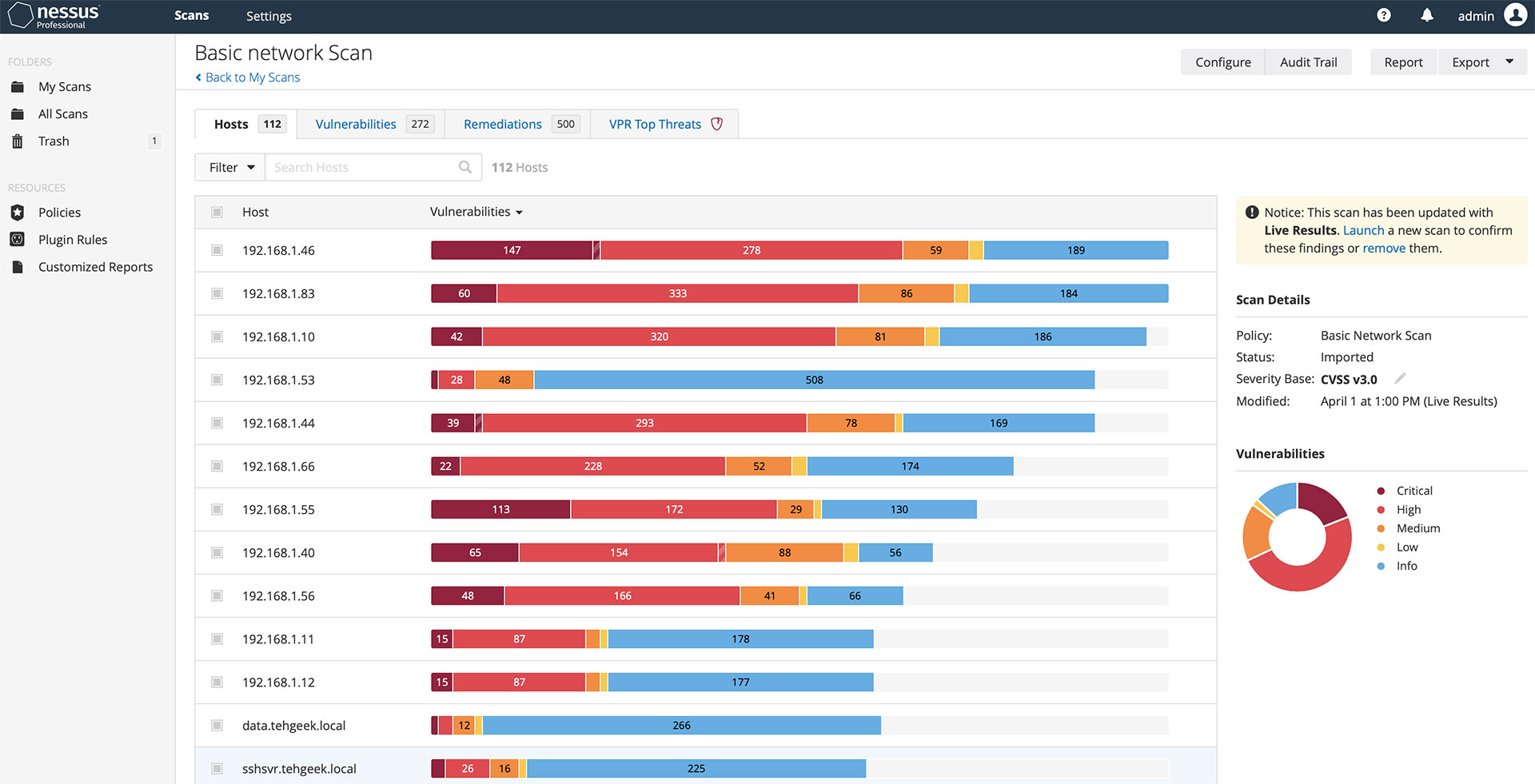
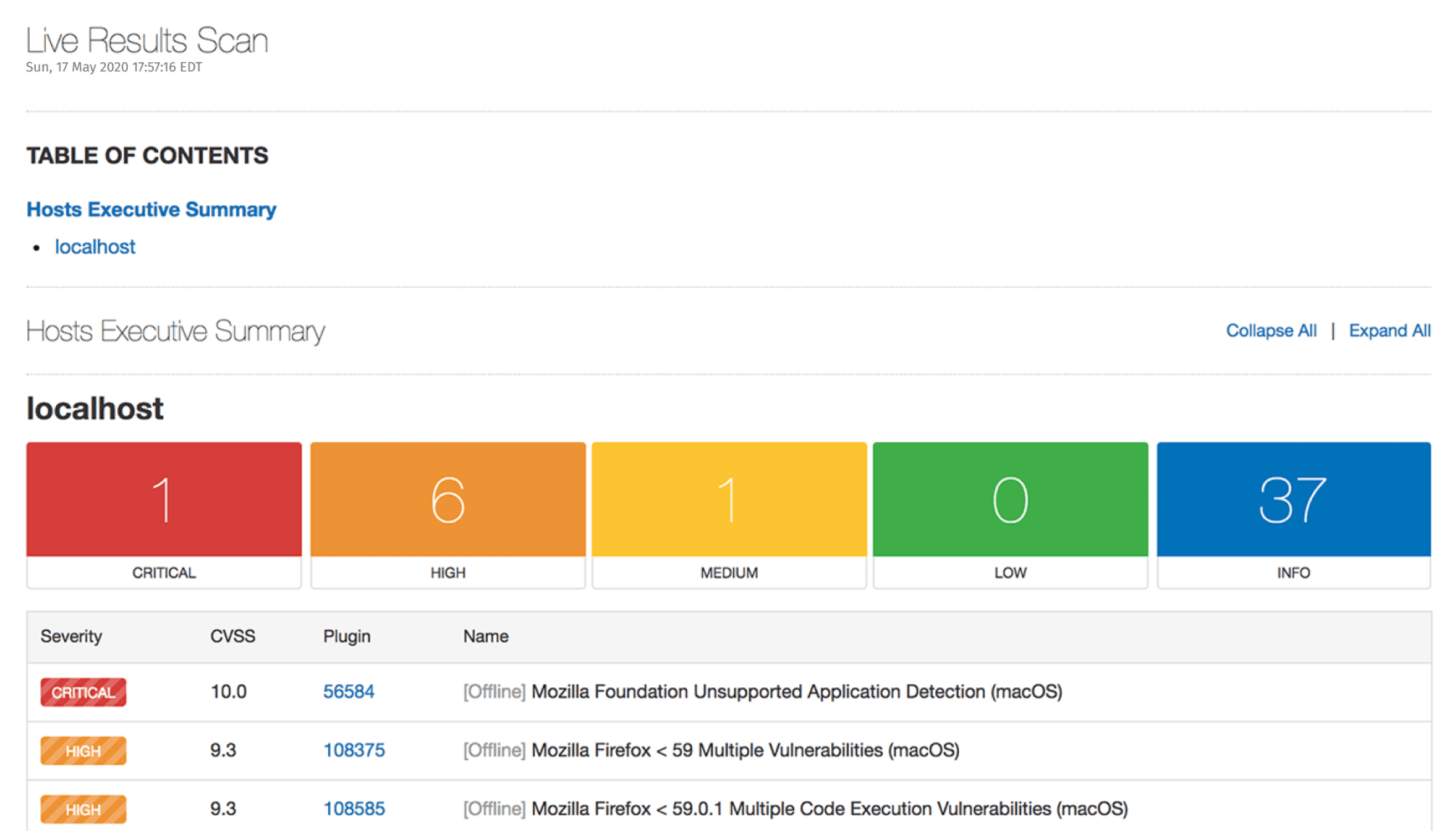
Accurate Visibility Into Your Networks
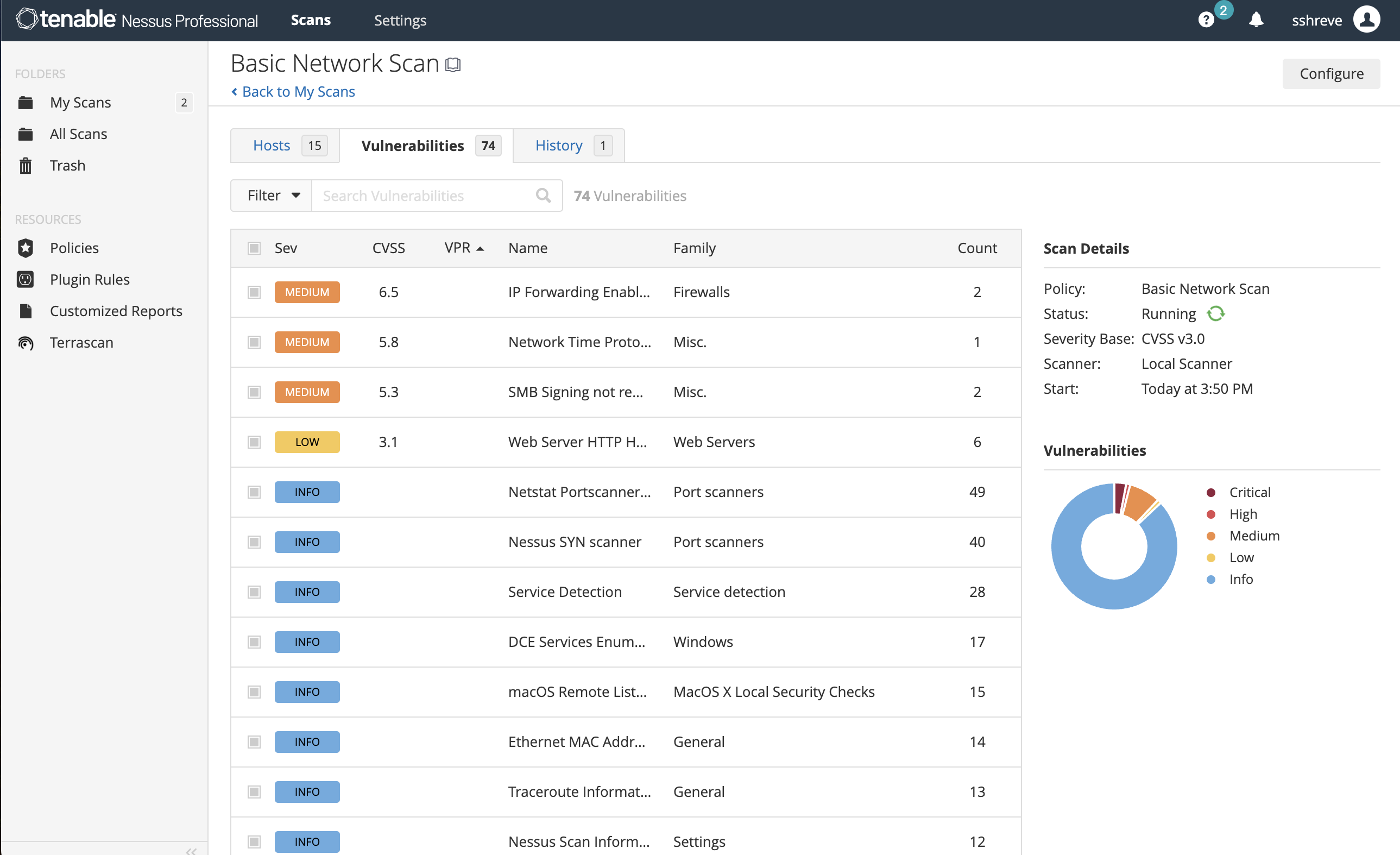
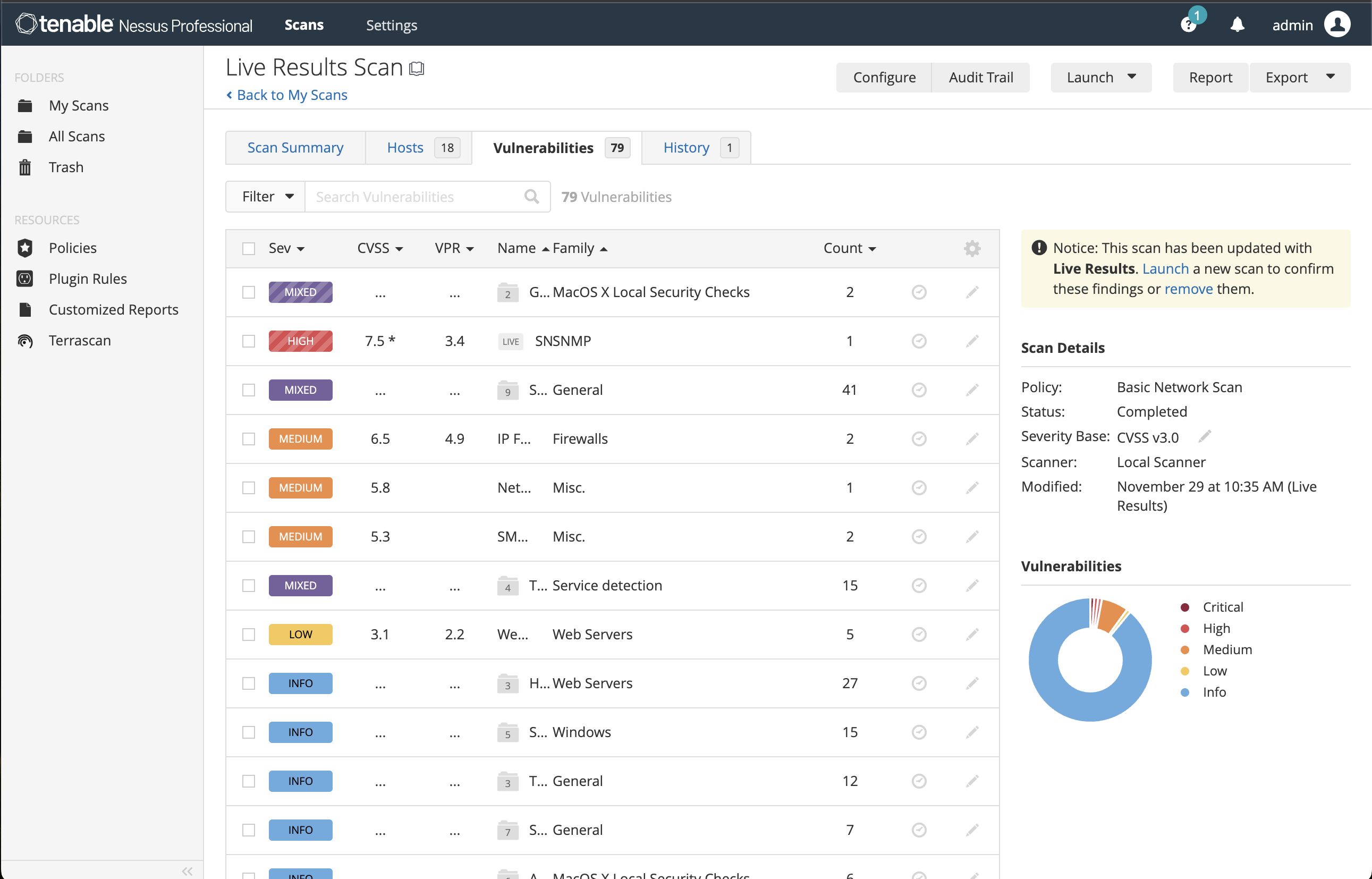
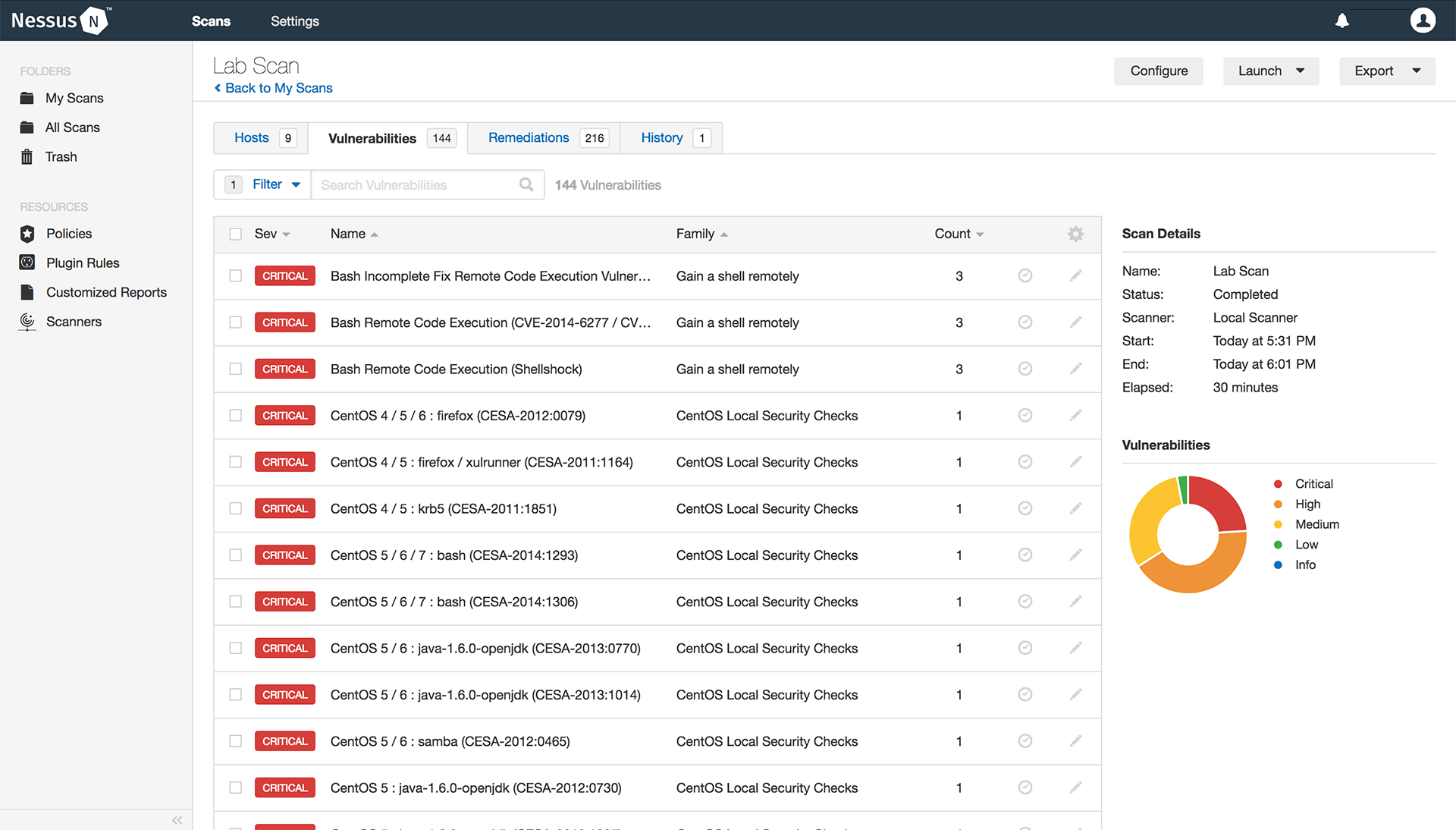
Nessus identifies the vulnerabilities that need attention with high-speed, accurate scanning, and highlights which vulnerabilities should be addressed first.

