Tenable Integrates with Dell KACE Systems Management Solution
Nessus and SecurityCenter now integrate with the Dell KACE K1000 Systems Management appliances to identify missing patches on vulnerable systems, detect unmanaged systems, and extend scanning to cover systems that previously could not be scanned.
This integration expands Tenable’s strategy to bridge the gap between vulnerability scanning and patching by allowing administrators to scan targets directly or query endpoint management platforms including Windows WSUS and SCCM, IBM Tivoli Endpoint Manager, Red Hat Network Satellite, and Dell KACE. Administrators are able to prioritize vulnerable and unpatched systems for distribution of updates and hotfixes.
Dell KACE Background
The Dell KACE Systems Management appliance is a fully integrated systems management solution delivered as an appliance to ease deployment and management. Dell KACE Systems Management appliances are available as physical, virtual, and hosted appliances to manage a variety of systems including Linux, Windows, and Mac OSX.
How does it work?
Both Nessus and SecurityCenter can query Dell KACE K1000 appliances to verify if the systems managed by Dell KACE are patched to the latest version. Patch information can be viewed in both the Nessus and SecurityCenter GUI. The following use cases illustrate some of the integration capabilities:
- Identify and pinpoint vulnerable assets that are missing patches
- Identify systems not managed by Dell KACE
- Use data obtained from Dell KACE to perform checks when Nessus or SecurityCenter do not have credentials for scanning a target host
How do you configure it?
Configuring the KACE K1000 integration is easy:
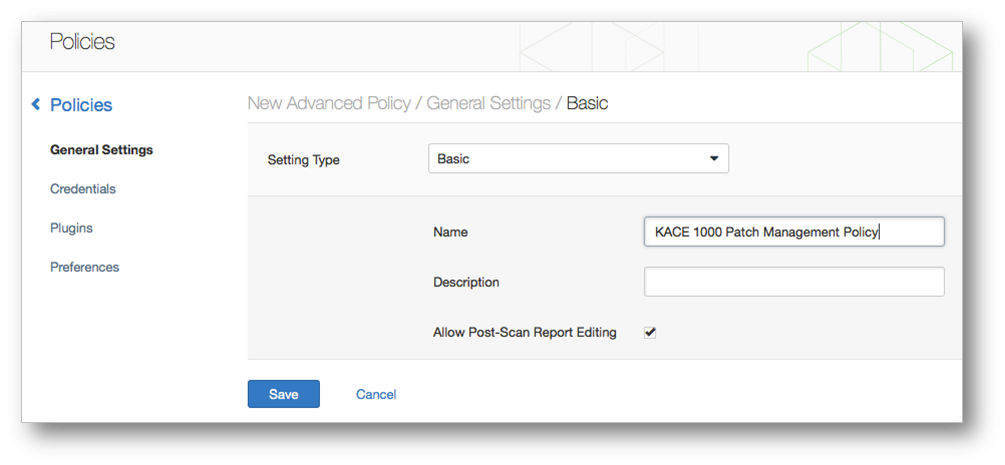
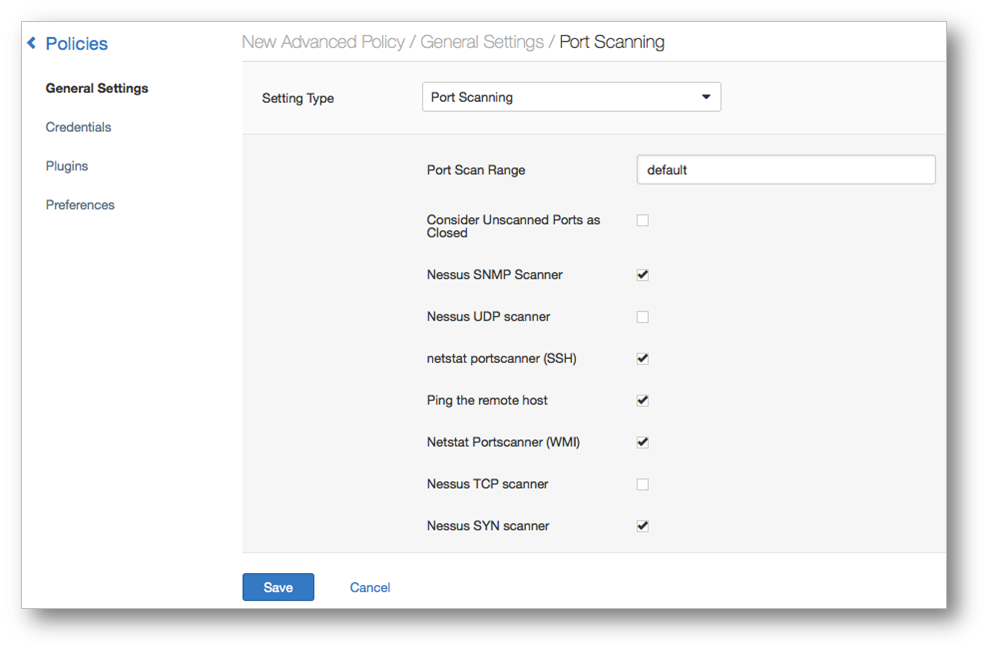
Step 1: Configure Policy/Settings.
