SecurityCenter 4.6.2 Provides Enhanced CyberScope Monitoring and Reporting
Note: Tenable SecurityCenter is now Tenable.sc. To learn more about this application and its latest capabilities, visit the Tenable.sc web page.
With the release of SecurityCenter 4.6.2, Tenable has added to its CyberScope monitoring and reporting capabilities by enabling federal organizations to easily report on information about assets and exchange security assessment results and device inventories of multiple IT assets at an aggregate level.
CyberScope LASR reporting
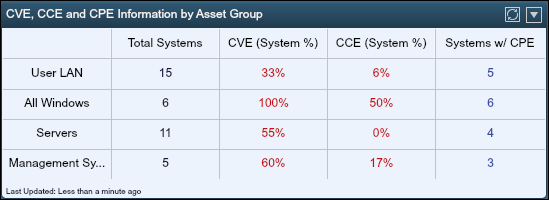
SecurityCenter-CV now includes integrated support for CVE and CPE vulnerabilities and is the only solution that provides consolidated CPE, CVE, and CCE feeds.
Previously, the passive sniffing capability of PVS uniquely detected vulnerabilities with CVE identifiers and CPE information for assets throughout the network. As a result, SecurityCenter-CV made monitoring and reporting efforts easier and more accurate than with just pure scanning alone.
SecurityCenter can now generate a CyberScope/LASR directly from the application. Previously, generating a CyberScope report required the xTool utility to connect to SecurityCenter, pull the data, and then generate the report. With this release, users can publish CyberScope and all other reports directly from SecurtyCenter.
In addition, two new reports are now available to support CyberScope projects:
Asset Reporting Format (ARF)
The ARF report defines a data model used against assets (i.e., computing device), asset identification information, and the relationship between the two. A few examples of an ARF report generated by SecurityCenter are:
Parent level organization of the asset Child organization name of the asset Sub-children of the asset Person Geo-Location The role of the ARF is to gather and identify the assets on the network and then tag particular attributes to those assets. This is done in order to later associate vulnerability and other types of information generated in other reports against these assets.
Assessment Summary Results (ASR)
SecurityCenter can now generate ASR reports which are designed to exchange vulnerability results of multiple assets at the aggregate level. While ARF documents contain very detailed information about few assets, ASR reports contain summarized information about many assets for a single vulnerability. Examples of what is generated in an ASR report by SecurityCenter:
- CCE info
- IAVM info
- CVE
- PluginID
By parsing both ARF and ASR reports, customers can use their own methods of tracking and mitigating vulnerable hosts across their organization. They can also pull in reports generated by other tools and parse that against what SecurityCenter is providing them.
Conclusion
These enhancements provide better metrics, improved knowledge of security posture, and more complete and accurate information about each asset for CyberScope initiatives.
Related Articles
- SecurityCenter
- Vulnerability Management