The Power of the Tenable Zero Day Research Team
Tenable researchers leverage extensive intel sources. Find and provide protection from the latest threats via new plugins.

The Power of Tenable Grows With You
With operability across Tenable’s product portfolio, easily migrate to Tenable Vulnerability Management, leverage the additional insights of Tenable OT Security for your industrial environment, or combine with the rest of Tenable the solutions as your vulnerability management needs increase.
KEY USE CASES FOR NESSUS
Nessus is the world’s No. 1 vulnerability scanning solution. Learn more about its power by exploring how Tenable customers put it to work in a variety of critical situations.
Pen Tester Cybersecurity Education Programs Faculty and Students Consultant SMB
Security Admin

Network penetration testers play a unique role in the IT security ecosystem.
Before executing full-fledged breach simulations that unveil how attackers can exploit specific weaknesses, pen testers often use Nessus first to identify exactly where those major vulnerabilities are hiding.
Read More
Students in cybersecurity education programs are invaluable to this highly specialized field.
Professors leading vulnerability assessment or vulnerability management courses use Nessus as a foundational tool. Its remarkable ease of use helps students quickly get acclimated to the essentials of uncovering vulnerabilities.
Read More
Cybersecurity consultants play pivotal roles in a constantly shifting threat and vulnerability landscape.