- In the Nessus GUI, click “New Policies” and select the “Advanced Policy” tab.
- Select “General Settings”, select the scan type, and configure the port scanning parameters as shown below:
Step 2: Enable the four plugins listed below:
- dell_kace_k1000_get_computer_info.nbin ==> Script ID : 76867
- dell_kace_k1000_get_missing_updates.nbin ==> Script ID: 76868
- dell_kace_k1000_init_info.nbin ==> Script ID: 76866
- dell_kace_k1000_report.nbin ==> Script ID: 76869
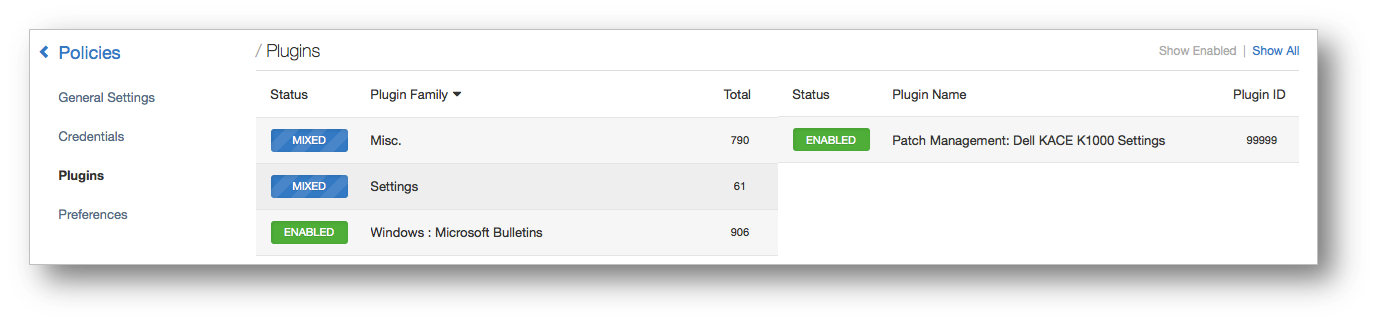
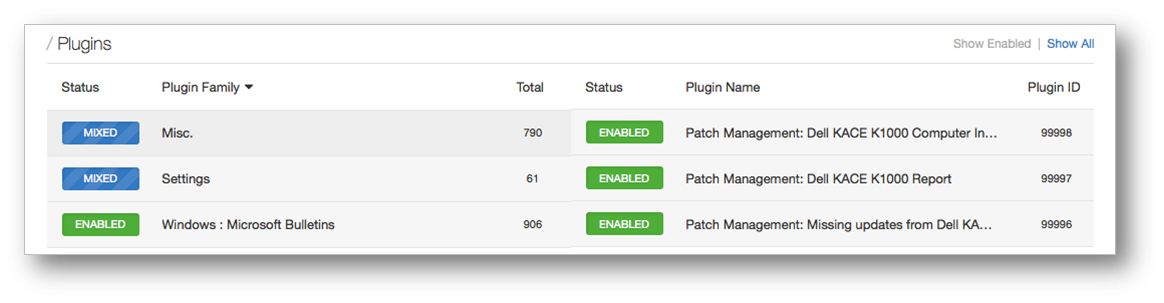
In addition to the KACE K1000-specific plugins, enable all plugins in the “Windows: Microsoft Bulletins” family.
