Hiding In Plain Sight: Discovering Legacy Applications Using PVS
Note: Passive Vulnerability Scanner (PVS) is now Nessus Network Monitor. To learn more about this application and its latest capabilities, visit the Nessus Network Monitor web page.
Hiding in Plain Sight
Finding the pockets of your network that contain hidden systems or applications is an ongoing task for every IT security department. It seems no matter how well you know your network, there is frequently something that causes you to raise an eyebrow and investigate. There are a few contributing factors that lead to pockets of unmanaged systems and applications:
The owner of the system does not want IT to find it
Often the user of the application knows they are running older operating systems and applications. They fear the process of updating as it may cause disruptions in services or their ongoing work. Of course, you as the security representative in the organization should not breed a culture of fear, but offer help in securing and moving applications to the latest versions and more secure platforms. This is often not an easy task, and requires collaboration with various teams and a solid plan for legacy application migration.
Nessus does not have credentials
Since you may have no knowledge of certain systems or applications, you likely do not have credentials. Without a credentialed audit, it is difficult to identify and determine if client software is outdated and/or vulnerable.
There is a local firewall blocking network scans
We often have to deal with legacy applications, and sometimes people take security into their own hands. This could mean the application has been firewalled off from the rest of the network, making it difficult for your scanners to detect and enumerate vulnerabilities.
Scanning may find vulnerabilities, but it’s difficult to enumerate applications
One of the difficulties associated with web application vulnerability scanning is knowing where all of the applications are located. If you do not know how to access the application, it is nearly impossible to enumerate vulnerabilities. For example, someone may install a vulnerable application in "/mycoolwebapp" and unless you know to go there, the application will not be scanned. There are ways to discover it; for example, if the application links to another page you've crawled. However, they can still be tricky to enumerate. Another example is an application protected by credentials not known by your scanner, the application will not be scanned.
PVS to the Rescue!