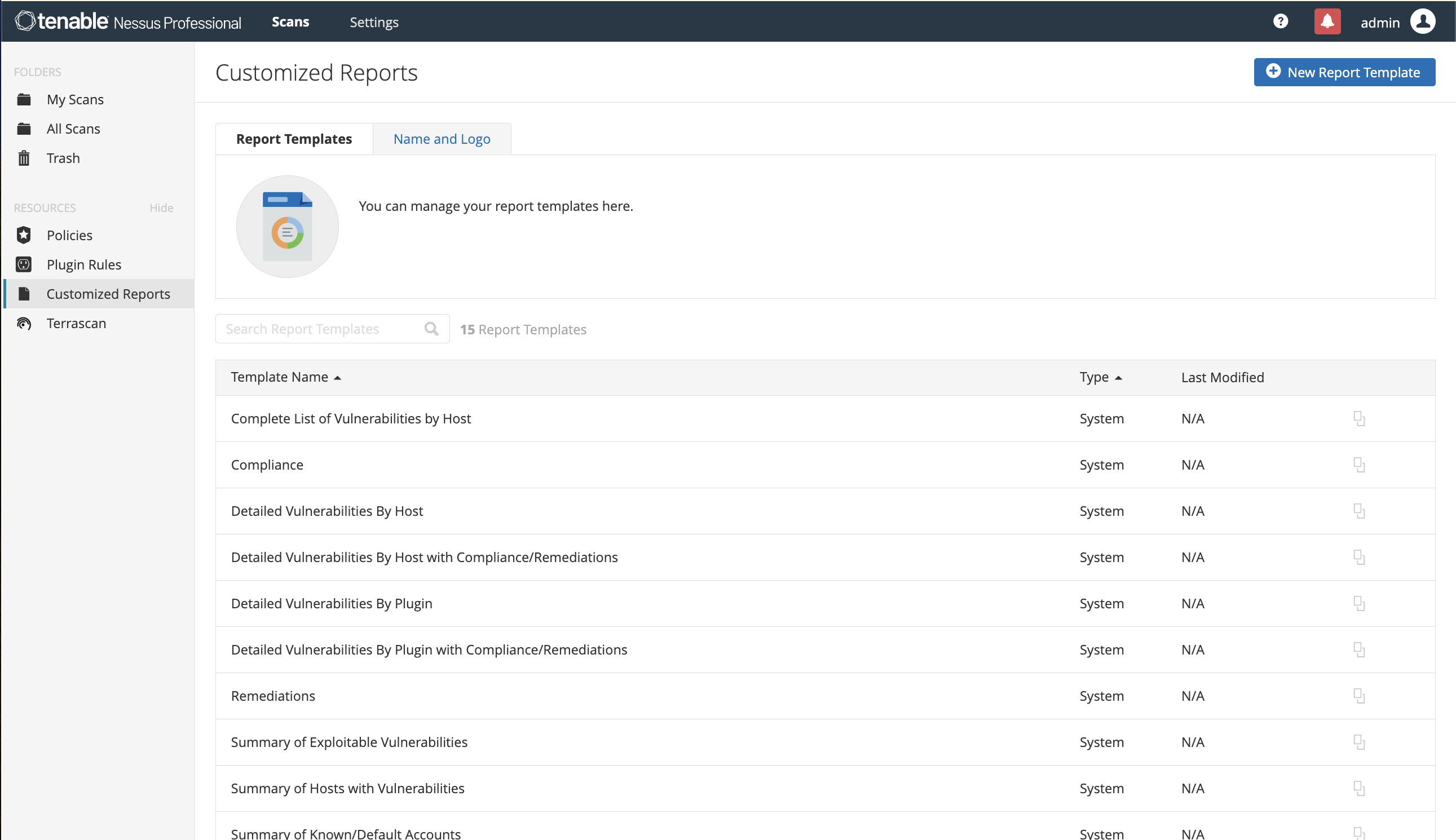
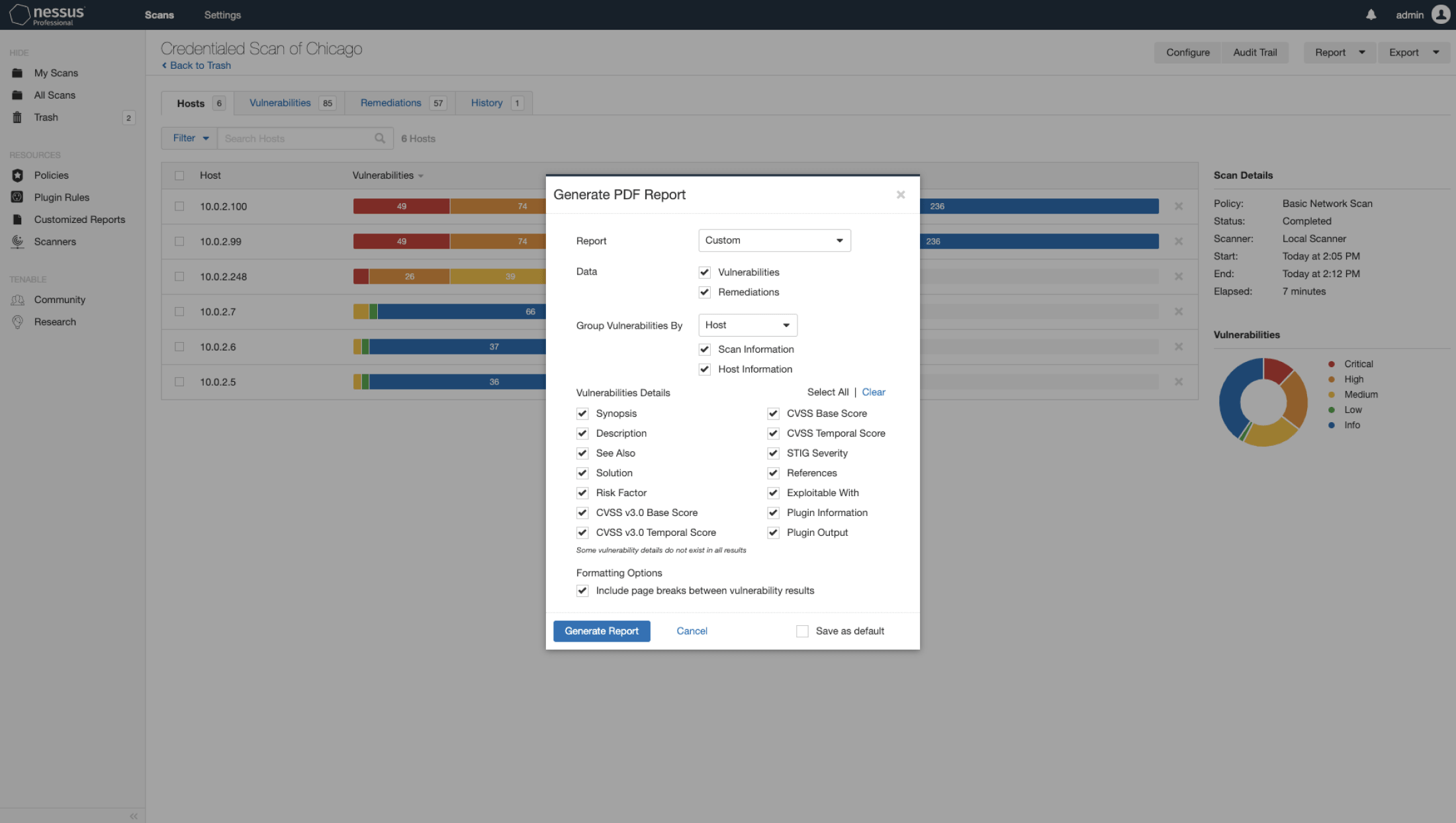
Cybersecurity consultants use Nessus to scour clients’ networks for vulnerabilities and create comprehensive reports that summarize security posture and contain key suggestions for remediation.
Read More
In years past, small and medium-sized businesses might have considered themselves effectively immune to cyberattacks.
Even the smallest companies that lack full-time cybersecurity staff can stay on top of vulnerabilities with Nessus, customizing comprehensive scans to meet unique business needs.
Read MoreTo learn more about Nessus features and functionality, visit our Nessus documentation page. To learn more about purchasing options, please contact your preferred reseller or visit our online store.
Nessus on-demand Training
Interested in learning how to use Nessus? Our on-demand course enables the student, pen tester, consultant and security practitioner, through a series of targeted videos, to develop the building blocks for effective use of the Nessus vulnerability assessment solution. From asset discovery to vulnerability assessment to compliance, participants will learn to effectively utilize Nessus in a variety of business use cases.