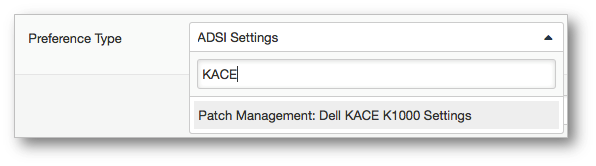
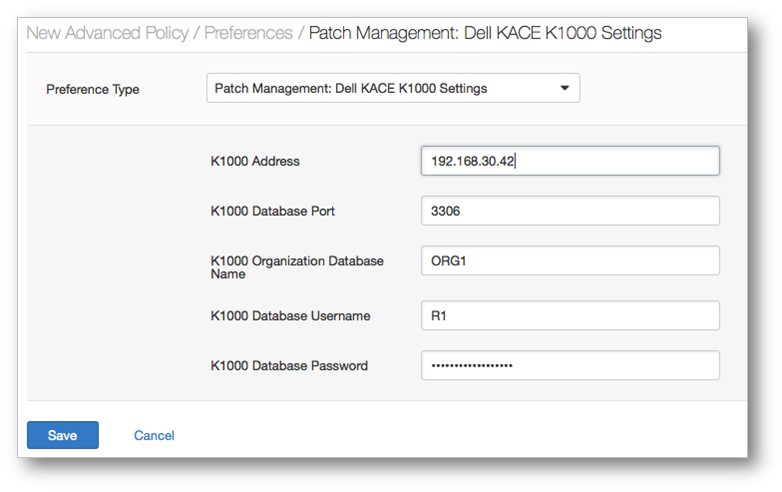
Step 3: Set Preferences
- Enter credentials for the Dell KACE K1000 from the “Preferences” and select “Patch Management: Dell KACE K1000 Settings”.
- Enter the appropriate Dell KACE K1000 server settings.
Integration Output:
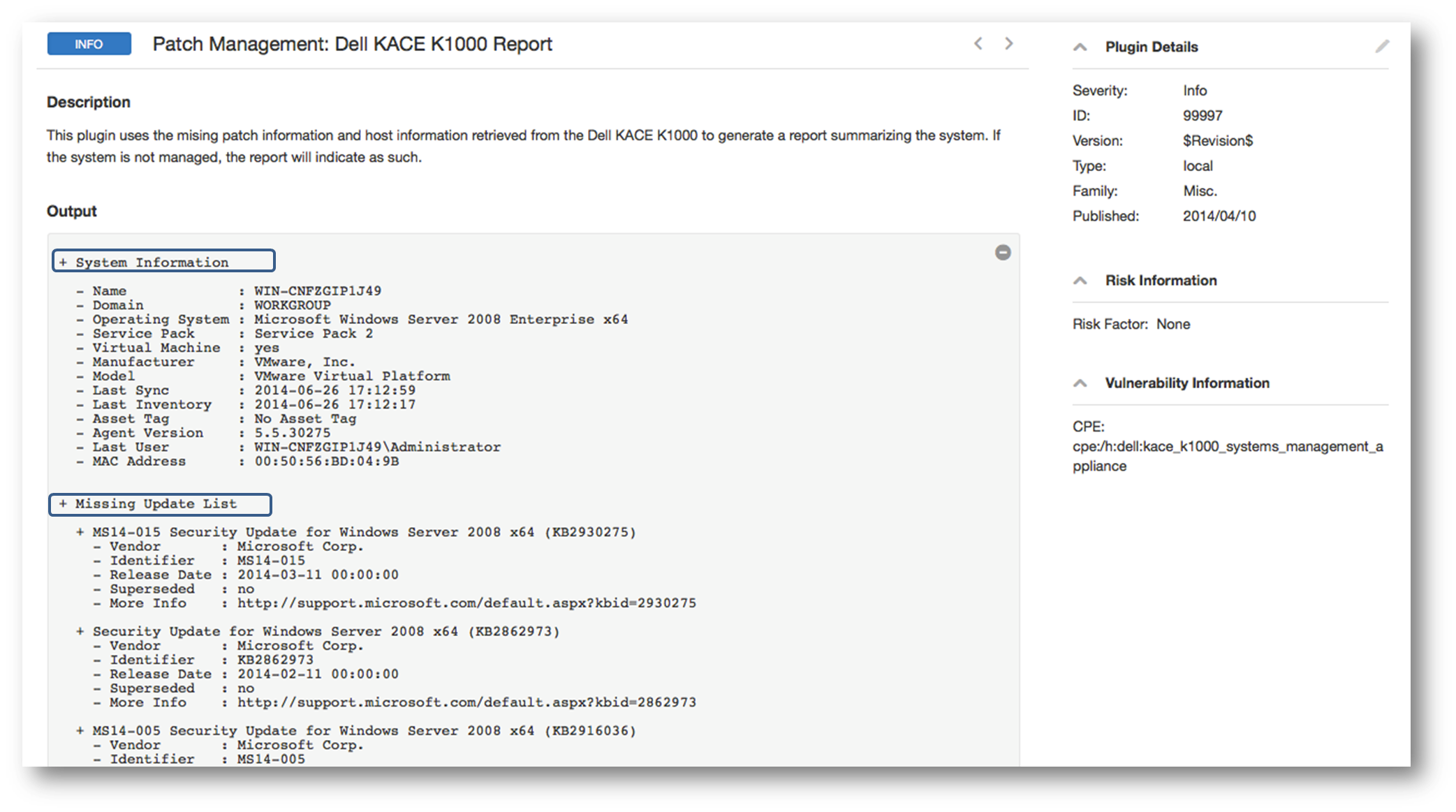
The following Nessus report provides host information retrieved from the Dell KACE K1000 along with missing patches.