First, let’s talk sensor placement. My goal is to enable the discovery of internal applications that are lacking updates and/or are vulnerable. With the Passive Vulnerability Scanner (PVS), I get a bonus: PVS detects the primary application, and secondary applications running with it are detected as well. In the case of a web application, PVS finds the web application (primary) plus the browser (secondary) and any helpers like Flash or Java. The sensor must see the traffic on the internal network to catch this, such as an uplink between core switches, or mirrored VLAN traffic from the internal network. For example, if your servers are on a specific subnet, this is a good VLAN to monitor. You could also go the other way, and if your clients are on specific subnets, mirror the traffic from those VLANs to a PVS sensor.
Once you've got PVS targeted, you can monitor for vulnerabilities. I was using a controlled environment, and right away I noticed some interesting results:
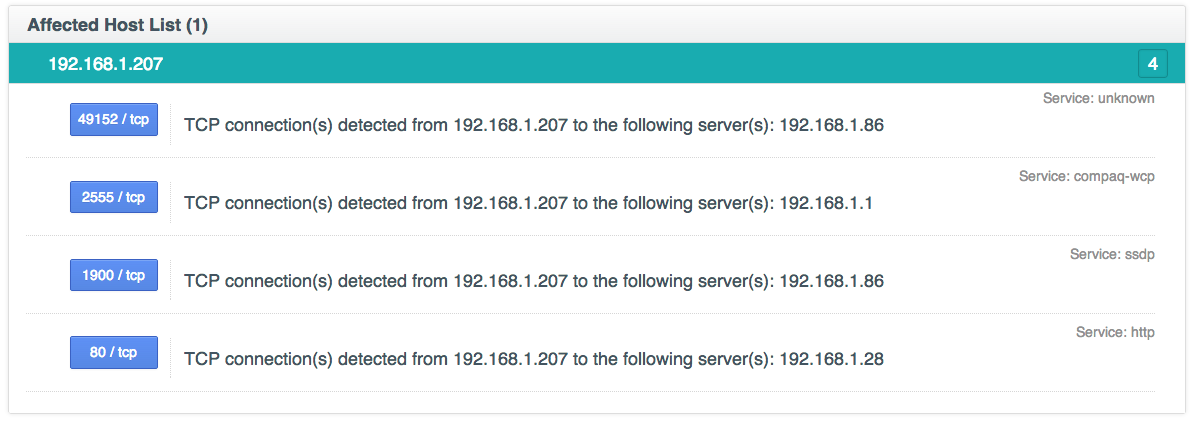
From the given list of vulnerabilities, the host is running a much older version of Firefox than the latest, in addition to the Flash Player. I'm really curious where this host is connecting; particularly, to which hosts on my internal network is it connecting? Fortunately, PVS creates a list of Internal Client Trusted Connections:
Looks like one host in particular received the HTTP connections: 192.168.1.28. Digging back into PVS, let’s review any vulnerabilities discovered for this host:
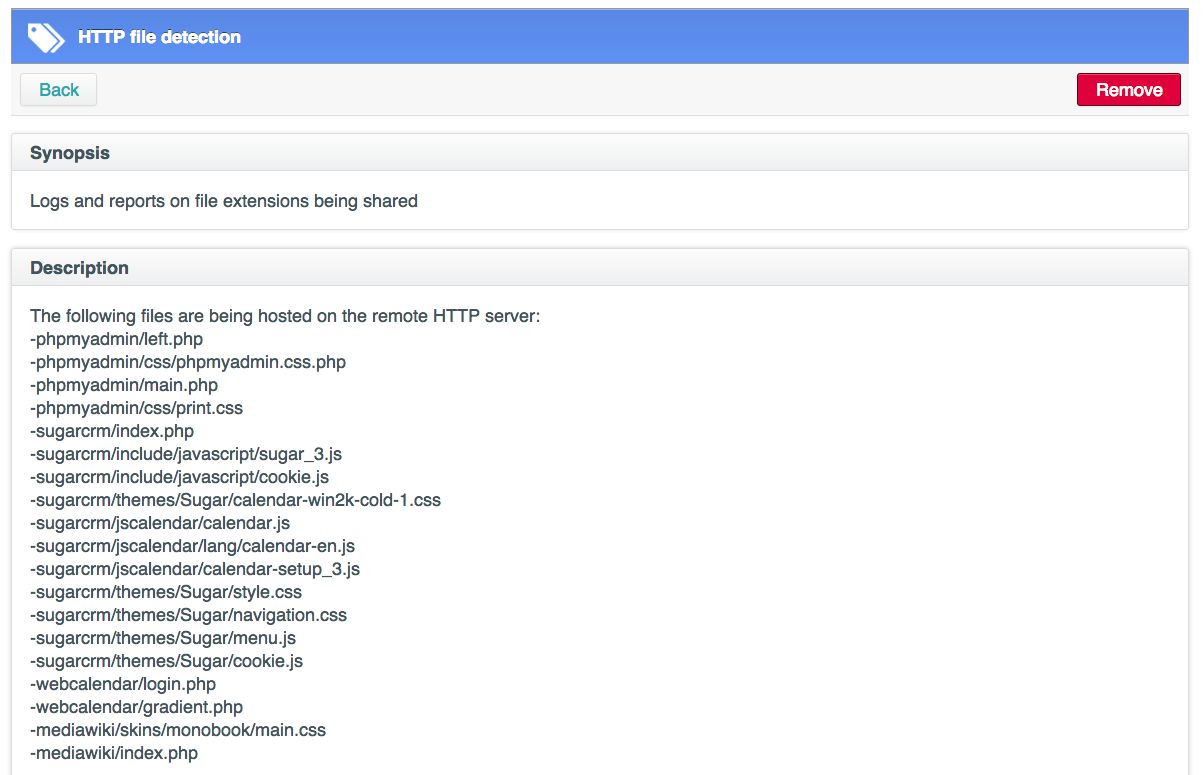
Yikes! Several older versions of PHP, Wordpress, and PHPMyadmin were discovered. At this point you may say, "But wait, I scanned this host with Nessus, and I couldn't find all those applications." With web application scanning, you have to know where to look. Applications can hide inside directories, behind authentication, and be attached to select vHosts. PVS to the rescue again! Since PVS is sniffing the traffic, we can review the HTTP file detection plugin and review the list of applications, and in this case their locations on the web server:
Conclusion
The Passive Vulnerability Scanner helps customers identify the "unknowns" on the network. Whether it’s a vulnerable web client or vulnerable web application, sniffing the network traffic will uncover such vulnerabilities (provided proper network placement). While web applications can hide from network vulnerability scans, passive detection and enumeration continues to be the key to uncovering vulnerable or legacy applications in your environment.
PVS is available to try yourself with an evaluation. PVS is now available with introductory pricing.
Related Articles
- Nessus Network Monitor
- Passive Network Monitoring
- Vulnerability Scanning