Learn More Buy Now for $250Course Topics
60+ targeted videos and demonstrations covering these topics:
- Introduction to Cybersecurity
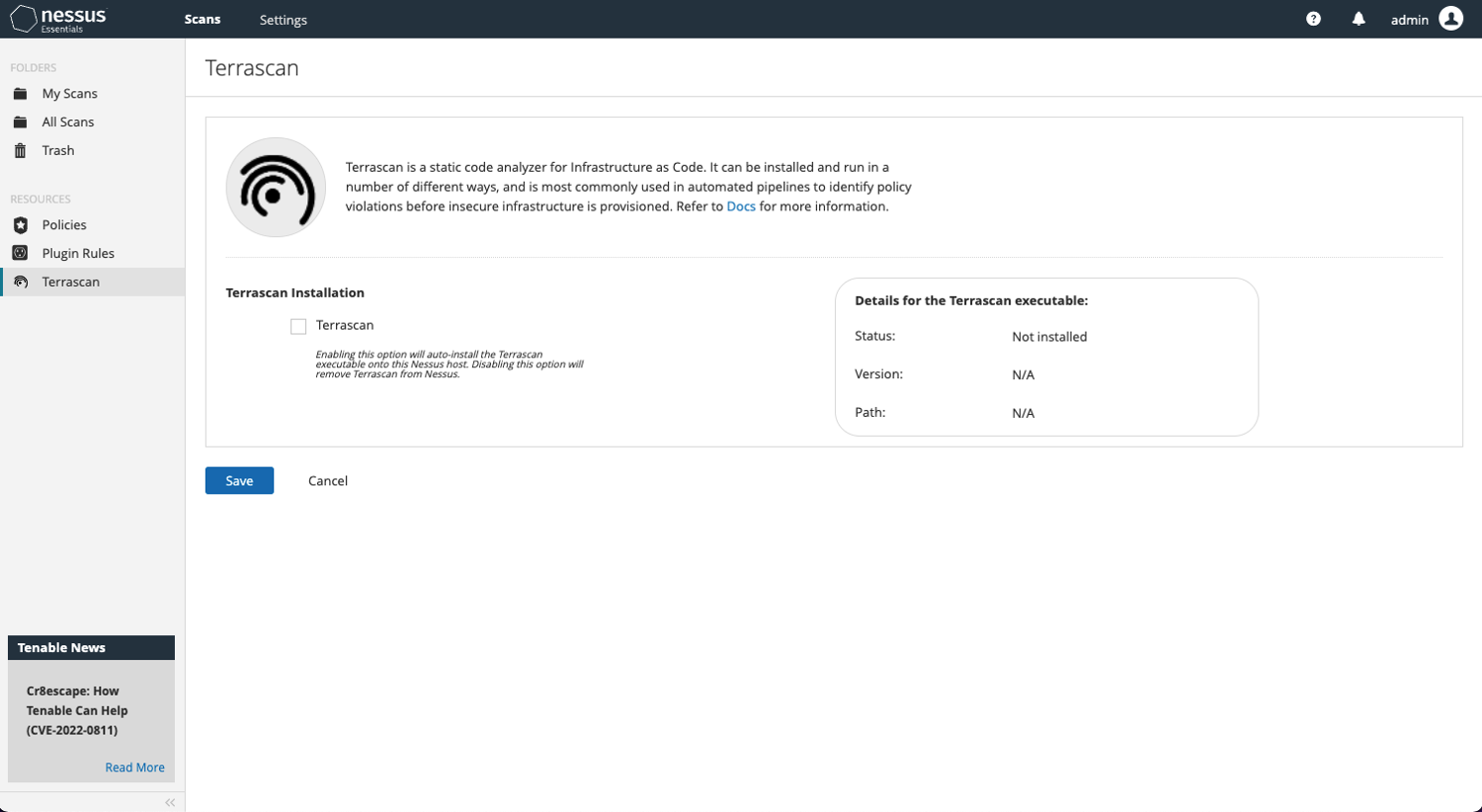
- Installation
- Configuration
- Vulnerability Assessment
- Compliance Assessment
- Analysis
Nessus Pro - Built for Security Professionals Like You
Get the world’s most widely deployed vulnerability assessment solution.