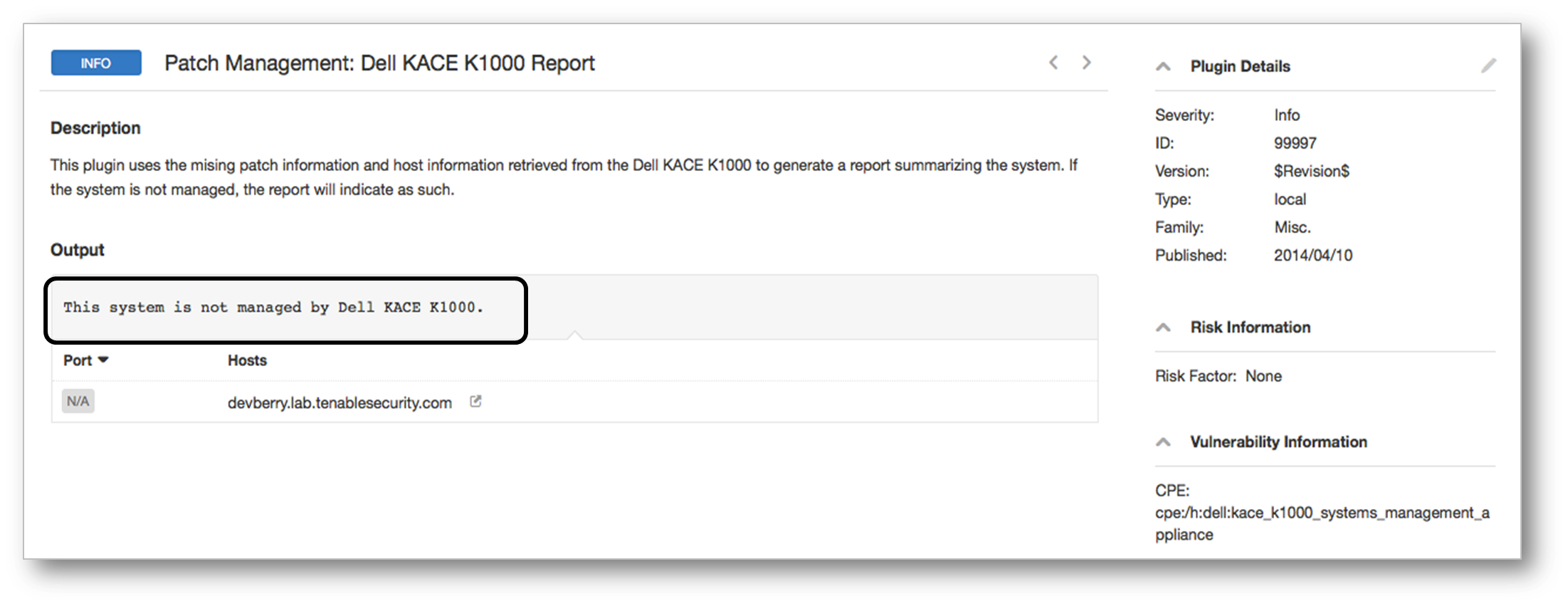
Nessus will also report systems the Dell KACE K1000 is not managing, enabling administrators to bring those systems under management (or simply ensure that they are appropriately patched).
Conclusion
Organizations can reduce risk by identifying vulnerable assets and systematically patching those systems. By integrating vulnerability management with systems management platforms, Tenable Nessus and SecurityCenter enable administrators to identify what’s vulnerable and prioritize their patch remediation.
To learn more about Tenable’s patch management support, visit our patch auditing solutions page. To learn more about real-time monitoring of the patch and compliance auditing of IT assets, check out SecurityCenter Continuous View.
Related Articles
- Announcements
- Integrations
- Nessus
- Patch Auditing
- SecurityCenter








