New Scan Policies, Plugins and Dashboard for CVE-2016-0800: DROWN

No matter which product you have, Nessus®, SecurityCenter™, SecurityCenter CV™, or Passive Vulnerability Scanner™, Tenable can determine if you are at risk of “drowning.”
The DROWN CVE-2016-0800 vulnerability is a cross protocol vulnerability that enables an attacker to decrypt TLS connections between up-to-date clients and servers by sending packets to any server that supports SSLv2 using the same private key.
The DROWN vulnerability’s impact is made worse by two additional OpenSSL implementation vulnerabilities:
- CVE-2015-3197, which allows a DROWN attacker to connect to the server with disabled SSLv2 ciphersuites, provided that support for SSLv2 itself is enabled
- CVE-2016-0703, which greatly reduces the time of carrying out the DROWN attack
According to drownattack.com, at the time of vulnerability publication on March 1, 33% of all HTTPs sites were affected by this vulnerability. More information on DROWN severity is available in the OpenSSL advisory issued on March 1.
The Tenable Response
Nessus
Impacted operating system vendors are making updates available, and Tenable has released a new Nessus scan policy template specifically for DROWN.

We have also issued a series of local and remote Nessus® plugins to detect the presence of affected versions of OpenSSL:
SecurityCenter
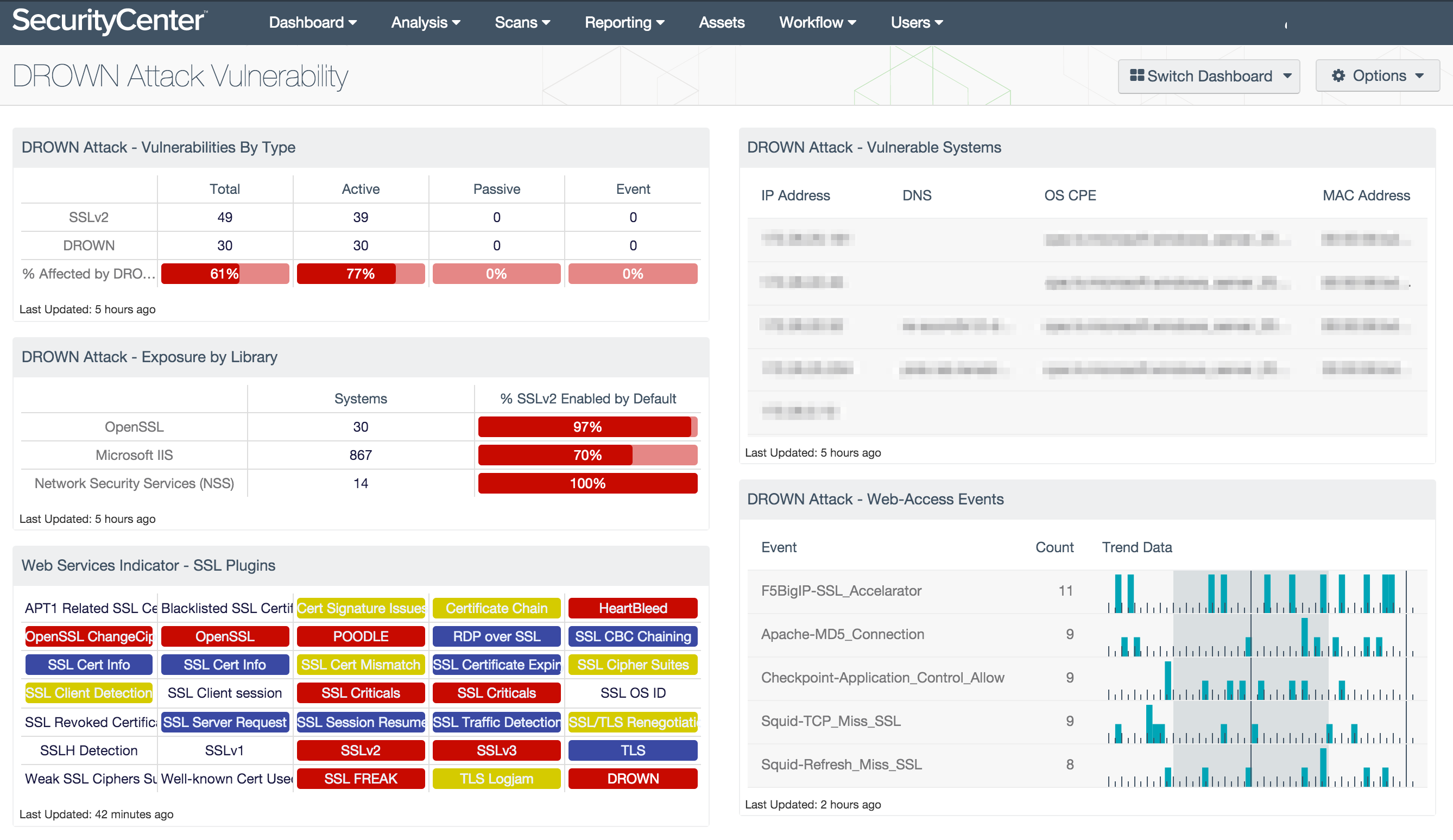
We have released a customized SecurityCenter™ dashboard to monitor, track and remediate critical assets affected by CVE-2016-0800. This dashboard is automatically available via the feed to provide insight on the impact to your environment and the progress of your efforts to remediate this vulnerability.
Passive Vulnerability Scanner
Note: Passive Vulnerability Scanner (PVS) is now Nessus Network Monitor. To learn more about this application and its latest capabilities, visit the Nessus Network Monitor web page.
The following plugins address DROWN:
| Title | ID |
|---|---|
|
SSLv2 Cross-Protocol Session Decryption Vulnerability (DROWN) |
|
|
OpenSSL 1.0.1 < 1.0.1s / 1.0.2 < 1.0.2g Multiple Vulnerabilities (DROWN) |
Related Articles
- Dashboards
- Nessus
- Nessus Network Monitor
- Plugins
- SecurityCenter








